Deterministic Large Scale NAT44
This chapter provides information about deterministic large scale NAT44 configurations.
Topics in this chapter include:
Applicability
This chapter was initially based on SR OS Release 11.0.R3, but the MD-CLI in the current edition corresponds to SR OS Release 25.7.R2.
Overview
Deterministic Network Address Translation (NAT) is a mode of operation where mappings between the NAT subscriber and the outside IP address and port range are allocated at the time of configuration. In deterministic NAT for Large Scale NAT IPv4-to-IPv4 (LSN44) subscribers, each LSN44 subscriber is permanently mapped to an outside IP address and a dedicated deterministic port-block based on a specific algorithm. Logging is not needed in this case because the reverse mapping can be obtained using the reverse of the preceding algorithm.
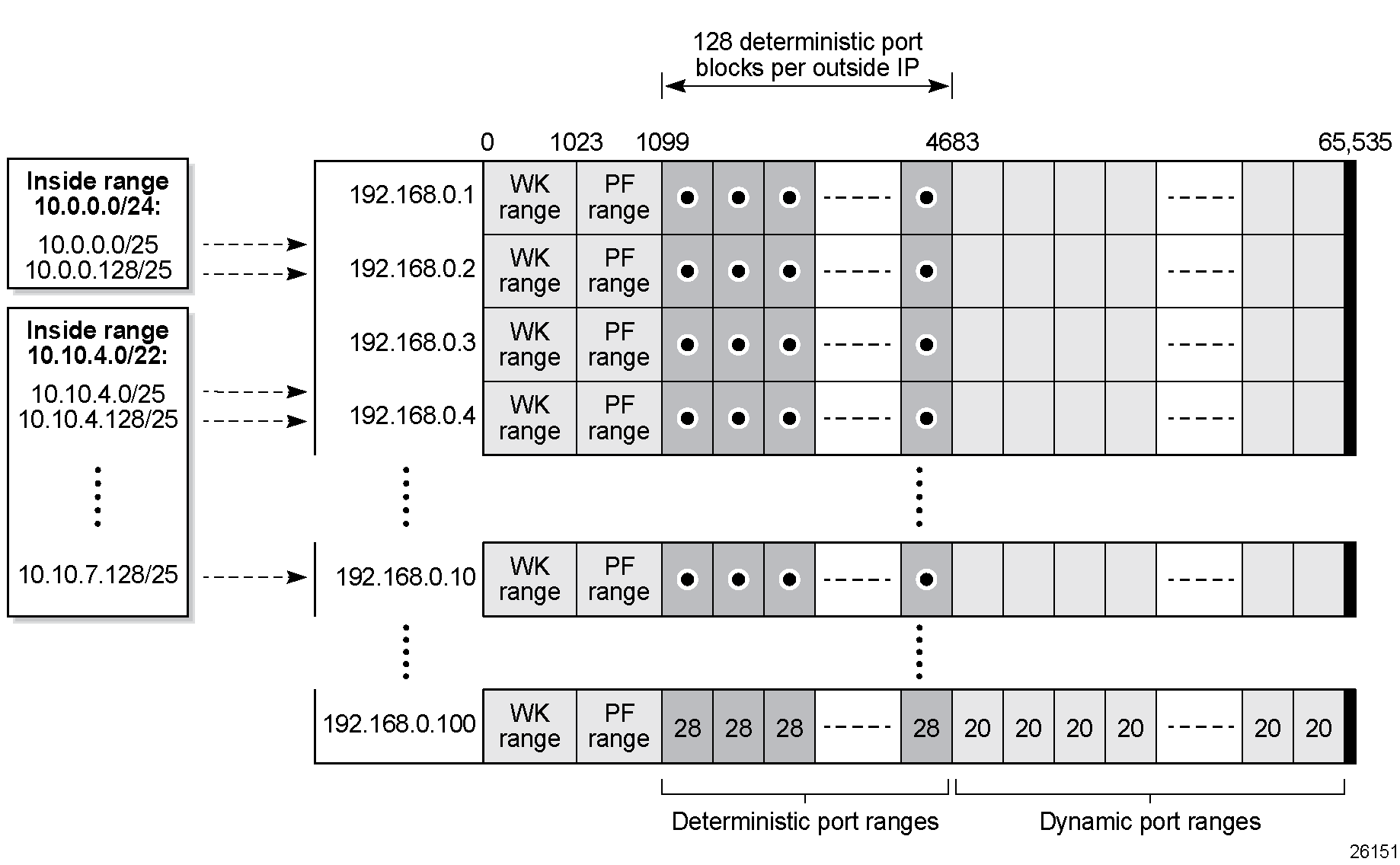
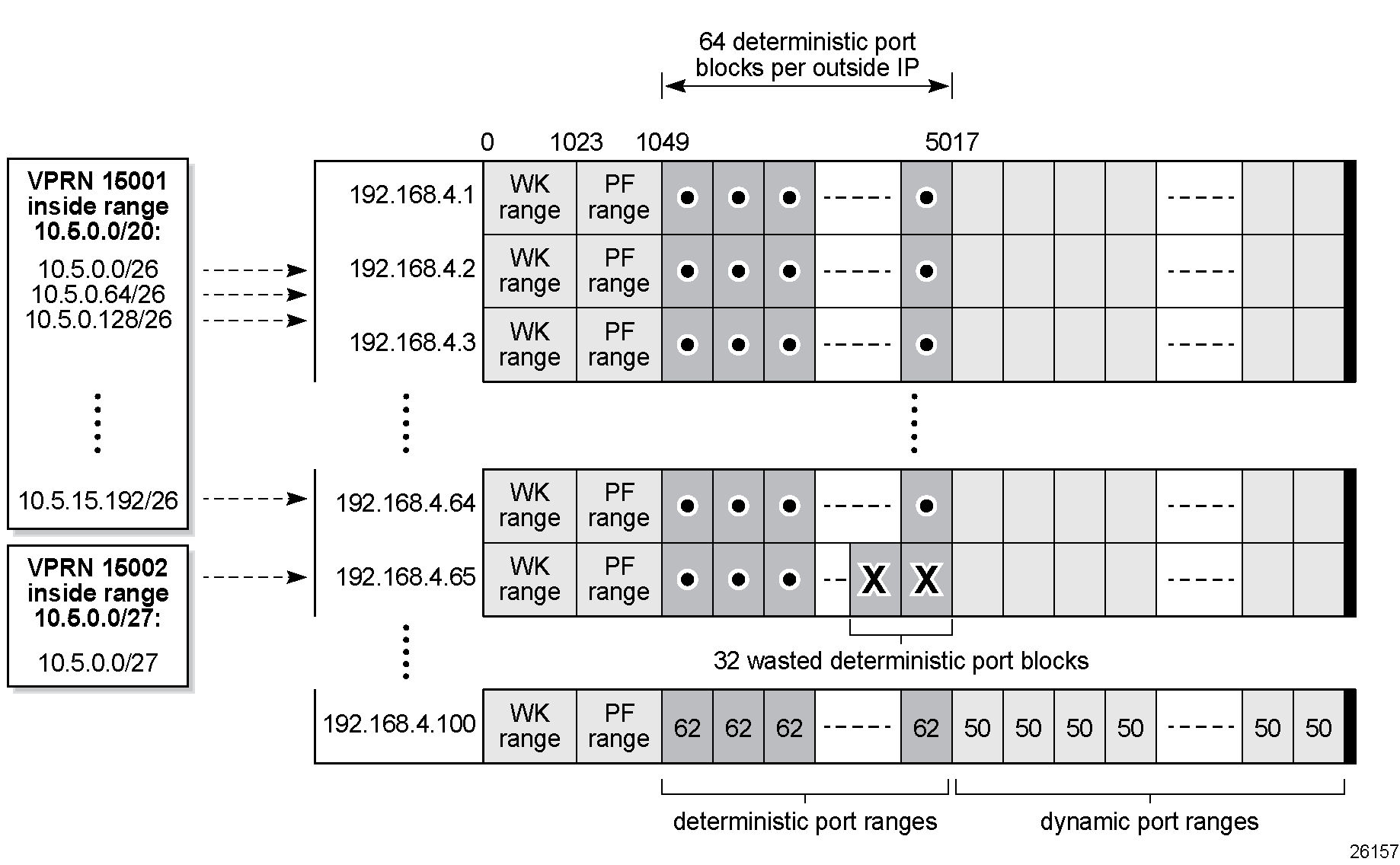
Deterministic NAT mapping shows the mapping between inside IP addresses and outside IP addresses, where the deterministic port blocks use the port range after the static port forwarding range. A deterministic LSN44 subscriber can have only one deterministic port block that can optionally be extended by one or multiple dynamic port blocks in case all ports in deterministic port block are exhausted.
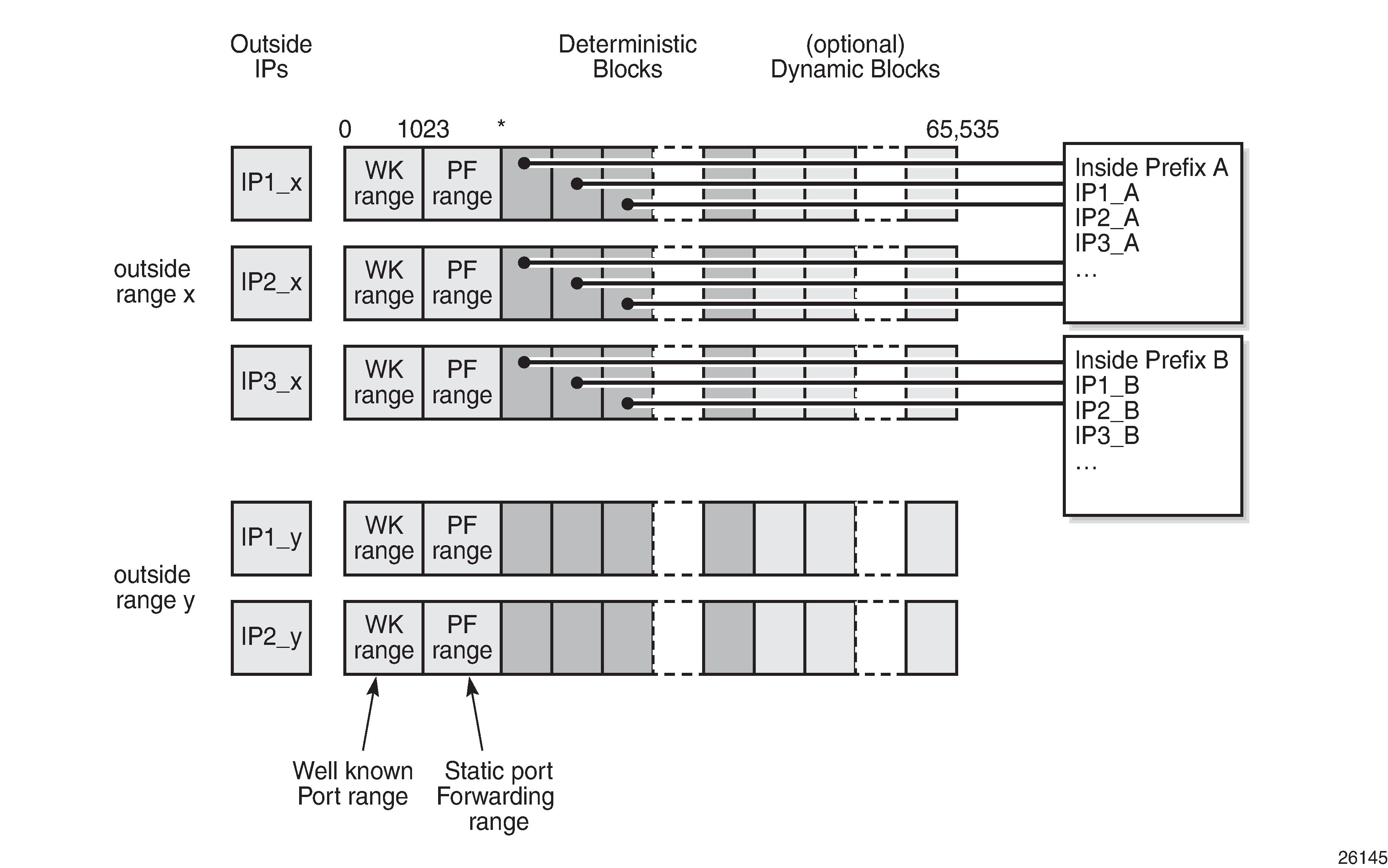
In case an LSN44 subscriber has been assigned both deterministic and dynamic port blocks, logging for the dynamic port block allocation and de-allocation is required. A scalable logging solution for dynamic port blocks is achievable using RADIUS or IPFIX. Logging for dynamic port blocks is out of the scope of this chapter.
Algorithm
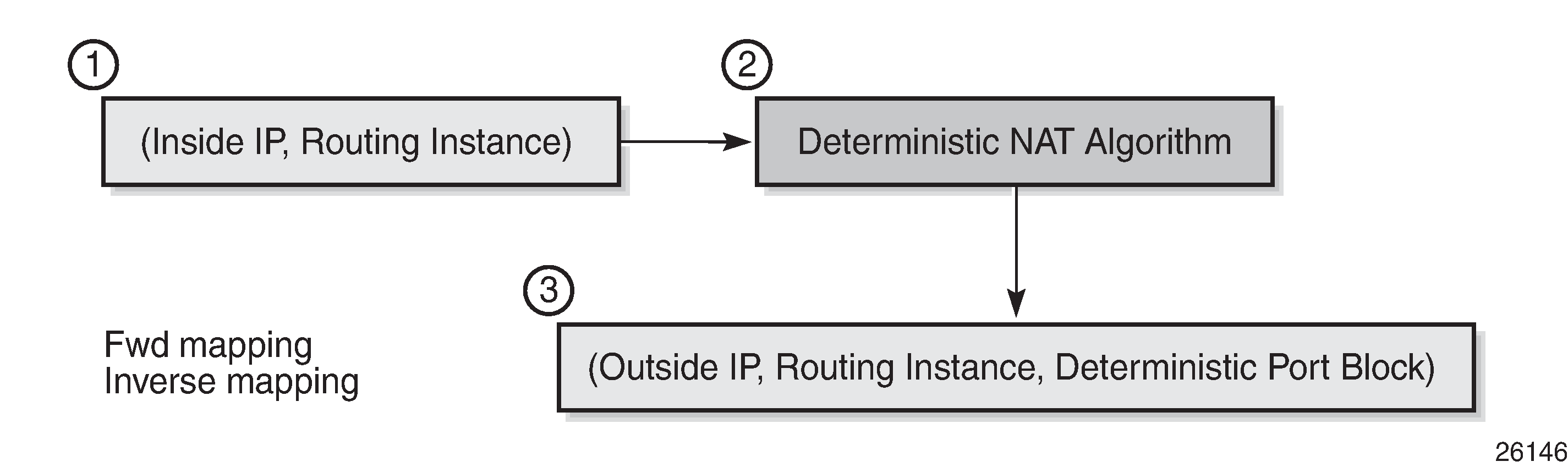
The deterministic NAT algorithm makes a predictable mapping between the (inside IP, routing instance) and the (outside IP, routing instance, deterministic port block), as shown in Deterministic NAT algorithm. The algorithm is revertive, meaning that a specific (outside IP, routing instance, deterministic port block) derives a specific (inside IP, routing instance).
The algorithm is loosely based on draft-donley-behave-deterministic-cgn-00, which allows for the dynamic expansion of the port blocks when the ports in the original deterministic port block are exhausted.
Deterministic mapping
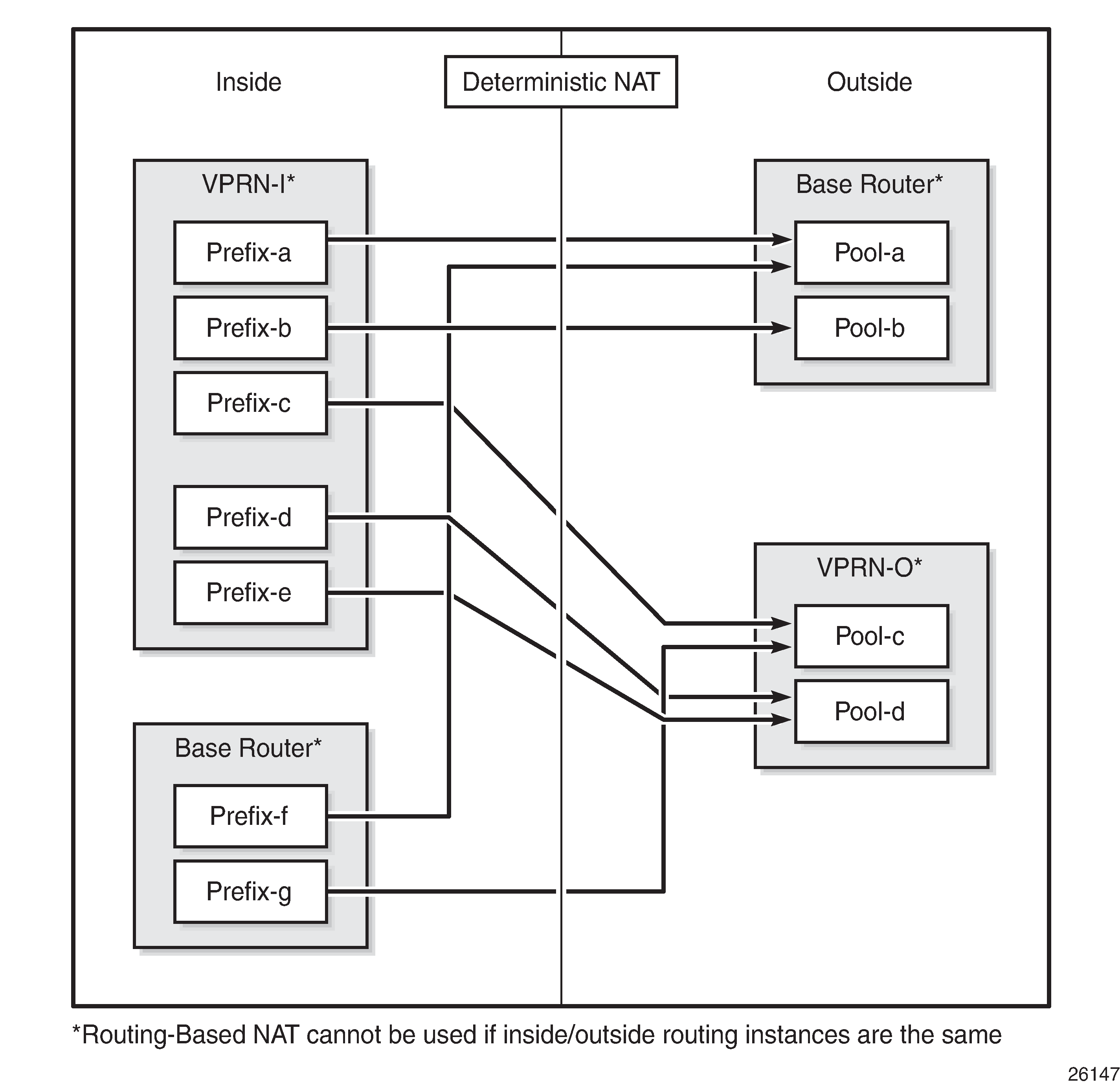
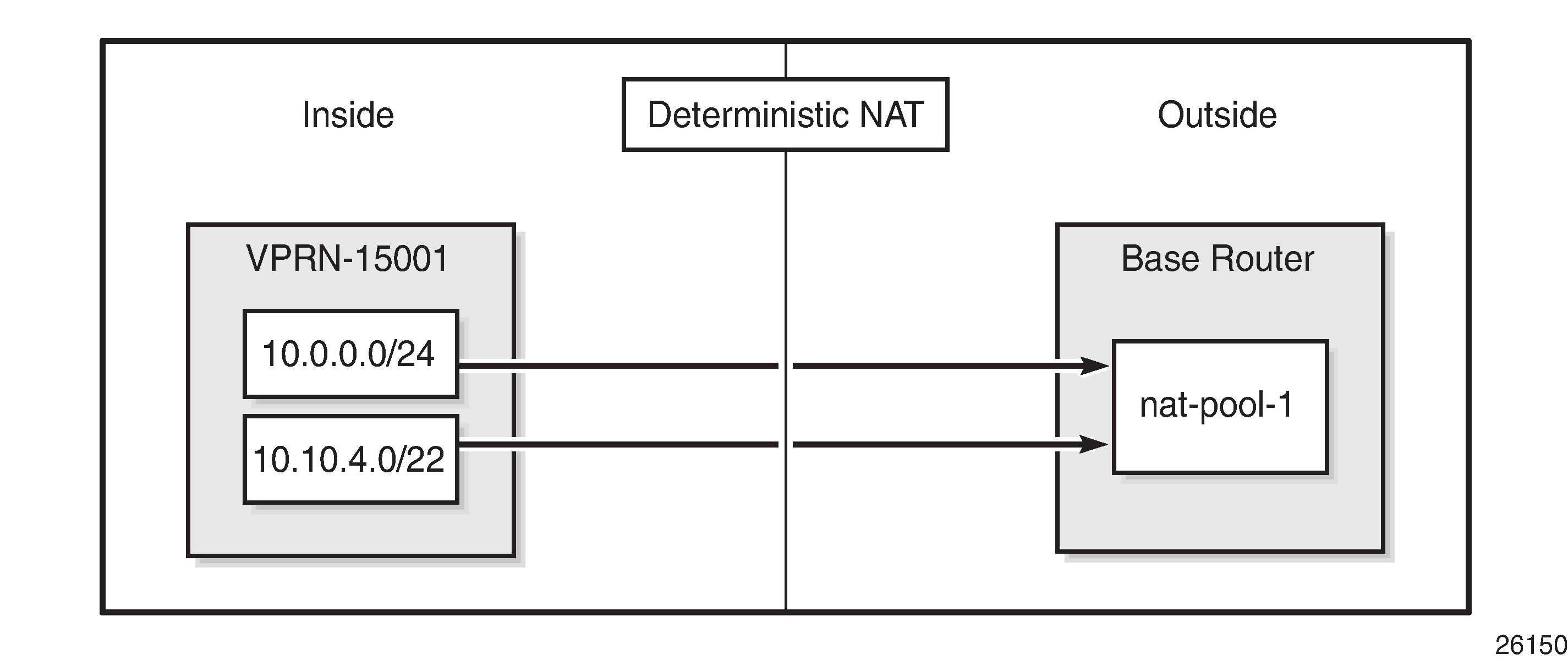
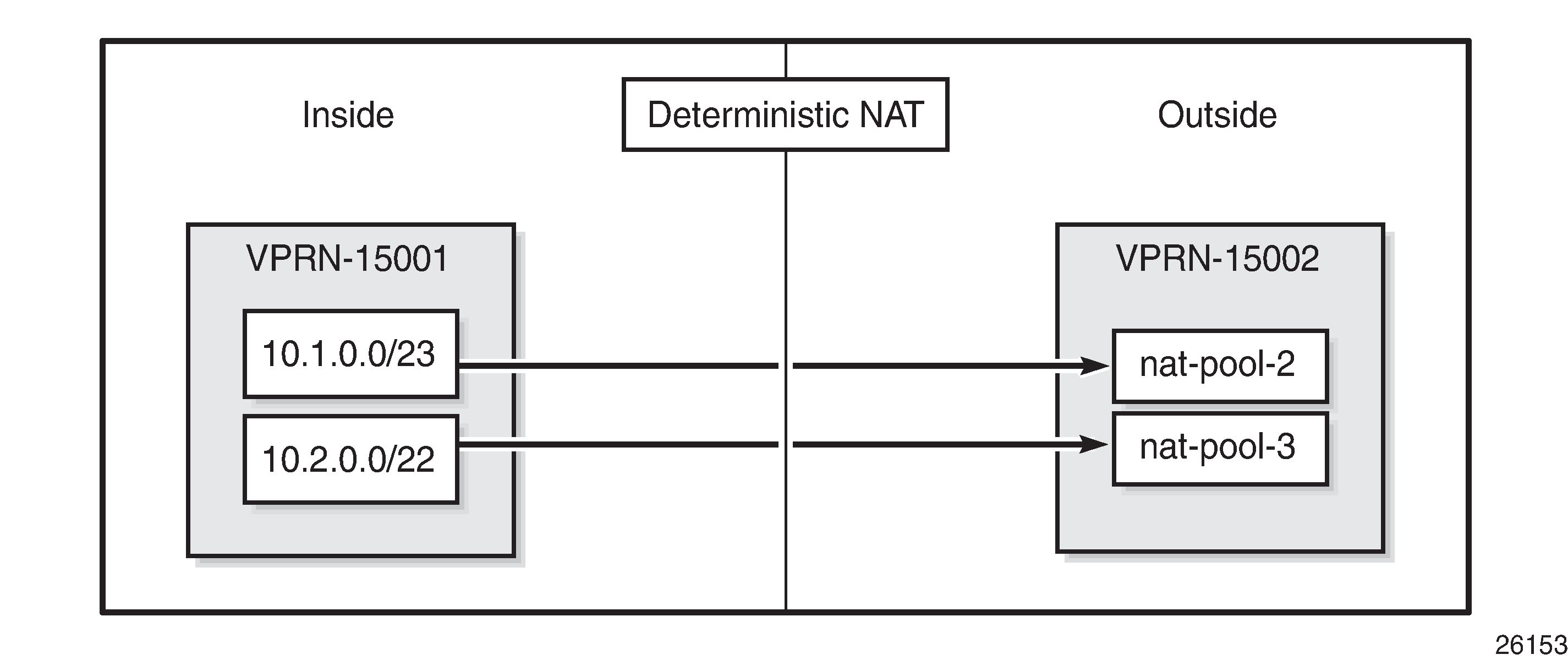
Any inside prefix in any routing instance can be mapped to any pool in any routing instance.
In deterministic NAT, prefixes from multiple routing instances can be mapped to the same outside pool, also prefixes from a single inside routing instance can be selectively mapped to different outside pools, as shown in Deterministic mapping: inside -> outside routing instances .
Mapping rules
A deterministic LSN44 subscriber is mapped to only one deterministic block which can further be extended to multiple dynamic blocks if ports within the deterministic block are exhausted.
The subscriber limit is the number of subscribers that can be deterministically mapped to one outside IP address (that is, compression ratio) and must be a power of 2.
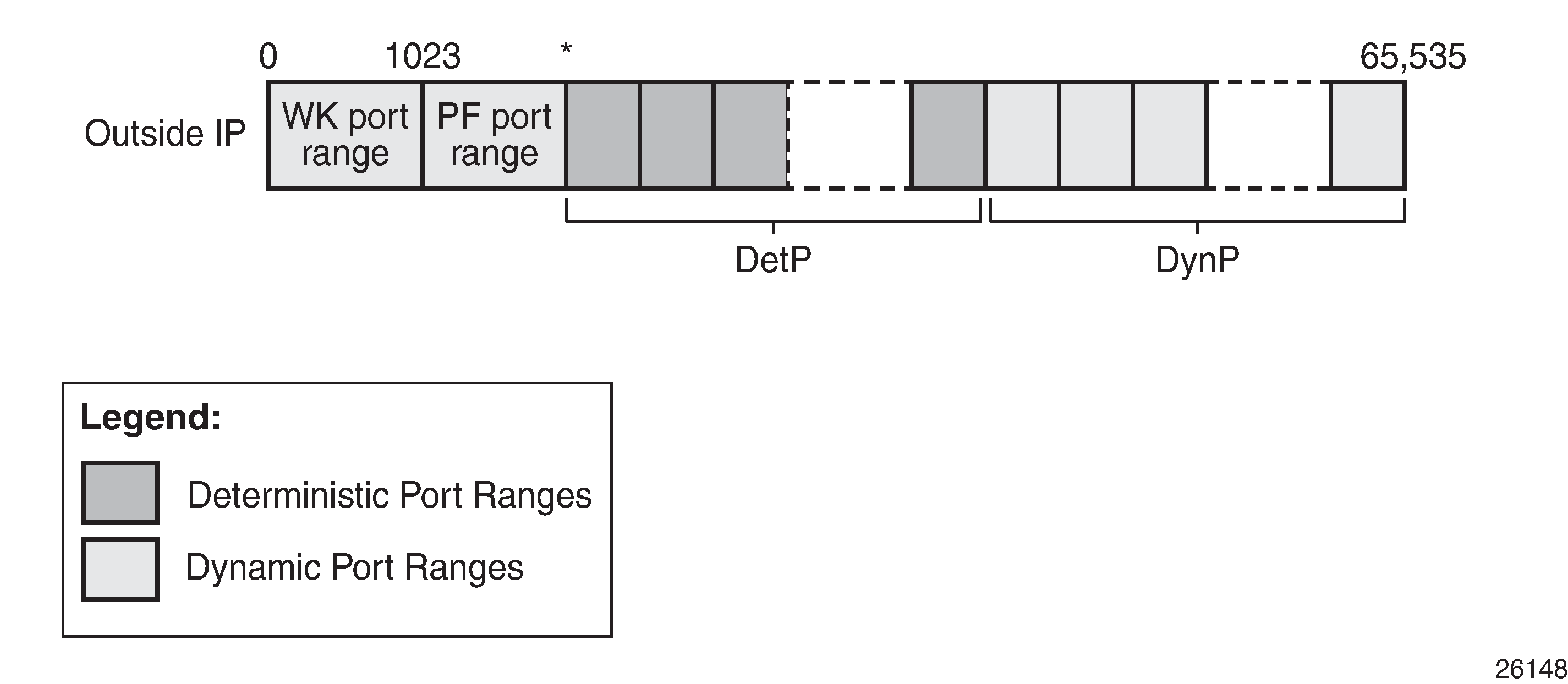
The total number of deterministic ports (DetP) per outside IP address is determined by this subscriber limit and the number of deterministic ports per subscriber.
The remaining ports (DynP) beyond the deterministic port range up to 65535 are dedicated for dynamic use when a deterministic block is exhausted.
Every host using an inside prefix is guaranteed one dedicate block in the deterministic port ranges.
If the inside prefix length is m < 32-n, where 2^n=subscriber limit, then the prefix must be broken into pieces so that all hosts (subscriber limit) in each piece maps exactly to one outside IP address.
For example, if there is an inside prefix 192.168.0.0/23, with m=23 and a maximum number of 256 hosts; and the subscriber limit set to 256, then n=8. This results in 23 < 24 (32-8) and so this inside prefix must be broken into 2 pieces, in other words, this inside prefix fits into 2 outside IP addresses, each of 256 port blocks.
In case that the prefix length is m ≥ 32-n, where 2^n=subscriber limit, then all hosts from the configured prefix are mapped to the same outside IP.
For example, if there is an inside prefix 192.168.1.0/25, with m=25 and a maximum number of 128 hosts, and the subscriber limit set to 256, then n=8. This results in 25 > 24 (32-8), so definitely 128 hosts can fit in one outside IP because there are 256 available port blocks, in other words, this inside prefix fits into one outside IP where 128 blocks have been used out of the 256 port-blocks available, and the remaining 128 ports are wasted.
Overbooking of the outside address pool is not supported in deterministic NAT.
Configuration
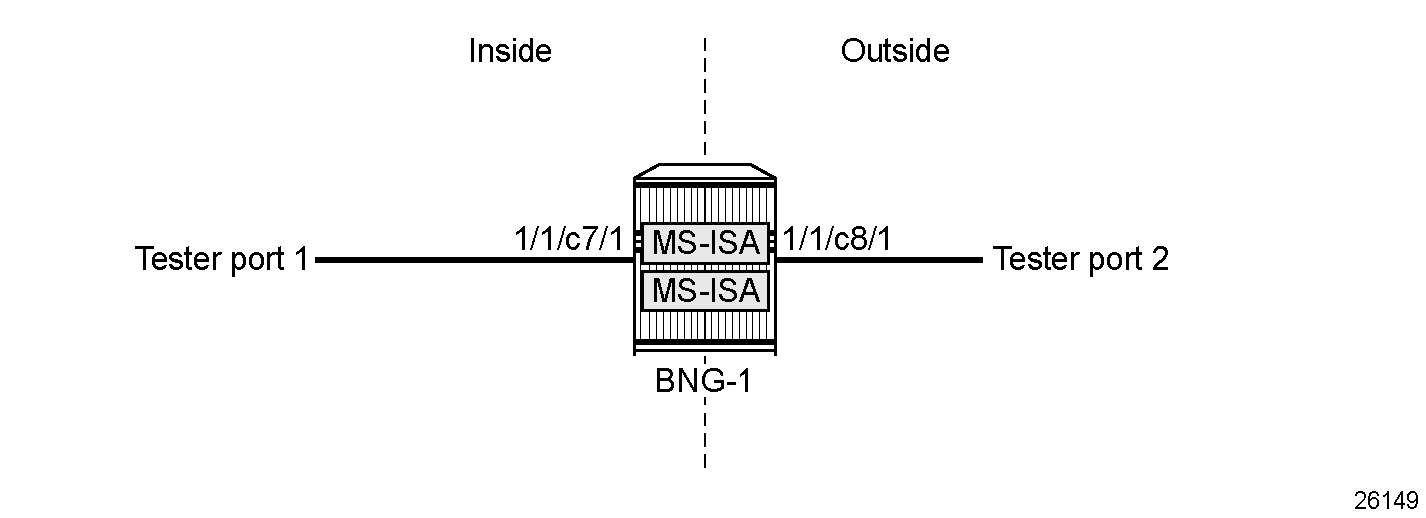
Example topology shows a topology with one node connected to two test center ports. Traffic can be sent between tester port 1 and tester port 2.
Private address ranges are used in outside pools in this chapter but normally public address ranges are used.
Configuration prerequisites
The card and MDA configuration is as follows:
configure {
card 1 {
admin-state enable
card-type i80-200g-sfpdd+12-400g-qsfpdd-1
mda 1 {
admin-state enable
mda-type m80-200g-sfpdd+12-400g-qsfpdd-1
}
The ESA configuration is as follows:
configure {
esa 1 {
admin-state enable
host-port 1/1/c80/1 {
}
host-port 1/1/c92/1 {
}
vm 1 {
admin-state enable
host-port 1/1/c80/1
vm-type bb
cores 4
memory 16
}
vm 3 {
admin-state enable
host-port 1/1/c92/1
vm-type bb
cores 4
memory 16
}
NAT group 1 is configured as follows:
configure {
isa {
nat-group 1 {
admin-state enable
description "NAT group 1"
redundancy {
active-mda-limit 1
}
esa 1 vm 1 { }
esa 1 vm 3 { }
}Configuration commands
A NAT outside pool is configured using the following command:
configure {router | service vprn <service-id>}
nat {
outside {
pool <nat-pool-name>
type large-scale
nat-group <nat-group-id>
port-forwarding-range {
range-end <range-end>
}
port-reservation {
{port-blocks <num-blocks> | ports <num-ports>}
}
large-scale {
subscriber-limit <subscriber-limit>
deterministic
port-reservation <det-num-ports>
}
}
address-range <start-ip-address> end <end-ip-address> {
}
}
}
-
nat-pool-name — Specifies the name of the NAT pool up to 32 characters max.
-
nat-group-id — Specifies the NAT group ID. The values are 1 — 4.
-
type — Specifies the pool type (large-scale).
-
num-blocks — Specifies the number of dynamic port blocks per outside IP address. The values are 1 — 64512.
-
num-ports — Specifies the number of ports per dynamic block. The values are 1 — 64512.
-
range-end — Specifies the upper limit of the port range available for static port forwarding. The values are 1023 — 65535.
-
subscriber-limit — Specifies the maximum number of subscribers per outside IP address.
-
A power of 2 (2^n) number for deterministic NAT: [1,2,4,8,16,32,64,128,256,512,1024,2048, 4096, 8192,16348, 32768]
-
1..65535 for non-deterministic NAT with default value: 65535
-
-
det-num-ports — Specifies the number of ports in a deterministic port block that is allocated and dedicated to a single subscriber during the configuration phase. The values are 1..65535.
-
start-ip-address — Specifies the first outside IP address in the a.b.c.d format.
-
end-ip-address — Specifies the last outside IP address in the a.b.c.d format.
When the subscriber limit equals 1, each subscriber is mapped to a single outside IP address, though the NAPT port translation function is still performed.
1:1 NAT mode in combination with deterministic NAT is not supported.
A NAT policy is configured using the following command:
configure {
service {
nat {
nat-policy <nat-policy-name> {
block-limit <[1..40]>
pool {
router-instance {<router-instance | vprn-service-name>}
name <nat-pool-name>
}
-
nat-policy-name — Specifies the NAT policy name up to 32 characters max.
-
block-limit —The maximum number of deterministic plus dynamic port blocks that can be assigned to a single inside IP address. In other words, the maximum number of dynamic port blocks that can be assigned to an inside IP address when the deterministic port block is exhausted equals (block-limit – 1).
-
nat-pool-name — Specifies the NAT pool name up to 32 characters max.
-
router-instance — Specifies the router instance the pool belongs to, either by router name or VPRN service ID. The router instance values are "Base" or a VPRN service name of maximum 64 characters.
A NAT inside prefix is configured using the following command:
configure [router| service vprn <service-name>]
nat {
inside {
large-scale {
nat44 {
max-subscriber-limit <max>
deterministic {
prefix-map <source-prefix> nat-policy <nat-policy-name> {
map <lsn-sub-address> to <lsn-sub-address> {
first-outside-address <outside-ip-address>
}
}
}
}
-
max-subscriber-limit <max> — The power of 2 (2^n) number that must match the largest subscriber limit number in a deterministic pool referenced from this inside routing instance. The range for this command is the same as the subscriber limit command under the pool hierarchy. The values are 1,2,4,8 ... 32768.
-
Should be greater than or equal to the largest subscriber limit of all pools referenced by the NAT policies within the corresponding inside routing instance.
-
Must be configured before any inside prefix configuration.
-
Must be 2^n and affects the ingress hashing of deterministic subscribers and also non-deterministic subscribers in case both are configured under the same inside router instance.
-
-
source-prefix — A prefix on the inside encompassing subscribers to be deterministically mapped to an outside IP address and port block in the corresponding pool.
-
<unicast-ipv4-address-and-prefix> | <expression>
-
<ipv4-prefix> — a.b.c.d (host bits must be 0)
-
<ipv4-prefix-length> — [0..32]
-
-
<unicast-ipv4-address-and-prefix> | <expression>
-
wildcard (*)
-
regular expression (')
-
range [ ]
-
-
-
<nat-policy-name> — Specifies a NAT policy name up to 32 characters in length.
Three cases are now configured to demonstrate the use of deterministic and dynamic port-block usage:
Case 1 - mapping multiple prefixes of the same VRF into the same outside pool: Mapping multiple prefixes from the same VRF (VPRN 15001) into the same outside pool, routing instance Base.
Case 2 - mapping multiple prefixes from the same VRF into different outside NAT pools: Mapping multiple prefixes from the same VRF (VPRN 15001) into different outside pools, routing instance VPRN 15002
Case 3 - mapping overlapping prefixes from different VRFs into the same outside NAT pool: Mapping overlapping prefixes from different VRFs (VPRN 15001 and VPRN 15002) into the same outside pool, routing instance Base.
Case 1 - mapping multiple prefixes of the same VRF into the same outside pool
Case 1 shows that the inside prefixes 10.0.0.0/24 and 10.10.4.0/22 in VPRN-15001 are mapped to the same outside NAT pool in the Base router. All traffic is NATed.
The NAT outside pool is configured as follows:
configure {
router "Base" {
nat {
outside {
pool "nat-pool-1" {
admin-state enable
type large-scale
nat-group 1
port-forwarding {
range-end 1099
}
port-reservation {
ports 20
}
large-scale {
subscriber-limit 128
deterministic {
port-reservation 28
}
}
address-range 192.168.0.1 end 192.168.0.100 {
}
}
}
The NAT policy is configured as follows:
configure {
service {
nat {
nat-policy "nat-policy-1" {
block-limit 4
pool {
router-instance "Base"
name "nat-pool-1"
}
}
}
The NAT inside prefixes are configured as follows:
configure {
service {
vprn "VPRN-15001" {
admin-state enable
service-id 15001
customer "1"
nat {
inside {
large-scale {
nat44 {
max-subscriber-limit 256
destination-prefix 0.0.0.0/0 {
}
deterministic {
prefix-map 10.0.0.0/24 nat-policy "nat-policy-1" {
admin-state enable
map 10.0.0.0 to 10.0.0.255 {
first-outside-address 192.168.0.1
}
}
prefix-map 10.10.4.0/22 nat-policy "nat-policy-1" {
admin-state enable
map 10.10.4.0 to 10.10.7.255 {
first-outside-address 192.168.0.3
}
}
}
}
}
}
}
map statements are automatically created when the prefix is created and it is in admin-state enable.
Show commands
The subscriber limit is set to 128 for the 10.0.0.0/24 prefix, so it is broken into two smaller /25 prefixes each. Each of these smaller prefixes are mapped into a specific outside IP address.
The following command shows the first Large Scale NAT (LSN) subscriber of the first /25 prefix for inside routing instance 15001:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-router 15001 inside-ip 10.0.0.0
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.0.0.0]
NAT policy : nat-policy-1
Subscriber ID : 276824064
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.0.0.0/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : "Base"
Outside IP address : 192.168.0.1
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last subscriber mapping to the same 192.168.0.1 outside IP address has inside address 10.0.0.127.
The following command shows the first LSN subscriber of the second /25 prefix for inside routing instance 15001:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-router 15001 inside-ip 10.0.0.128
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.0.0.128]
NAT policy : nat-policy-1
Subscriber ID : 276824192
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.0.0.128/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : "Base"
Outside IP address : 192.168.0.2
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last subscriber mapping to the same 192.168.0.2 outside IP address has inside address 10.0.0.255.
The following command shows the base router LSN blocks corresponding to the first inside IP address within the 10.0.0.0/24 prefix:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.0.0.0
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.1 [1100..1127]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.0.0.0
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
The following command shows the base router LSN blocks corresponding to the last inside IP address within the 10.0.0.0/24 prefix:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.0.0.255
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.2 [4656..4683]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.0.0.255
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
The subscriber limit is 128 for the 10.10.4.0/22 prefix, so it is broken into eight /25 prefixes. Each of these smaller prefixes are mapped into a specific outside IP address.
The following command shows the first LSN subscriber of the first /25 prefix for inside routing instance 15001:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.10.4.0
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.10.4.0]
NAT policy : nat-policy-1
Subscriber ID : 276824320
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.10.4.0/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : "Base"
Outside IP address : 192.168.0.3
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last subscriber mapping to the same 192.168.0.3 outside IP address has inside address 10.10.4.127.
The following command shows the first LSN subscriber of the last /25 prefix for inside routing instance 15001:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.10.7.128
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.10.7.128]
NAT policy : nat-policy-1
Subscriber ID : 276825216
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.10.7.128/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : "Base"
Outside IP address : 192.168.0.10
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The following command shows the base router LSN blocks corresponding to the first inside IP within 10.10.4.0/24 prefix:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.10.4.0
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.3 [1100..1127]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.10.4.0
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
The following command shows the base router LSN blocks corresponding to the last inside IP within 10.10.4.0/24 prefix:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.10.7.255
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.10 [4656..4683]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.10.7.255
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
Mapping results
According to this configuration, each inside IP address has one deterministic block of 28 ports and can have up to three dynamic blocks (block-limit = 4) each of 20 ports, allowing a maximum of 28+3*20 = 88 flows.
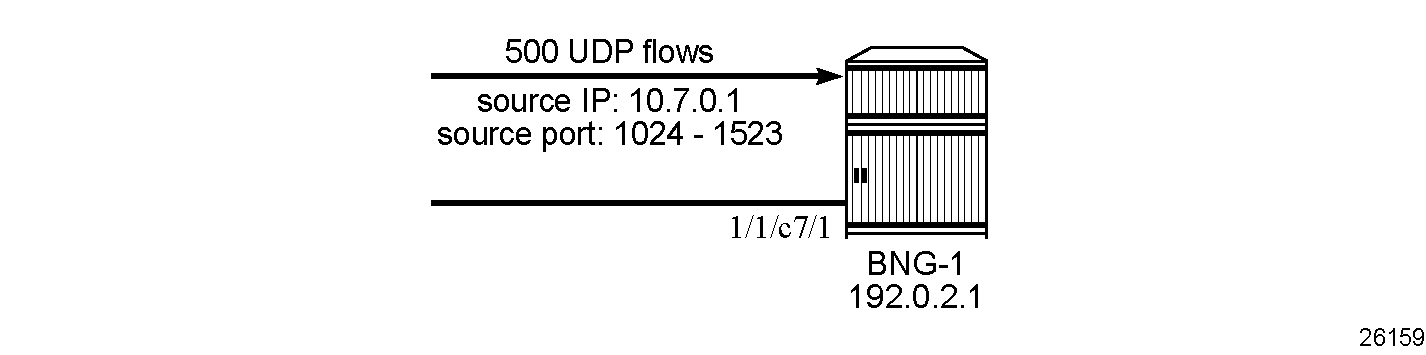
Sending flows
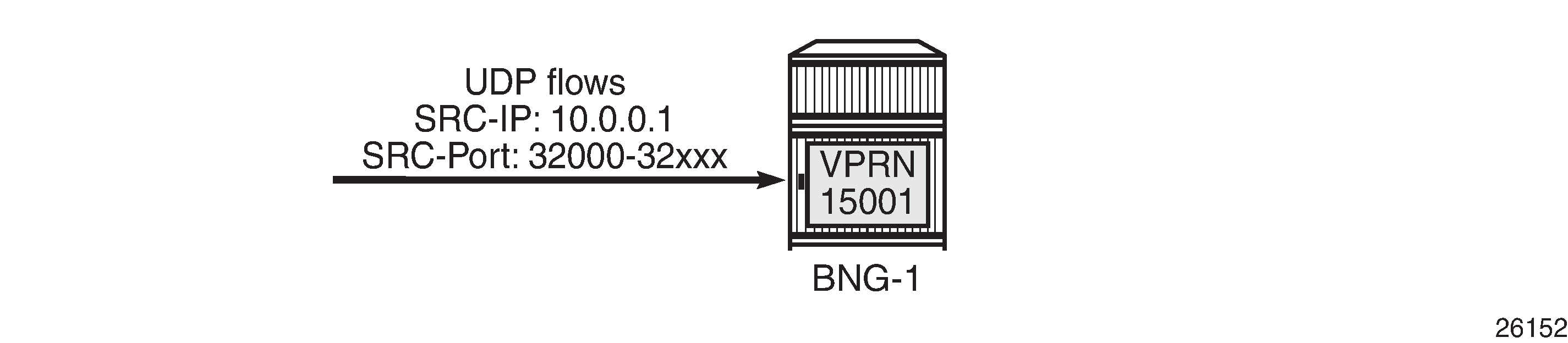
For the inside IP 10.0.0.1, several UDP flows are sent with source IP 10.10.0.1 and different source UDP port numbers. Both the deterministic and dynamic blocks mappings are verified.
When sending 28 UDP flows or less, all flows are mapped to a single deterministic block because the number of ports in a deterministic block is 28. There is no logging; because no dynamic blocks are used, only the deterministic block is used.
The following command shows the LSN blocks on the outside Base routing instance and the outside ports allocated for the inside IP 10.0.0.1:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.0.0.1
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.1 [1128..1155]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.0.0.1
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
When increasing the number of flows such that: 29 ≤ number of flows ≤ 48
-
In addition to the deterministic block (28 ports), there is an extension by 1 dynamic block of 20 ports (port-reservation=20).
-
Logging occurs for the dynamic port block.
With the following command, NAT tmnxNatPlBlockAllocationLsn (2012) events are generated with the default severity:
configure {
log {
log-events {
nat event tmnxNatPlBlockAllocationLsn {
generate true
}The following command shows the base router LSN blocks and the outside ports allocated to the inside IP address 10.0.0.1: the first block is the deterministic block of 28 ports and the second block is a dynamic block of 20 ports.
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.0.0.1
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.1 [1128..1155]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.0.0.1
192.168.0.1 [4684..4703]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:33:42
Inside router : vprn15001
Inside IP address : 10.0.0.1
-------------------------------------------------------------------------------
Number of blocks: 2
===============================================================================
With NAT event 2012 (tmnxNatPlBlockAllocationLsn) generated, logging can be verified using Log 99 which shows the mapping details to the new dynamic block as follows:
308 2025/10/13 09:33:42.025 UTC MINOR: NAT #2012 Base NAT
"{3} Map 192.168.0.1 [4684-4703] ESA-VM 1/1 -- 276824065 classic-lsn-sub %1 vprn15001 10.0.0.1 at 2025/10/13 09:33:42"
When increasing the number of flows such that: 49 ≤ number of flows ≤ 68
-
In addition to the deterministic block (28 ports), there is an extension by 2 dynamic blocks of 20 ports each.
-
Logging occurs for the dynamic port blocks.
The following command shows LSN blocks on the outside Base routing instance and the outside ports allocated for the inside IP 10.0.0.1:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.0.0.1
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.1 [1128..1155]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.0.0.1
192.168.0.1 [4684..4703]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:33:42
Inside router : vprn15001
Inside IP address : 10.0.0.1
192.168.0.1 [4704..4723]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:34:24
Inside router : vprn15001
Inside IP address : 10.0.0.1
-------------------------------------------------------------------------------
Number of blocks: 3
===============================================================================
Logging is verified using Log 99 (in case event-control NAT events are generated) which shows the mapping details to the new dynamic block as follows:
309 2025/10/13 09:34:24.957 UTC MINOR: NAT #2012 Base NAT
"{4} Map 192.168.0.1 [4704-4723] ESA-VM 1/1 -- 276824065 classic-lsn-sub %1 vprn15001 10.0.0.1 at 2025/10/13 09:34:24"
When increasing the number of flows such that: 69 ≤ number of flows ≤ 88
-
In addition to the deterministic block (28 ports), there is an extension by 3 dynamic blocks of 20 ports each.
-
Logging occurs for the dynamic port blocks.
The following command shows LSN blocks on the outside Base routing instance and the outside ports allocated for the inside IP 10.0.0.1:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.0.0.1
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.0.1 [1128..1155]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:04:36
Inside router : vprn15001
Inside IP address : 10.0.0.1
192.168.0.1 [4684..4703]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:33:42
Inside router : vprn15001
Inside IP address : 10.0.0.1
192.168.0.1 [4704..4723]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:34:24
Inside router : vprn15001
Inside IP address : 10.0.0.1
192.168.0.1 [4724..4743]
Pool : nat-pool-1
Policy : nat-policy-1
Started : 2025/10/13 09:35:18
Inside router : vprn15001
Inside IP address : 10.0.0.1
-------------------------------------------------------------------------------
Number of blocks: 4
===============================================================================
Logging is verified using Log 99 which shows the mapping details to the new dynamic block as follows:
310 2025/10/13 09:35:18.679 UTC MINOR: NAT #2012 Base NAT
"{5} Map 192.168.0.1 [4724-4743] ESA-VM 1/1 -- 276824065 classic-lsn-sub %1 vprn15001 10.0.0.1 at 2025/10/13 09:35:18"
When increasing the number of flows such that the number of flows > 88
-
No more extension by dynamic blocks (block limit = 4) allowed.
-
Any flows more than 88 are dropped and the relevant NAT statistics incremented.
To verify NAT statistics, first check the NAT group, member, and ESA (or MS-ISA) associated with the outside IP 192.168.0.1/32:
[/]
A:admin@BNG-1# show router route-table 192.168.0.1/32
===============================================================================
Route Table (Router: Base)
===============================================================================
Dest Prefix[Flags] Type Proto Age Pref
Next Hop[Interface Name] Metric
-------------------------------------------------------------------------------
192.168.0.1/32 Remote NAT 00h36m01s 0
NAT outside to esa 1 vm 1 0
-------------------------------------------------------------------------------
No. of Routes: 1
Flags: n = Number of times nexthop is repeated
B = BGP backup route available
L = LFA nexthop available
S = Sticky ECMP requested
===============================================================================
To check which group and member this ESA belongs to, the following command can be used:
[/]
A:admin@BNG-1# show isa nat-group 1 members
===============================================================================
ISA Group 1 members
===============================================================================
Group Member State MDA/VM Addresses Blocks Se-% Hi Se-Prio
-------------------------------------------------------------------------------
1 1 active esa-1/1 10 1490 < 1 N 0
-------------------------------------------------------------------------------
No. of members: 1
===============================================================================
The following command can be used to verify relevant statistics for this NAT group/member:
[/]
A:admin@BNG-1# show isa nat-group 1 statistics esa-vm 1/1 | match flow
no matching flow : 0
max flow exceeded : 0
TCP no flow for RST : 0
TCP no flow for FIN : 0
TCP no flow : 0
flow log failed : 0
new flow : 80
found flow : 122107
flow create logged : 0
flow delete logged : 0
flow log pkt tx : 0
flow create failed, key ambiguous : 0
flow create failed, conflicting policies : 0
too many frag. lists for flow : 0
flow log pkt rate limit dropped : 0
Case 2 - mapping multiple prefixes from the same VRF into different outside NAT pools
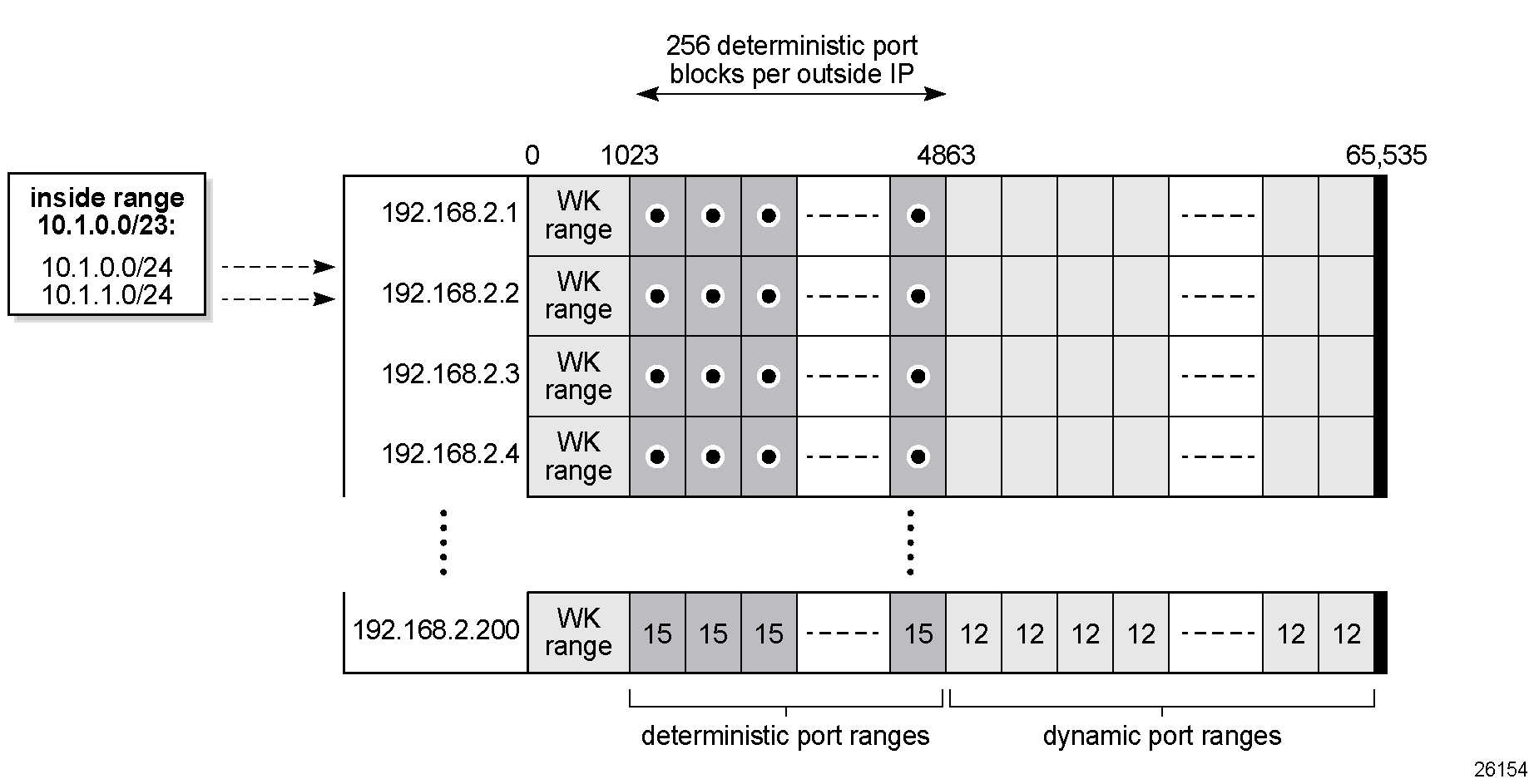
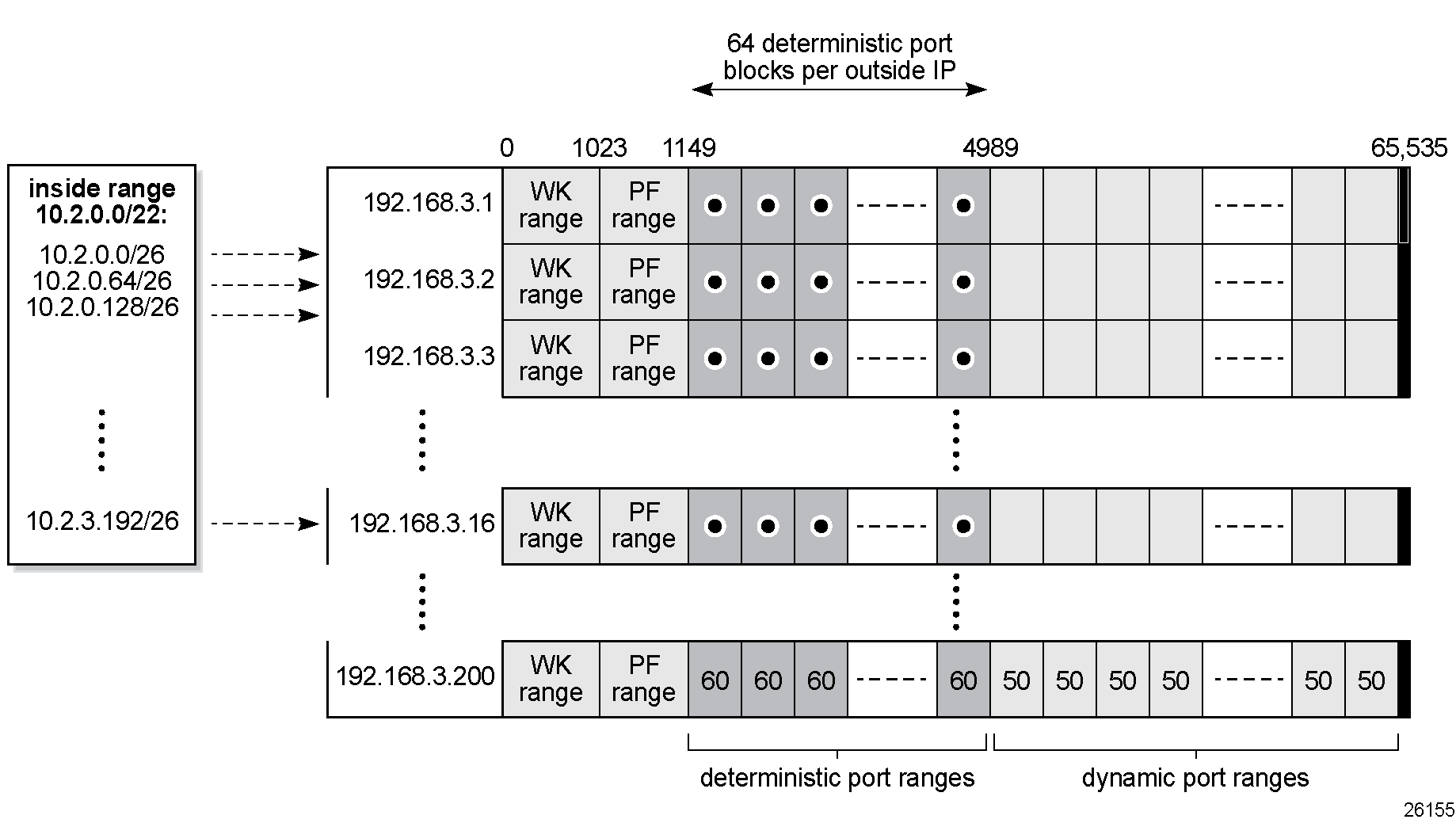
Case 2 shows that prefix 10.1.0.0/23 in VPRN-15001 is mapped to outgoing NAT pool "nat-pool-2" in VPRN-15002 while prefix 10.2.0.0/22 in VPRN-15001 is mapped to "nat-pool-3" in VPRN-15002. All traffic is NATed.
The NAT outside pools are configured in VPRN-15002, as follows:
configure {
service {
vprn "VPRN-15002" {
admin-state enable
service-id 15002
customer "1"
nat {
outside {
pool "nat-pool-2" {
admin-state enable
type large-scale
nat-group 1
port-reservation {
ports 12
}
large-scale {
subscriber-limit 256
deterministic {
port-reservation 15
}
}
address-range 192.168.2.1 end 192.168.2.200 {
}
}
pool "nat-pool-3" {
admin-state enable
type large-scale
nat-group 1
port-forwarding {
range-end 1149
}
port-reservation {
ports 50
}
large-scale {
subscriber-limit 64
deterministic {
port-reservation 60
}
}
address-range 192.168.3.1 end 192.168.3.200 {
}
}
}
}
The NAT policies are configured as follows:
configure {
service {
nat {
nat-policy "nat-policy-2" {
block-limit 4
pool {
router-instance "VPRN-15002"
name "nat-pool-2"
}
}
nat-policy "nat-policy-3" {
block-limit 2
pool {
router-instance "VPRN-15002"
name "nat-pool-3"
}
}
The NAT inside prefixes are configured as follows:
configure {
service {
vprn "VPRN-15001" {
admin-state enable
service-id 15001
customer "1"
nat {
inside {
large-scale {
nat44 {
max-subscriber-limit 256
destination-prefix 0.0.0.0/0 {
}
deterministic {
prefix-map 10.1.0.0/23 nat-policy "nat-policy-2" {
admin-state enable
map 10.1.0.0 to 10.1.1.255 {
first-outside-address 192.168.2.1
}
}
prefix-map 10.2.0.0/22 nat-policy "nat-policy-3" {
admin-state enable
map 10.2.0.0 to 10.2.3.255 {
first-outside-address 192.168.3.1
}
}
}
}
}
}Show commands
The subscriber limit corresponding to the 10.1.0.0/23 prefix is 256, so the 10.1.0.0/23 prefix is broken into two /24 prefixes. Each of these smaller prefixes are mapped into a specific outside IP address.
The following command shows the first LSN subscriber of the first /24 prefix for inside routing instance 15001:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.1.0.0
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.1.0.0]
NAT policy : nat-policy-2
Subscriber ID : 276825344
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.1.0.0/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : 15002
Outside IP address : 192.168.2.1
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last subscriber mapping to the same 192.168.2.1 outside IP address has inside address 10.1.0.255.
The following command shows the first LSN subscriber of the second /24 prefix for inside routing instance 15001:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.1.1.0
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.1.1.0]
NAT policy : nat-policy-2
Subscriber ID : 276825600
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.1.1.0/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : 15002
Outside IP address : 192.168.2.2
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last subscriber mapping to the same 192.168.2.2 outside IP address has inside address 10.1.1.255.
The following command shows the VPRN-15002 LSN blocks corresponding to the first inside IP address within the 10.1.0.0/23 prefix:
[/]
A:admin@BNG-1# show router 15002 nat lsn-blocks inside-ip 10.1.0.0
===============================================================================
Large-Scale NAT blocks for vprn15002
===============================================================================
192.168.2.1 [1024..1038]
Pool : nat-pool-2
Policy : nat-policy-2
Started : 2025/10/13 09:45:31
Inside router : vprn15001
Inside IP address : 10.1.0.0
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
The following command shows the VPRN-15002 LSN blocks corresponding to the last inside IP address within the 10.1.0.0/23 prefix:
[/]
A:admin@BNG-1# show router 15002 nat lsn-blocks inside-ip 10.1.1.255
===============================================================================
Large-Scale NAT blocks for vprn15002
===============================================================================
192.168.2.2 [4849..4863]
Pool : nat-pool-2
Policy : nat-policy-2
Started : 2025/10/13 09:45:31
Inside router : vprn15001
Inside IP address : 10.1.1.255
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
The subscriber limit corresponding to the 10.2.0.0/22 prefix is 64,so the 10.2.0.0/22 prefix is broken into sixteen /26 prefixes. Each of these /26 prefixes is mapped to a specific outside IP address.
The following command shows the first LSN subscriber for the inside routing instance 15001 for the first /26 prefix:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.2.0.0
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.2.0.0]
NAT policy : nat-policy-3
Subscriber ID : 276825856
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.2.0.0/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : 15002
Outside IP address : 192.168.3.1
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last inside address mapping to the 192.168.3.1 outside address is 10.2.0.63.
The following command shows the first LSN subscriber for the inside routing instance 15001 for the last /26 prefix:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.2.3.192
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.2.3.192]
NAT policy : nat-policy-3
Subscriber ID : 276826816
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.2.3.192/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : 15002
Outside IP address : 192.168.3.16
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last inside address mapping to the 192.168.3.16 outside address is 10.2.3.255.
The following command shows the VPRN-15002 LSN blocks corresponding to the first inside IP address within the 10.2.0.0/22 prefix:
[/]
A:admin@BNG-1# show router 15002 nat lsn-blocks inside-ip 10.2.0.0
===============================================================================
Large-Scale NAT blocks for vprn15002
===============================================================================
192.168.3.1 [1150..1209]
Pool : nat-pool-3
Policy : nat-policy-3
Started : 2025/10/13 09:45:31
Inside router : vprn15001
Inside IP address : 10.2.0.0
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
The following command shows the VPRN-15002 LSN blocks corresponding to the last inside IP within the 10.2.0.0/22 prefix:
[/]
A:admin@BNG-1# show router 15002 nat lsn-blocks inside-ip 10.2.3.255
===============================================================================
Large-Scale NAT blocks for vprn15002
===============================================================================
192.168.3.16 [4930..4989]
Pool : nat-pool-3
Policy : nat-policy-3
Started : 2025/10/13 09:45:31
Inside router : vprn15001
Inside IP address : 10.2.3.255
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
Mapping results
According to this configuration, for the 10.1.0.0/23 prefix, each inside IP address has one deterministic block of 15 ports and can have up to three dynamic blocks (block limit =4) each of 12 ports, allowing for a maximum of 15+3*12 = 51 flows.
According to this configuration, for the 10.2.0.0/22 prefix, each inside IP address has one deterministic block of 60 ports, and can have up to one dynamic block (block limit =2) of 50 ports, allowing for a maximum of 60+50 = 110 flows.
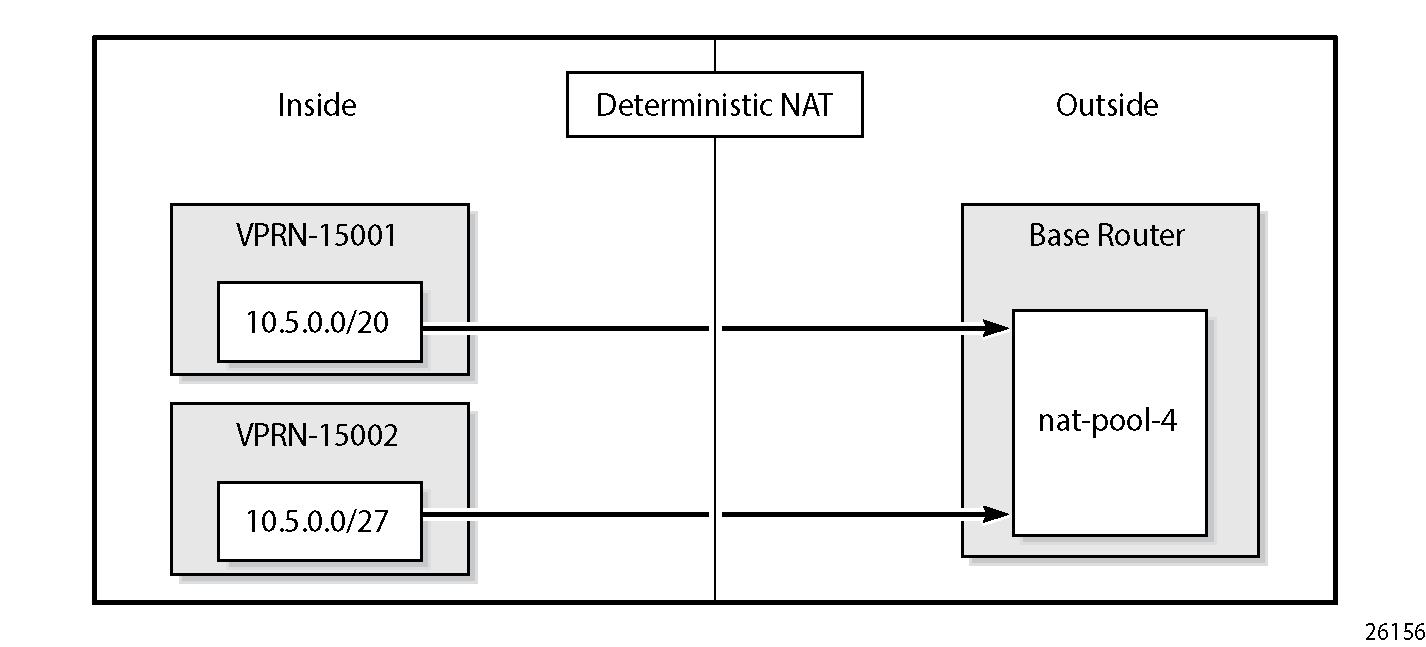
Case 3 - mapping overlapping prefixes from different VRFs into the same outside NAT pool
Case 3 shows that overlapping prefixes from VPRN-15001 and VPRN-15002 are mapped to the same outside NAT pool in the Base router. All traffic is NATed.
The NAT outside pool is configured as follows:
configure {
router "Base" {
nat {
outside {
pool "nat-pool-4" {
admin-state enable
type large-scale
nat-group 1
port-forwarding {
range-end 1049
}
port-reservation {
ports 50
}
large-scale {
subscriber-limit 64
deterministic {
port-reservation 62
}
}
address-range 192.168.4.1 end 192.168.4.100 {
}
}The NAT policy is configured as follows:
configure {
service {
nat {
nat-policy "nat-policy-4" {
block-limit 4
pool {
router-instance "Base"
name "nat-pool-4"
}
}The NAT inside prefix is configured as follows:
configure {
service {
vprn "VPRN-15001" {
admin-state enable
service-id 15001
customer "1"
nat {
inside {
large-scale {
nat44 {
max-subscriber-limit 256
destination-prefix 0.0.0.0/0 {
}
deterministic {
prefix-map 10.5.0.0/20 nat-policy "nat-policy-4" {
admin-state enable
map 10.5.0.0 to 10.5.15.255 {
first-outside-address 192.168.4.1
}
}
}
}
}
}
}
}
vprn "VPRN-15002" {
admin-state enable
service-id 15002
customer "1"
nat {
inside {
large-scale {
nat44 {
max-subscriber-limit 128
destination-prefix 0.0.0.0/0 {
}
deterministic {
prefix-map 10.5.0.0/27 nat-policy "nat-policy-4" {
admin-state enable
map 10.5.0.0 to 10.5.0.31 {
first-outside-address 192.168.4.65
}
}
}
}
}
}
}
}
Show commands
For the 10.5.0.0/20 prefix on VPRN 15001, the subscriber-limit is 64. The 10.5.0.0/20 prefix is broken into 64 smaller /26 prefixes, each to be mapped into a specific outside IP address.
The following command shows the first LSN subscriber for the inside routing instance 15001 of the first /26 prefix:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.5.0.0 inside-router 15001
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.5.0.0]
NAT policy : nat-policy-4
Subscriber ID : 276826880
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.5.0.0/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : "Base"
Outside IP address : 192.168.4.1
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last inside address mapping to the 192.168.4.1 outside address is 10.5.0.63.
The following command shows the first Large Scale NAT (LSN) subscriber for the inside routing instance 15001 of the last /26 prefix:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.5.15.192 inside-router 15001
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.5.15.192]
NAT policy : nat-policy-4
Subscriber ID : 276830912
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15001
Inside IP address prefix : 10.5.15.192/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : "Base"
Outside IP address : 192.168.4.64
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The last inside address mapping to the 192.168.4.64 outside address is 10.5.15.255.
The following command shows the base router LSN blocks corresponding to the first inside IP address within the 10.5.0.0/20 prefix:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.5.0.0 inside-router 15001
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.4.1 [1050..1111]
Pool : nat-pool-4
Policy : nat-policy-4
Started : 2025/10/13 09:52:33
Inside router : vprn15001
Inside IP address : 10.5.0.0
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
To show the base router LSN blocks corresponding to the last inside IP address within the 10.5.0.0/20 prefix, the following command can be used:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.5.15.255 inside-router 15001
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.4.64 [4956..5017]
Pool : nat-pool-4
Policy : nat-policy-4
Started : 2025/10/13 09:52:33
Inside router : vprn15001
Inside IP address : 10.5.15.255
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
For the 10.5.0.0/27 prefix in VPRN 15002, the subscriber limit is 64. The 10.5.0.0/27 prefix is mapped into one outside IP address.
The following command shows the first LSN subscriber for the inside routing instance 15002 of the 10.5.0.0/27 prefix:
[/]
A:admin@BNG-1# show service nat lsn-subscribers inside-ip 10.5.0.0 inside-router 15002
===============================================================================
NAT LSN subscribers
===============================================================================
Subscriber : [LSN-Host@10.5.0.0]
NAT policy : nat-policy-4
Subscriber ID : 276830976
-------------------------------------------------------------------------------
Type : classic-lsn-sub
Inside router : 15002
Inside IP address prefix : 10.5.0.0/32
ISA NAT group : 1
ISA NAT group member : 1
Outside router : "Base"
Outside IP address : 192.168.4.65
-------------------------------------------------------------------------------
No. of LSN subscriber instances: 1
===============================================================================
The following command shows the LSN blocks corresponding to the first inside IP address within the 10.5.0.0/27 prefix:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.5.0.0 inside-router 15002
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.4.65 [1050..1111]
Pool : nat-pool-4
Policy : nat-policy-4
Started : 2025/10/13 09:52:33
Inside router : vprn15002
Inside IP address : 10.5.0.0
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
The following command shows the LSN blocks for the last inside IP address within the 10.5.0.0/27 prefix
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.5.0.31 inside-router 15002
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.4.65 [2972..3033]
Pool : nat-pool-4
Policy : nat-policy-4
Started : 2025/10/13 09:52:33
Inside router : vprn15002
Inside IP address : 10.5.0.31
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
Mapping results
According to this configuration, each inside IP address within VPRN 15001 has one deterministic block of 62 ports and can have up to three dynamic blocks (block-limit =4) of 50 ports each, allowing a maximum of 62+3*50 = 212 flows.
According to this configuration each inside IP address within VPRN 15002 has one deterministic block of 62 ports and can have up to three dynamic blocks (block limit =4) of ports each, allowing a maximum of 62+3*50 = 212 flows.
For VPRN 15002, because the number of LSN subscribers (32) is less than the number of deterministic blocks (64), 32 deterministic blocks are wasted, specifically 32*62 = 1984 ports are wasted which is not good in terms of capacity planning.
Inverse mapping
In deterministic LSN44, the inside IP addresses are mapped to outside IP addresses and corresponding port blocks based on a deterministic algorithm. The inverse mapping that reveals the subscriber identity behind the NAT is based on the reversal of this algorithm.
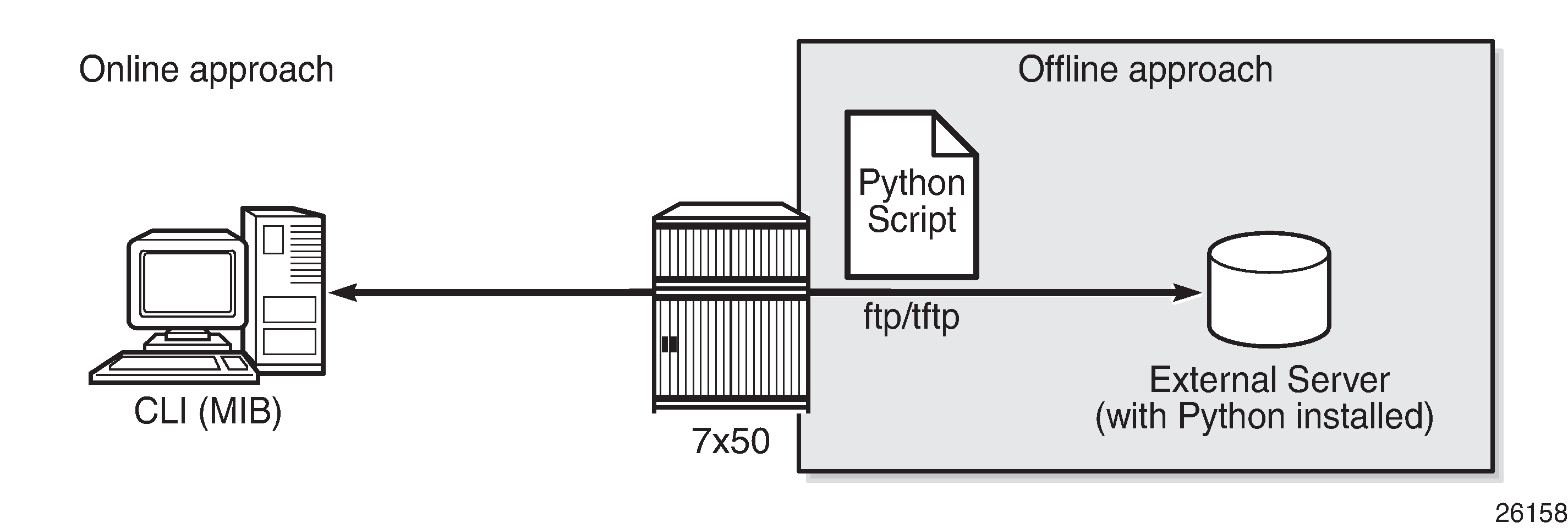
Inverse mapping approach shows that inverse mappings can be done either online or offline:
Online — Locally on the SR OS node, via CLI (MIB)
Offline — Externally, via a Python script. The purpose of such an offline approach is to provide fast queries without accessing the SR OS node.
Online approach
A tools command is available which shows the reverse mapping (outside to inside) for deterministic NAT instead of using logging.
tools dump nat deterministic-mapping outside-ip <ipv4-address | expression> router <router-instance> outside-port <[1..65535]>
Using Case 3 - mapping overlapping prefixes from different VRFs into the same outside NAT pool as an example, to obtain (inside IP, inside routing instance), the inverse mapping for a specific (outside IP, outside routing instance, outside port) is done as follows:
[/]
A:admin@BNG-1# tools dump nat deterministic-mapping outside-ip 192.168.4.1 router "Base" outside-port 1050
classic-lsn-sub inside router 15001 ip 10.5.0.0 -- outside router Base ip 192.168.4.1 port 1050 at Mon Oct 13 10:00:37 UTC 2025
[/]
A:admin@BNG-1# tools dump nat deterministic-mapping outside-ip 192.168.4.65 router "Base" outside-port 1050
classic-lsn-sub inside router 15002 ip 10.5.0.0 -- outside router Base ip 192.168.4.65 port 1050 at Mon Oct 13 10:00:37 UTC 2025
Offline approach
The purpose of such an offline approach is to provide fast queries without the need to directly query the SR OS node. This is achieved by generating and exporting a Python script for reverse querying, which is a manual operation that needs to be repeated every time there is configuration change in deterministic NAT.
The script is exported (manually) to the external system.
To configure remotely the location for the Python script, the following command is used:
configure {
service {
nat {
deterministic-script {
location <remote-url>
The remote URL is a remote location where the script is stored, such as:
[{ftp://|tftp://}<login>:<pswd>@ <remote-location>/][<file-path>]The remote URL has a maximum length of 180 characters.
When the script location is specified, the script can be exported to that location using the following command:
admin nat save-deterministic-script
Using the following command the status of the script can be checked, and whether it is necessary to re-save (export) the script or not:
[/]
A:admin@BNG-1# show service nat deterministic-script
===============================================================================
Deterministic NAT script data
===============================================================================
Location : ftp://*:*@192.99.1.249/./images/detnat.py
Save needed : no
Last save result : success
Last save time : 2025/10/13 10:01:13
===============================================================================
The external system must have the Python scripting language installed with the following modules: getopt, math, os, socket, and sys.
The Python script can then be run on the external server; the parameters are as follows:
(ANPM2VM1-HOST):~/images > ./detnat.py
Error: need exactly one of --forward or --backward arguments
Usage: detnat.py DIRECTION PARAMETERS
Perform forward or backard NAPT according to the configured deterministic rules.
DIRECTION:
-f, --forward Translate from inside to outside address/port
-b, --backward Translate from outside to inside address/port
PARAMETERS:
-a, --address=IP-ADDRESS The address to translate. IPv6 addresses can be
specified in shorthand or full notation.
-p, --port=PORT The outside port in case of backward translation.
-s, --service=SERVICE-ID The service where the IP-ADDRESS originates from.
This is the inside service in case of forward
translation and the outside service in case of
backward translation.
To specify the base router, this option must be
omitted.
-P, --policy=POLICY-NAME The nat-policy used by the subscriber.
-h, --help Show this help message
where detnat.py is the name of the python script previously exported.
As an example of a forward query:
(ANPM2VM1-HOST):~/images > ./detnat.py -f -s 15001 -a 10.0.0.1
classic-lsn-sub is using policy nat-policy-1, has public ip address 192.168.0.1 from base router and is using ports [1128 - 1155]
As an example of a reverse query:
(ANPM2VM1-HOST):~/images > ./detnat.py -b -s 0 -a 192.168.4.1 -p 1525
classic-lsn-sub has private ip address 10.5.0.7 from service 15001 and is using policy nat-policy-4
Simultaneous support of deterministic and non-deterministic NAT
Deterministic NAT can be used simultaneously with non-deterministic NAT within the same inside routing instance. However, they cannot share the same pool.
An outside pool can be only deterministic (although expandable by dynamic ports blocks) or non-deterministic at any time. A non-deterministic pool is a pool that contains dynamic port blocks only.
The following shows a configuration using deterministic NAT simultaneously with non-deterministic NAT.
The NAT outside pools are configured as follows:
configure {
router "Base" {
nat {
outside {
pool "nat-pool-1" {
admin-state enable
type large-scale
nat-group 1
port-forwarding {
range-end 1099
}
port-reservation {
ports 20
}
large-scale {
subscriber-limit 128
deterministic {
port-reservation 28
}
}
address-range 192.168.0.1 end 192.168.0.100 {
}
}
pool "nat-pool-Non-Deterministic" {
admin-state enable
type large-scale
nat-group 1
address-range 192.168.7.1 end 192.168.7.100 {
}
}
}The NAT policies are configured as follows:
configure {
service {
nat {
nat-policy "nat-policy-1" {
block-limit 4
pool {
router-instance "Base"
name "nat-pool-1"
}
}
nat-policy "nat-policy-Non-Deterministic" {
pool {
router-instance "Base"
name "nat-pool-Non-Deterministic"
}
}The NAT inside prefixes are configured as follows:
configure {
service {
vprn "VPRN-15001" {
admin-state enable
service-id 15001
customer "1"
nat {
inside {
large-scale {
nat-policy "nat-policy-Non-Deterministic"
nat44 {
max-subscriber-limit 256
destination-prefix 0.0.0.0/0 {
}
deterministic {
prefix-map 10.0.0.0/24 nat-policy "nat-policy-1" {
admin-state enable
map 10.0.0.0 to 10.0.0.255 {
first-outside-address 192.168.0.1
}
}
}
}
}
}
}In this example, the inside IP prefixes that do not match any of the deterministic prefixes are NATed using a non-deterministic pool.
The following command shows which NAT pool and NAT policy are used for NATing the inside IP 10.7.0.1:
[/]
A:admin@BNG-1# show router nat lsn-blocks inside-ip 10.7.0.1
===============================================================================
Large-Scale NAT blocks for Base
===============================================================================
192.168.7.100 [1024..1055]
Pool : nat-pool-Non-Deterministic
Policy : nat-policy-Non-Deterministic
Started : 2025/10/13 10:06:06
Inside router : vprn15001
Inside IP address : 10.7.0.1
-------------------------------------------------------------------------------
Number of blocks: 1
===============================================================================
Conclusion
This example provides the commands required for configuring deterministic LSN44 NAT. Both deterministic as well as non-deterministic NAT are supported, with simultaneous operation being possible.
Inverse query can be done online or offline to retrieve the NAT mappings. Logging is not needed as long as there are no dynamic blocks assigned to LSN44 subscribers.