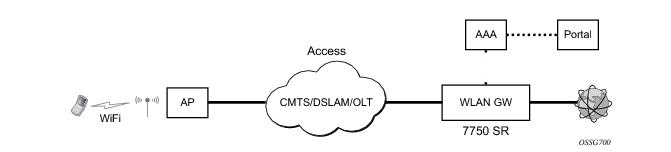
The 7750 SR serves as a WLAN Gateway (WLAN-GW) providing Layer 3 termination and ESM for these subscribers. The connectivity from WLAN AP or AC can be over any existing access technology (DSL, PON, Fiber, DOCSIS, etc.), with Ethernet based connectivity from the access-node (DSLAM, OLT, Eth MTU, Layer 2 CMTS) to the WLAN-GW. WLAN-GW functions could be on a standalone 7750 as shown in Figure 141 or could be an add-on functionality on existing 7750 based BNG as shown in
Figure 142. WLAN connectivity to the WLAN-GW could be over a Layer 2 aggregation or an Layer 3 aggregation network (typical when WLAN-GW is upstream of an existing BNG or CMTS). In case of Layer 2 aggregation the connectivity to the WLAN-GW could be tagged or untagged Ethernet. In case of Layer 3 aggregation, supported connectivity option is Ethernet over GRE (or Eth-over-MPLS over GRE) tunnel originating from the AP/AC, and terminating on the WLAN-GW. The WLAN AP acts as a bridge, switching Ethernet frames into a GRE tunnel terminating on an MS-ISA in the WLAN-GW.
The GRE encapsulation is based on RFC 1701/2784, Generic Routing Encapsulation (GRE), WLAN-GW will encapsulate according to RFC 1701 with all the flag fields set to 0, and no optional fields present. WLAN-GW is able to receive both encapsulation specified in RFC 1701 and RFC 2784, with all flag fields set to 0, and no optional fields present in the header.
config isa wlan-gw-group <group-id>
[no] active-iom-limit <number>
[no] description <description-string>
[no] * iom <slot-number>
nat
[no] radius-accounting-policy <nat-accounting-policy>
[no] session-limits
[no] reserved <num-sessions>
[no] watermarks high <percentage> low <percentage>
[no] shutdown
*B:Dut-C>config>service>vprn>sub-if>grp-if>soft-gre# info detail
----------------------------------------------
authentication
no authentication-policy
hold-time sec 5
exit
no data-triggered-ue-creation
dhcp
shutdown
active-lease-time min 10
initial-lease-time min 10
no l2-aware-ip-address
no primary-dns
no primary-nbns
no secondary-dns
no secondary-nbns
exit
egress
no agg-rate-limit
no hold-time
qos 1
no scheduler-policy
no shape-multi-client-only
no shaping
exit
gw-address 1.1.1.57
no gw-ipv6-address
no http-redirect-policy
no nat-policy
mobility
hold-time 5
no trigger
exit
router 70
no tcp-mss-adjust
track-mobility
mac-format "aa:"
no radius-proxy-cache
exit
wlan-gw-group 3
vlan-tag-ranges
no default-retail-svc-id
range start 0 end 100
authentication
no authentication-policy
hold-time sec 5
exit
no data-triggered-ue-creation
dhcp
shutdown
active-lease-time min 10
initial-lease-time min 10
no l2-aware-ip-address
no primary-dns
no primary-nbns
no secondary-dns
no secondary-nbns
exit
no http-redirect-policy
no nat-policy
retail-svc-id 35
track-mobility
mac-format "aa:"
no radius-proxy-cache
exit
exit
exit
no shutdown
Downstream traffic can be subjected to aggregate rate-limit per tunnel or per tunnel and per retailer combination (in case of wholesale). Typically a unique SSID is used per retailer for wholesale on the AP, and is reflected via unique dot1Q tag. In the case of soft-GRE tunnel per AP, the tunnel encapsulation is performed on the tunnel ISA. The downstream traffic on the tunnel IOM is received over B-VPLS from the anchor IOM, and is MAC-in-MAC (802.1ah) encapsulated. I-SID in the packet represents the GRE tunnel or tunnel and retailer combination. SAP-egress QoS policy defining queues (with rates), and FC to queue mapping, can be specified under soft-GRE interface. This policy is applicable to all tunnels (or tunnel and SSID combinations) associated with the soft-GRE interface, and is attached to corresponding I-SIDs on the B-VPLS SAP. Traffic is shaped into these queues based on configured queue rates. An aggregate rate-limit applied across queues on an I-SID (representing tunnel or tunnel and retailer combination) can be configured under soft-GRE interface. The aggregate rate-limit works in conjunction with a port-scheduler. The port-scheduler corresponds to the internal port between tunnel ISA and its carrier IOM, and is specified at the WLAN-GW IOM group level. The rate-limit includes the B-VPLS encapsulation overhead. The configuration is shown in Figure 144. Queues per I-SID also work with virtual-scheduler (with or without a port scheduler). Virtual-scheduling and aggregate-rate enforcement are mutually exclusive. Configuration is shown in
Figure 145. Egress SAP QoS policy, aggregate rate-limit, port-scheduler, and virtual-schedulers are described in SROS QoS guide. SAP egress QoS policy associated with soft-GRE interface implicitly creates queues (and scheduler association) on ISIDs as corresponding soft-GRE tunnels are created. General ISID queuing and shaping is defined in SROS services guide.
config>qos#
port-scheduler-policy “lo-gre-port-sched”
max-rate 5000
level 1 rate 1000 cir-rate 1000
level 8 rate 500 cir-rate 500
exit
exit
config>qos>
sap-egress 3 create
queue 1 create
rate 300
port-parent level 1 weight 10 cir-level 1 weight 10
exit
queue 2 create
rate 100
port-parent level 8 weight 10 cir-level 8 weight 10
fc af create
dot1p 2
de-markweight
exit
fc be create
queue 1
dot1p 0
de-mark
exit
fc ef create
queue 2
dot1p 5
de-mark
exit
exit
exit
config>service>ies>sub-if>grp-if>soft-gre>egress
agg-rate-limit 2000
hold-time 300
qos 3
shaping per-tunnel
shape-multi-client
exit
config>isa>wlan-gw-group#
active-iom-limit 1
tunnel-port-policy " lo-gre-port-sched "
iom 2
iom 3
no shutdown
exit
// hierarchical virtual scheduler
config>qos#
scheduler-policy “virtual-sched-policy”
tier1
scheduler “all-traffic” create
rate 10000
exit
exit
tier2
scheduler “non-voice” create
parent all-traffic cir-level 1
rate 9000
exit
scheduler “voice” create
parent all-traffic level 2 cir-level 2
rate 3000
exit
exit
exit
config>qos>
sap-egress 3 create
queue 1 create
parent “non-voice”
rate 2000 cir 1000
exit
queue 2 create
parent “voice”
rate 500 cir-rate 500
fc be create
queue 1
dot1p 0
de-mark
exit
fc ef create
queue 2
dot1p 5
de-mark
exit
exit
exit
config>service>ies>sub-if>grp-if>soft-gre>egress
hold-time 300
qos 3
scheduler-policy “virt-sched-policy”
shaping per-tunnel
shape-multi-client
exit
show router 50 wlan-gw soft-gre-tunnels detail
===============================================================================
Soft GRE tunnels
===============================================================================
Remote IP address : 201.1.1.2
Local IP address : 50.1.1.1
ISA group ID : 1
ISA group member ID : 1
Time established : 2012/06/19 20:31:36
Number of UE : 1
Tunnel QoS
----------
Operational state : active
Number of UE : 1
Remaining hold time (s) : N/A
Service Access Points(SAP)
===============================================================================
Service Id : 2147483650
SAP : 2/1/lo-gre:1 Encap : q-tag
Description : Internal SAP
Admin State : Up Oper State : Up
Flags : None
Multi Svc Site : None
Last Status Change : 06/19/2012 07:13:31
Last Mgmt Change : 06/19/2012 20:30:24
-------------------------------------------------------------------------------
Encap Group Specifics
-------------------------------------------------------------------------------
Encap Group Name : _tmnx_SHAPER_GR000 Group Type : ISID
Qos-per-member : TRUE
Members :
1
-------------------------------------------------------------------------------
QOS
-------------------------------------------------------------------------------
E. qos-policy : 3 Q Frame-Based Acct: Disabled
E. Sched Policy : E. Agg-limit : 4000
-------------------------------------------------------------------------------
Encap Group Member 1 Base Statistics
-------------------------------------------------------------------------------
Last Cleared Time : N/A
Forwarding Engine Stats
Packets Octets
For. InProf : 0 0
For. OutProf : 0 0
Dro. InProf : 0 0
Dro. OutProf : 0 0
-------------------------------------------------------------------------------
Encap Group Member 1 Queue Statistics
-------------------------------------------------------------------------------
Packets Octets
Egress Queue 1
For. InProf : 0 0
For. OutProf : 0 0
Dro. InProf : 0 0
Dro. OutProf : 0 0
===============================================================================
-------------------------------------------------------------------------------
No. of tunnels: 1
===============================================================================
show qos scheduler-hierarchy sap 2/1/lo-gre:1 encap-group "_tmnx_SHAPER_GR000" member 1 detail
===============================================================================
Scheduler Hierarchy - Sap 2/1/lo-gre:1
===============================================================================
Egress Scheduler Policy :
-------------------------------------------------------------------------------
Legend :
(*) real-time dynamic value
(w) Wire rates
B Bytes
-------------------------------------------------------------------------------
Root (Egr)
| slot(2)
|--(Q) : -2147483646->2/1/lo-gre:1->EG(_tmnx_SHAPER_GR000):1->1 (Port 2/1/lo-gre Orphan)
| | AdminPIR:10000000 AdminCIR:0
| | AvgFrmOv:100.00
| | AdminPIR:10000000(w) AdminCIR:0(w)
| | CBS:0 B MBS:12582912 B
| | Depth:0 B HiPrio:1376256 B
| | MaxAggRate:4000(w) CurAggRate:0(w)
| |
| | [Within CIR Level 0 Weight 0]
| | Assigned:0(w) Offered:0(w)
| | Consumed:0(w)
| |
| | [Above CIR Level 1 Weight 0]
| | Assigned:4000(w) Offered:0(w)
| | Consumed:0(w)
| |
| | TotalConsumed:0
| | OperPIR:4000 OperCIR:0
| |
| | PktByteOffset:add 0*
| | OnTheWireRates:false
| | ATMOnTheWireRates:false
| | LastMileOnTheWireRates:false
show router 50 wlan-gw soft-gre-tunnels detail
===============================================================================
Soft GRE tunnels
===============================================================================
Remote IP address : 201.1.1.2
Local IP address : 50.1.1.1
ISA group ID : 1
ISA group member ID : 1
Time established : 2012/06/19 20:43:03
Number of UE : 1
Tunnel QoS
----------
Operational state : active
Number of UE : 1
Remaining hold time (s) : N/A
Service Access Points(SAP)
===============================================================================
Service Id : 2147483650
SAP : 2/1/lo-gre:1 Encap : q-tag
Description : Internal SAP
Admin State : Up Oper State : Up
Flags : None
Multi Svc Site : None
Last Status Change : 06/19/2012 07:13:31
Last Mgmt Change : 06/19/2012 20:30:24
-------------------------------------------------------------------------------
Encap Group Specifics
-------------------------------------------------------------------------------
Encap Group Name : _tmnx_SHAPER_GR000 Group Type : ISID
Qos-per-member : TRUE
Members :
1
-------------------------------------------------------------------------------
QOS
-------------------------------------------------------------------------------
E. qos-policy : 3 Q Frame-Based Acct: Disabled
E. Sched Policy : virtual_scheduler_policy E. Agg-limit : -1
-------------------------------------------------------------------------------
Encap Group Member 1 Base Statistics
-------------------------------------------------------------------------------
Last Cleared Time : N/A
Forwarding Engine Stats
Packets Octets
For. InProf : 2 752
For. OutProf : 0 0
Dro. InProf : 0 0
Dro. OutProf : 0 0
-------------------------------------------------------------------------------
Encap Group Member 1 Queue Statistics
-------------------------------------------------------------------------------
Packets Octets
Egress Queue 1
For. InProf : 2 752
For. OutProf : 0 0
Dro. InProf : 0 0
Dro. OutProf : 0 0
===============================================================================
-------------------------------------------------------------------------------
No. of tunnels: 1
===============================================================================
show qos scheduler-hierarchy sap 2/1/lo-gre:1 encap-group "_tmnx_SHAPER_GR000" member 1 detail
===============================================================================
Scheduler Hierarchy - Sap 2/1/lo-gre:1
===============================================================================
Egress Scheduler Policy :
-------------------------------------------------------------------------------
Legend :
(*) real-time dynamic value
(w) Wire rates
B Bytes
-------------------------------------------------------------------------------
Root (Egr)
| slot(2)
|--(S) : virtual_scheduler (Port 2/1/lo-gre)
| | AdminPIR:4000 AdminCIR:0(sum)
| |
| | AvgFrmOv:105.31(*)
| | AdminPIR:4212(w) AdminCIR:0(w)
| |
| | [Within CIR Level 0 Weight 0]
| | Assigned:0(w) Offered:0(w)
| | Consumed:0(w)
| |
| | [Above CIR Level 1 Weight 1]
| | Assigned:4212(w) Offered:0(w)
| | Consumed:0(w)
| |
| |
| | TotalConsumed:0(w)
| | OperPIR:3999
| |
| | [As Parent]
| | Rate:3999
| | ConsumedByChildren:0
| |
| |
| |--(Q) : -2147483646->2/1/lo-gre:1->EG(_tmnx_SHAPER_GR000):1->1
| | | AdminPIR:10000000 AdminCIR:0
| | | AvgFrmOv:105.31(*)
| | | CBS:0 B MBS:12582912 B
| | | Depth:0 B HiPrio:1376256 B
| | |
| | | [Within CIR Level 0 Weight 1]
| | | Assigned:0 Offered:0
| | | Consumed:0
| | |
| | | [Above CIR Level 1 Weight 1]
| | | Assigned:3999 Offered:0
| | | Consumed:0
| | |
| | | TotalConsumed:0
| | | OperPIR:4000 OperCIR:0
| | |
| | | PktByteOffset:add 0*
| | | OnTheWireRates:false
| | | ATMOnTheWireRates:false
| | | LastMileOnTheWireRates:false
RADIUS proxy can be configured per service router (base or VPRN). The proxy acts as a server towards the WIFI AP RADIUS clients, and as a client towards RADIUS server(s). Therefore, both client and server parts of the RADIUS proxy need to be configured. The attribute from access-request or response message that serves as the key for the cache is configurable. The key configuration is mandatory for enabling the cache. Commonly the key is the MAC address of the UE, which is available in subsequent DHCP request, and used to locate the cache entry. The UE’s MAC address is typically available in the Calling-station-Id attribute (31) in the RADIUS access-request message from the AP. The proxy can be configured for both authentication and accounting. The radius server policies referred by RADIUS proxy are configured under “aaa” context. If caching is enabled in the RADIUS proxy, the subscriber attributes returned in access-accept are cached. These can include 802.1x credentials/keys, IP address or pool, DNS information, default gateway information, retail-service-id, SLA-profile, filter parameters, charging information, session keys (MS-MPPE-RECV-KEY, MS-MPPE-SEND-KEY) etc. If subsequent DHCP DISCOVER is not received within the configured timeout, the cache entry is removed.
config>service>ies>
config>service>vprn>
description "Default Description For VPRN ID 50"
interface "listening_radius_server" create
address 9.9.9.9/32
loopback
exit
radius-proxy
server "radius_proxy" purpose accounting authentication create
cache
key packet-type request attribute-type 31
timeout min 5
track-accounting stop interim-update accounting-on accounting-off
no shutdown
exit
default-accounting-server-policy "radius_acct_server_policy"
default-authentication-server-policy "radius_Auth_server_policy"
interface "listening_radius_server"
load-balance-key attribute-type 102 vendor 5
secret "AQepKzndDzjRI5g38L3LbbN3E8qualtn" hash2
send-accounting-response
no shutdown
exit
config>service>vprn
radius-server
server "radius_server" address 100.100.100.2 secret "9OkclHYDDbo9eHrzFmuxiaO/LAft3Pw"
hash2 port 1812 create
exit
exit
config>aaa
radius-server-policy "radius_server_policy" create
servers
router 50
access-algorithm hash-based
source-address 10.1.1.1
timeout min 1
hold-down-time 2
server 1 name "radius_server"
exit
config>subscriber-mgmt
local-user-db "radius_ludb" create
dhcp
match-list service-id
host "default" create
auth-policy "auth_policy_1"
match-radius-proxy-cache
fail-action continue
match mac
server router 50 name "radius_proxy"
exit
no shutdown
exit
no shutdown
exit
exit
config>subscriber-mgmt
sla-profile "portal-redirect" create
ingress
ip-filter 10
exit
exit
exit
system>config>filter
ip-filter 10 create
entry 1 create
match protocol udp
dst-port range 67 68
exit
action forward
exit
entry 2 create
match protocol tcp
dst-port eq 80
exit
action http-redirect "http://www.google.ca"
exit
exit
exit
config>service>vprn
dhcp
local-dhcp-server "dhcp" create #### create local DHCP server
pool “1” create #### define Pool
options
dns-server 8.8.8.8 8.8.4.4
lease-time min 5
exit
subnet 128.203.254.180/30 create
options
subnet-mask 255.255.0.0
default-router 128.203.254.181
exit
address-range 128.203.254.182 128.203.254.183
exit
exit
exit
exit
interface "DHCP-lb" create #### loopback interface with DHCP server
address 10.1.1.1/32
local-dhcp-server "dhcp"
loopback
exit
subscriber-interface "sub-int" create #### subscriber interface
address 128.203.254.181/30 #### Subnets out of which UE
address 10.10.0.1/16 ###### addresses are allocated.
group-interface "group-int" softgre create
sap-parameters
sub-sla-mgmt
def-sla-profile "sla_def"
def-sub-profile "sub_def"
sub-ident-policy "sub_ident"
exit
exit
exit
dhcp
proxy-server
emulated-server 10.10.0.1 #### proxy to get IP address from AAA
lease-time min 5 #### or from DHCP server. Can provide
no shutdown #### split lease (shorter lease towards client,
exit #### and longer lease towards AAA or DHCP server.
no option
server 10.1.1.1 #### DHCP local server
trusted
lease-populate 32000
gi-address 128.203.254.181
user-db "radius_ludb" #### LUDB for proxy cache co-relation
no shutdown
exit
exit
config>service>ies>
config>service>vprn>
subscriber-interface <if-name>
group-interface <if-name> softgre
soft-gre
[no] router (base | <vprn-id>) # tunnel service context
[no] wlan-gw-group <group-id>
....snip
mobility
[no] trigger {data | iapp}
[no] hold-time <seconds> // [0..255 secs]
exit
exit
exit
config>service>ies>
config>service>vprn>
subscriber-interface <if-name>
group-interface <if-name> softgre
soft-gre
[no] router (base | <vprn-id>) # tunnel service context
[no] wlan-gw-group <group-id>
....snip
vlan-tag-ranges # Precedence for retail-service-id:
# RADIUS, vlan-retail-service-map, default-retail-svc
[no] vlan start <start-tag> end <end-tag> retail-svc-id <svc-id>
[no] default-retail-svc-id
exit
exit
exit
config>subscriber-mgmt>wlan-gw
serving-network mcc “123” mnc “45”
mgw-profile “pgw-west-mno1” [create]
description “mgw profile for MNO north-east PGW”
interface-type s2b
ip-ttl 255
keep-alive interval 60 retry-count 3 timeout 10
message-retransmit timeout 30 retry-count 3
exit
config>router
config>service>vprn
apn “internet.mno1.apn”
mgw-map
address 33.1.1.1/32 “pgw-west-mno1”
address 34.1.1.1/32 “ggsn-east-mno1”
exit
config>service>vprn>dns
primary-dns 130.1.1.1
secondary-dns 131.1.1.1
tertiary-dns 132.1.1.1
ipv4-source-address 170.1.1.1
exit
Table 20describes 3GPP attributes and ALU specific attributes related to GTP signaling are supported.
show router wlan-gw
mobile-gateway – Display mobile gateway information
mgw-map – Display the mobile gateway map
mgw-address-cache – Display the mobile gateway’s DNS lookup address cache.
show router wlan-gw mgw-address-cache [apn <apn-string>]
<apn-string> : [80 chars max]
show router wlan-gw mobile-gateway
[mgw-profile <profile-name>] [local-address <ip-address>] [control <protocol>]
remote-address <ip-address> [udp-port <port>]
remote-address <ip-address> [udp-port <port>] statistics
<profile-name> : [32 chars max]
<ip-address> : ipv4-address - a.b.c.d
<ipv6-address - x:x:x:x:x:x:x:x (eight 16-bit pieces)
x:x:x:x:x:x:d.d.d.d
x - [0..FFFF]H
d - [0..255]D
<protocol> : gtpv1-c|gtpv2-c
<port> : [1..65535]
===============================================================================
Mobile gateways
===============================================================================
Remote address : 5.20.1.2
UDP port : 2123
-------------------------------------------------------------------------------
State : up
Local address : 5.20.1.3
Profile : default
Control protocol : gtpv1-c
Restart count : 3
Time : 2012/06/28 08:07:11
===============================================================================
Mobile Gateway address cache
===============================================================================
APN : full.dotted.apn.apn.epc.mnc010.mcc206.3gppnetwork.org
-------------------------------------------------------------------------------
Mobile Gateway address : 5.20.1.2
Time left (s) : 3587
-------------------------------------------------------------------------------
No. of cache entries: 1
No. of Mobile gateways: 1
===============================================================================
show subscriber-mgmt wlan-gw
gtp-session - Display GTP session information
gtp-statistics - Display GTP statistics
mgw-profile - Display Mobile Gateway profile information
show subscriber-mgmt wlan-gw gtp-session
imsi <imsi> apn <apn-string>
[mgw-address <ip-address>] [mgw-router <router-instance>] [remote-control-teid <teid>] [local-
control-teid <teid>] [detail]
imsi <imsi>
<imsi> : [a string of digits between 9 and 15 long]
<apn-string> : [80 chars max]
<ip-address> : ipv4-address - a.b.c.d
<ipv6-address> : x:x:x:x:x:x:x:x (eight 16-bit pieces)
x:x:x:x:x:x:d.d.d.d
x - [0..FFFF]H
d - [0..255]D
<router-instance> : <router-name>|<service-id>
router-name - "Base"
service-id - [1..2147483647]
<teid> : [1..4294967295]
show subscriber-mgmt wlan-gw gtp-statistics
show subscriber-mgmt wlan-gw mgw-profile
<profile-name>
<profile-name> associations
mgw-profile
<profile-name> : [32 chars max]
===============================================================================
GTP sessions
===============================================================================
IMSI : 206100000000041
APN : full.dotted.apn.mnc010.mcc206.gprs
-------------------------------------------------------------------------------
Mobile Gateway router : "Base"
Mobile Gateway address : 5.20.1.2
Remote control TEID : 1119232
Local control TEID : 4293918976
Bearer 5 rem TEID : 1074861061
Bearer 5 loc TEID : 4293919013
-------------------------------------------------------------------------------
No. of GTP sessions: 1
===============================================================================
===============================================================================
WLAN Mobile Gateway profile "default"
===============================================================================
Description : (Not Specified)
Retransmit timeout (s) : 5
Retransmit retries : 3
Keepalive interval (s) : 60
Keepalive retries : 4
Keepalive retry timeout (s) : 5
Time to live : 255
Interface type : s2a
Last management change : 06/28/2012 06:05:30
===============================================================================
=============================================================================
GTP statistics
=============================================================================
tx echo requests : 1
tx echo responses : 0
tx errors : 0
rx echo requests : 0
rx echo responses : 1
rx errors : 0
rx version not supported : 0
rx zero TEID responses : 0
path faults : 0
path restarts : 0
tx invalid msgs : 0
tx create PDP context requests : 0
tx create PDP context responses : 0
tx delete PDP context requests : 0
tx delete PDP context responses : 0
tx create session requests : 1
tx create session responses : 0
tx delete session requests : 0
tx delete session responses : 0
tx delete bearer requests : 0
tx delete bearer responses : 0
tx error indication count : 0
rx invalid msgs : 0
rx create PDP context requests : 0
rx create PDP context responses : 0
rx delete PDP context requests : 0
rx delete PDP context responses : 0
rx create session requests : 0
rx create session responses : 1
rx delete session requests : 0
rx delete session responses : 0
rx delete bearer requests : 0
rx delete bearer responses : 0
rx error indication count : 0
rx invalid pkt length : 0
rx unknown pkts : 0
rx missing IE pkts : 0
rx bad IP header pkts : 0
rx bad UDP header pkts : 0
============================================================================
“Migrant users” are UEs that connect to an SSID, but move out of the range of the access-point before initiating or completing authentication. For open-SSIDs, a migrant user may stay in the range of the access-point just enough to get a DHCP lease from the WLAN-GW. In real WIFI deployments with portal authentication, it has been observed that a large percentage of users are migrant, such as get a DHCP lease but do not initiate or complete authentication. Prior to this feature, an ESM host is created when DHCP completes. This results in consumption of resources on both CPM and IOM, limiting the ESM scale and performance for fully authenticated active users. This feature adds support to only create an ESM host after a user has been fully authenticated, either via web portal or with a AAA server based on completing EAP exchange. In addition, with this feature L2-aware NAPT is enabled on the ISA, such that each UE gets the same shared configured inside IP@ from the ISA via DHCP. Until a user is authenticated, forwarding of user traffic is constrained (via policy) to only access DNS and portal servers. Each user is allocated a small number of configured NAT outside ports to minimize public IP address consumption for unauthenticated users. Once the user is successfully authenticated, as indicated via a RADIUS COA on successful portal authentication, an ESM host is created, and the L2-aware NAT is applied via a normal per-subscriber NAT policy. The inside IP address of the user does not change. The outside IP pool used is as per the NAT policy, and the L2-aware NAT could be 1:1 or NAPT with larger number of outside ports than in the un-authenticated phase. If a user is already pre-authenticated (for example, if RADIUS server remembers the MAC@ of the UE from previous successful portal authentication), then the initial access-accept from RADIUS will trigger the creation of the ESM host.
However, if a user needs portal authentication (as indicated in access-accept), then while the user is pending authentication, forwarding is restricted to DNS and portal servers via the redirect policy. The redirect policy is an IP ACL that restricts forwarding based on IP destination, destination port, and protocol, and also specifies http-redirect for http traffic that does not match any of the forwarding rules. The URL for re-direct is configured in the redirect policy or can be provided in authentication-accept. A Maximum of 16 redirect policies can be created in the system, with a maximum of 64 forward rules across all redirect policies. During this “authentication pending” phase all forwarded traffic is subjected to L2-aware NAT on the ISA. The NAT policy to use for these users can be configured on the soft-GRE interface or per VLAN range under the soft-GRE interface. After an access-accept has been received from RADIUS for such a user, the next http packet triggers a redirect function from the ISA, and an http 302 is sent to the client. The redirect can be configured to append original-URL, subscriber’s MAC address and IP address to the redirect URL sent back in http 302. The client presents its credentials to the portal and once it is successfully authenticated, a COA is generated from the RADIUS server (triggered by the portal). The COA message triggers creation of an ESM host with the subscriber configuration contained in the COA such as subscriber-profile, SLA-profile, NAT-profile and application-profile. From this point normal ESM based forwarding occurs for the subscriber.
With “data-triggered-ue-creation” configured under soft-GRE group interface or per VLAN range (such as, per one or more SSIDs), first L3 packet received on WLAN-GW ISA from an unknown subscriber (with no prior state, such as an unknown MAC address) will trigger RADIUS authentication from the ISA. The authentication is based on configured isa-radius-policy (under aaa context). If RADIUS authentication succeeds, then ESM host is created from the CPM. The ESM host can get deleted based on idle-timeout. Data-triggered authentication and subscriber creation enables stateless inter WLAN-GW redundancy, as shown in Figure 151. If the AP is configured with a backup WLAN-GW address (or FQDN), it can tunnel subscriber traffic to the backup WLAN-GW, when it detects failure of the primary WLAN-GW (based on periodic liveness detection). With “data-triggered-ue-creation” configured, the first data packet results in authentication and ESM host creation on the backup WLAN-GW. If the subscriber had obtained an IP address via DHCP with L2-aware NAT on the primary WLAN-GW, it can retain it with L2 aware NAT on the backup WLAN-GW. The NAT outside pool for the subscriber changes on the backup WLAN-GW based on local configuration. For a subscriber that needs to be anchored on GGSN/PGW (as indicated via RADIUS access-accept), RADIUS server will return the IP address of PGW/GGSN where the UE was anchored before the switch-over. GTP tunnel is then signaled with “handover indication” set. The PGW/GGSN must return the requested IP address of the UE, which is the address with which the UE originated data packet that triggered authentication.
#------------------------------------------------------
NAT configuration for migrant and authenticated users
#------------------------------------------------------
service
vprn 300 customer 1 create
nat
inside
l2-aware
address 21.1.1.1/16
exit
exit
outside
pool "migrant_outside_pool" nat-group 1 type wlan-gw-anchor create
address-range 22.22.0.0 22.22.0.255 create
exit
no shutdown
exit
pool "wifi_outside_pool" nat-group 1 type l2-aware create
address-range 22.0.0.0 22.0.0.255 create
exit
no shutdown
exit
exit
exit
exit
nat
nat-policy "migrant_nat_300" create
pool "migrant_outside_pool" router 300
timeouts
tcp-established min 1
exit
exit
nat-policy "wifi_nat_300" create
pool "wifi_outside_pool" router 300
exit
exit
#--------------------------------------------------------------------------------
echo "AAA Configuration" - ISA-RADIUS-Policy for authentication from WLAN-GW ISA
#--------------------------------------------------------------------------------
aaa
isa-radius-policy "wifi_isa_radius" create
description "Default authentication policy for migrant users"
password "i2KzVe9XPxgy4KN2UEIf6jKeMT3X4mT6JcUmnnPZIrw" hash2
servers
router "Base"
source-address-range 100.100.100.4
server 1 create
authentication
coa
ip-address 100.100.100.2
secret "ABIQRobhHXzq13ycwqS74FSrj.OdTwh5IdjhRB.yAF." hash2
no shutdown
exit
exit
exit
radius-server-policy "radius_server_policy" create
servers
router "Base"
server 1 name "radius_server"
exit
exit
exit
#--------------------------------------------------
echo "Subscriber-mgmt Configuration" - Redirect Policy
#--------------------------------------------------
subscriber-mgmt
http-redirect-policy "migrant_redirect" create
url "portal.ipdtest.alcatel-lucent.com:8081/start/?mac=$MAC&url=$URL&ip=$IP"
portal-hold-time 10
forward-entries
dst-ip 8.8.8.1 protocol tcp dst-port 8081
dst-ip 8.8.8.7 protocol tcp dst-port 8007
dst-ip 8.8.8.8 protocol udp dst-port 53
exit
exit
exit
service
#----------------------------------------------------------------
echo "migrant user configuration under soft-GRE group interface”
#---------------------------------------------------------------
vprn 300 customer 1 create
subscriber-interface "ies-4-20.1.1.1" create
address 20.1.1.1/16
group-interface "grp-vprn_ue-2/1/2:51" softgre create
sap-parameters
sub-sla-mgmt
def-sla-profile "slaprof_1"
def-sub-profile "subprof_1"
sub-ident-policy "identprof"
exit
exit
dhcp
proxy-server
emulated-server 20.1.1.1
no shutdown
exit
trusted
lease-populate 32767
user-db "radius_ludb"
no shutdown
exit
host-connectivity-verify interval 1000
soft-gre
gw-address 50.1.1.4
mobility
hold-time 0
trigger data iapp
exit
router 50
wlan-gw-group 1
vlan-tag-ranges
range start 100 end 100
authentication
authentication-policy "wifi_isa_radius"
exit
data-triggered-ue-creation
dhcp
l2-aware-ip-address 21.1.1.2
primary-dns 130.1.1.1
secondary-dns 131.1.1.1
no shutdown
exit
nat-policy "migrant_nat_4"
exit
exit
no shutdown
exit
exit
exit
exit
RADIUS proxy is extended to listen for incoming IPv6 RADIUS messages from IPv6 RADIUS clients on AP/CPEs. The listening interface that the RADIUS proxy binds to must be configured with an IPv6 address as shown in Figure 155. The IPv6 RADIUS proxy is solely for DHCPv4-based UEs behind IPv6 only AP/CPEs (IPv6-capable UEs are not supported in this release). All RADIUS-proxy functions (including caching, correlation with DHCPv4, and mobility tracking) are supported identically to existing IPv4 client-side RADIUS-proxy.




