Event and accounting logs
This chapter provides information about configuring event and accounting logs on the 7705 SAR.
Topics in this chapter include:
Logging overview
The two primary types of logging supported on the 7705 SAR are:
The log files saved in local storage can be encrypted using the AES-256-CTR algorithm.
configure
log
encryption-key key [hash | hash2]- The encrypted log files can be decrypted offline using the appropriate OpenSSL command:
openssl enc -aes-256-ctr -pbkdf2 -d -in <log file encrypted> -out <output log file> -p -pass pass:<passphrase>- When an encrypted log file is opened in a text editor, editing or viewing the file contents is not possible because the entire file is encrypted.
Event logging
Event logging controls the generation, dissemination and recording of system events for monitoring status and troubleshooting faults within the system. Events are messages generated by the system by applications or processes within the 7705 SAR. The 7705 SAR groups events into four major categories or event sources:
security events – security events are generated by the SECURITY application and pertain to attempts to breach system security
change events – change events are generated by the USER application and pertain to the configuration and operation of the node
debug events – debug events are generated by the DEBUG application and pertain to trace or other debugging information
main events – main events pertain to 7705 SAR applications that are not assigned to other event categories/sources
The applications listed above have the following properties:
a timestamp in UTC or local time
the generating application
a unique event ID within the application
a router name identifying the VRF-ID that generated the event
a subject identifying the affected object
a short text description
Event control assigns the severity for each application event and determines whether the event should be generated or suppressed. The severity numbers and severity names supported in the 7705 SAR conform to ITU standards M.3100 X.733 and X.21 and are listed in the following table.
Severity number |
Severity name |
|---|---|
1 |
Cleared |
2 |
Indeterminate (info) |
3 |
Critical |
4 |
Major |
5 |
Minor |
6 |
Warning |
Event control maintains a count of the number of events generated (logged) and dropped (suppressed) for each application event. The severity of an application event can be configured in event control.
An event log within the 7705 SAR associates the event sources with logging destinations. Examples of logging destinations include the console session, memory logs, file destinations, SNMP trap groups, and syslog destinations. A log filter policy can be associated with the event log to control which events are logged in the event log based on combinations of application, severity, event ID range, and the subject of the event.
Accounting logs
The 7705 SAR accounting logs collect comprehensive statistics to support several billing models. The 7705 SAR collects accounting data on services and on network interfaces on a per-forwarding class basis.
In addition to gathering information critical for service billing, accounting records can be analyzed to provide insight about customer service trends for potential service revenue opportunities. Accounting statistics on network ports can be used to track link utilization and network capacity planning. This information is valuable for traffic engineering and capacity planning within the network core.
The 7705 SAR also supports SAA accounting policies.
Accounting statistics are collected according to the parameters defined within the context of an accounting policy. Accounting policies are applied to customer service access points (SAPs) and network interfaces. Accounting statistics are collected by counters for individual service queues defined on the customer’s SAPs or by the counters within forwarding class (FC) queues defined on the network ports.
The type of record defined within the accounting policy determines where a policy is applied, which statistics are collected, and the time interval at which to collect statistics.
The only supported destination for an accounting log is a compact flash system device (cf3: on all platforms; also cf1: or cf2: on the 7705 SAR-18). Accounting data is stored within a standard directory structure on the device in compressed XML format.
Log destinations
Both event logs and accounting logs use a common mechanism for referencing a log destination. The 7705 SAR supports the following log destinations:
An event log can be associated with multiple event sources, but it can only have a single log destination. Any of the supported log destinations can be configured for an event log.
For an accounting log, the only type of log destination that can be configured is a file destination.
Console
Sending events to a console destination means the message will be sent to the system console. The console device can be used as an event log destination.
Session
A session destination is a temporary log destination that directs entries to the active Telnet or SSH session for the duration of the session. When the session is terminated, for example, when the user logs out, the to session configuration is removed. Event logs configured with a session destination are stored in the configuration file but the to session part of the configuration is not stored. Event logs can direct log entries to the session destination.
Memory logs
A memory log is a circular buffer. When the log is full, the oldest entry in the log is replaced with the new entry. When a memory log is created, the specific number of entries it can hold can be specified; otherwise, it will assume a default size. An event log can send entries to a memory log destination.
Log files
Log files can be used by both event logs and accounting logs and are stored on the compact flash device (cf3: on all platforms; also cf1: or cf2: on the 7705 SAR-18) in the file system. A log file destination is configured using the config>log>file-id log-file-id command. A log file destination is applied to an event log using the config>log>log-id>to file command and to an accounting file using the config>log>accounting-policy>to file command.
A log file is identified by a single log file ID, but a log file is generally composed of a number of individual files in the file system. A log file is configured with the following parameters:
rollover: represents the length of time, expressed in minutes, that an individual log file should be written to before a new file is created for the relevant log file ID. The rollover time is checked only when an update to the log is performed. Thus this rule is subject to the incoming rate of the data being logged. For example, if the rate is very low, the actual rollover time may be longer than the configured value.
retention time: for a log file, specifies the amount of time the file should be retained on the system based on the creation date and time of the file. The retention time is used as a factor to determine which files should be deleted first if the file system device nears 100% usage.
When a log file is created, only the compact flash device for the log file is specified. Log files are created in specific subdirectories with standardized names depending on the type of information stored in the log file.
Event log files
Event log files are always created in the \log directory on the compact flash device. The naming convention for event log files is:
logeeff-timestamp
where:
-
ee is the event log ID
-
ff is the log file destination ID
-
timestamp is the timestamp when the file is created in the form of yyyymmdd-hhmmss
where:
-
yyyy is the four-digit year (for example, 2015)
-
mm is the two-digit number representing the month (for example, 12 for December)
-
dd is the two-digit number representing the day of the month (for example, 03 for the 3rd of the month)
-
hh is the two-digit hour in a 24-hour clock (for example, 04 for 4 a.m.)
-
mm is the two-digit minute (for example, 30 for 30 minutes past the hour)
- ss is the two-digit second (for example, 14 for 14 seconds)
-
Accounting log files
Accounting log files are created in the \act-collect directory on the compact flash device. The naming convention for accounting logs is:
actaaff-timestamp.xml.gz
where:
aa is the accounting policy ID
ff is the log file destination ID
timestamp is the timestamp when the file is created, in the same form as for event logs.
Accounting logs are .xml files that are created in a compressed format and have a .gz extension.
The \act-collect directory is where active accounting logs are written. When an accounting log is rolled over, the active file is closed and archived in the \act directory before a new active accounting log file is created in \act-collect.
SNMP trap group
An event log can be configured to send events to SNMP trap receivers by specifying an SNMP trap group destination.
An SNMP trap group can have multiple trap targets. Each trap target can have different operational parameters.
A trap destination has the following properties:
the IP address of the trap receiver (IPv4 or IPv6)
the UDP port used to send the SNMP trap
SNMP version (v1, v2c, or v3) used to format the SNMP notification
SNMP community name for SNMPv1 and SNMPv2c receivers
security name and level for SNMPv3 trap receivers
For SNMP traps that will be sent out-of-band through the Management Ethernet port on the CSM, the source IP address of the trap is the IP interface address defined on the Management Ethernet port. For SNMP traps that will be sent in-band, the source IP address of the trap is the system IP address of the 7705 SAR.
Each trap target destination of a trap group receives the identical sequence of events as defined by the log ID and the associated sources and log filter applied.
Syslog
An event log can be configured to send events to one syslog destination. Syslog destinations have the following properties:
syslog server IP address (IPv4 or IPv6)
the UDP port used to send the syslog message
the Syslog Facility Code
the Syslog Severity Threshold (0 to 7) (events exceeding the configured level will be sent)
Because syslog uses eight severity levels, whereas the 7705 SAR uses six internal severity levels, the severity levels are mapped to syslog severities. The following table displays the severity level mappings to syslog severities.
7705 SAR severity level |
Syslog severity level (highest to lowest) |
Syslog configured severity |
Definition |
|---|---|---|---|
3 critical |
0 |
emergency |
System is unusable |
1 |
alert |
Action must be taken immediately |
|
4 major |
2 |
critical |
Critical conditions |
5 minor |
3 |
error |
Error conditions |
6 warning |
4 |
warning |
Warning conditions |
5 |
notice |
Normal but significant condition |
|
1 cleared 2 indeterminate |
6 |
info |
Informational messages |
7 |
debug |
Debug-level messages |
Event logs
This section contains the following topics:
Event logs are the means of recording system-generated events for later analysis. Events are messages generated by the system by applications or processes within the 7705 SAR.
The following figure depicts a functional block diagram of event logging.
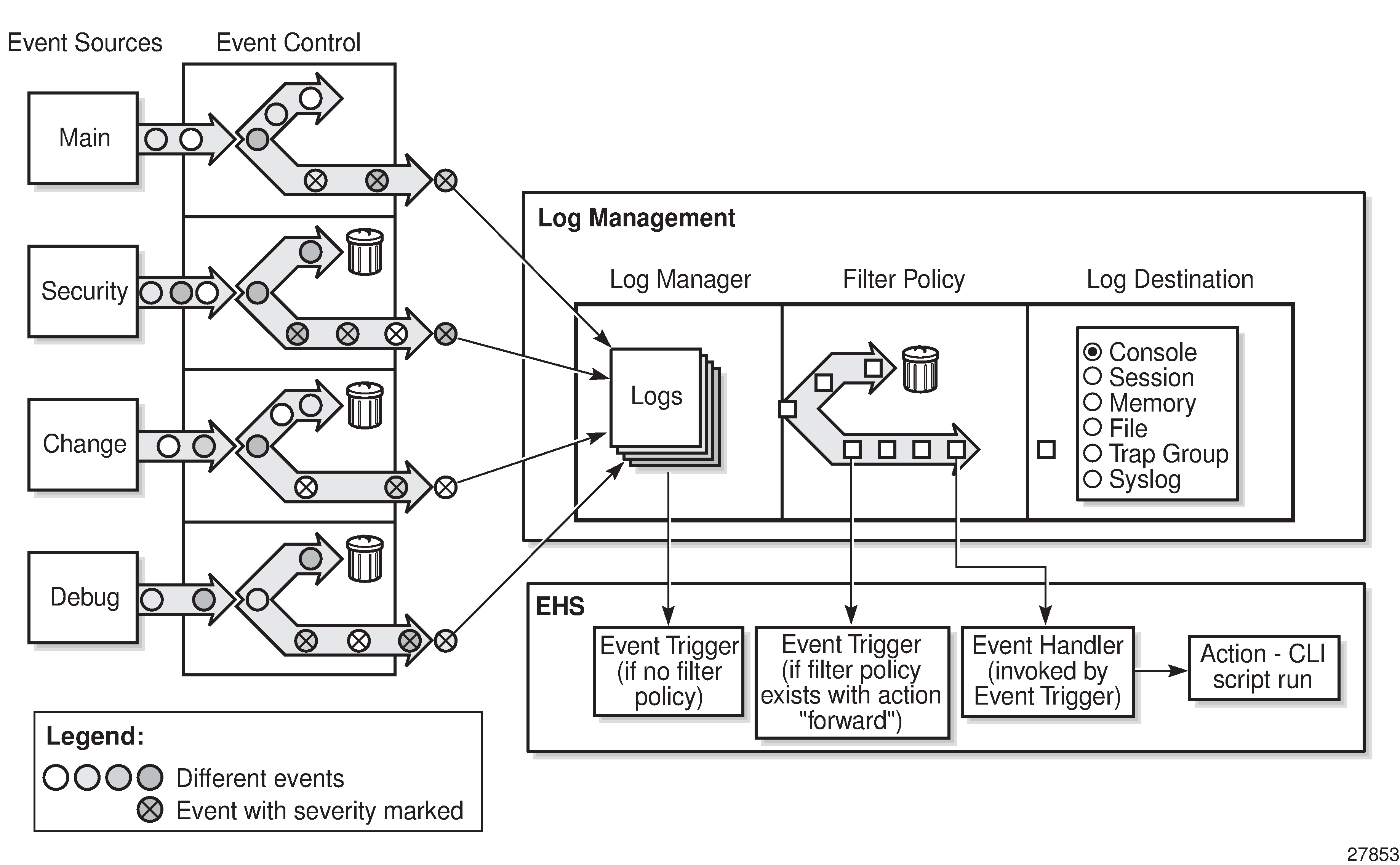
Event sources
In Event logging block diagram, the event sources are the main categories of events that feed the log manager.
-
security – the security event source is all events that affect attempts to breach system security, such as failed login attempts, attempts to access MIB tables to which the user is not granted access, or attempts to enter a branch of the CLI to which access has not been granted. Security events are generated by the SECURITY application.
-
change – the change activity event source is all events that directly affect the configuration or operation of the node. Change events are generated by the USER application.
-
debug – the debug event source is the debugging configuration that has been enabled on the system. Debug events are generated by the DEBUG application.
-
main – the main event source receives events from all other applications within the 7705 SAR
The show log applications command displays all applications:
*A:ALU-48# show log applications
==================================
Log Event Application Names
==================================
Application Name
----------------------------------
APS
...
BGP
CHASSIS
CPMHWFILTER
...
IGMP_SNOOPING
IP
IPSEC
...
MIRROR
MLD
MLD_SNOOPING
...
ROUTE_POLICY
RSVP
...
VRTR
FIREWALL
...
==================================
*A:ALU-48#Event control
Event control preprocesses the events generated by applications before the event is passed into the main event stream. Event control assigns a severity to application events and can either forward the event to the main event source or suppress the event. Suppressed events are counted in event control, but these events do not generate log entries as they never reach the log manager.
Simple event throttling is another method of event control and is configured in the same way as the generation and suppression options. See Simple logger event throttling.
Events are assigned a default severity level in the system, but the application event severities can be changed by the user.
Application events contain an event number and description that describes why the event is generated. The event number is unique within an application, but the number can be duplicated in other applications.
The following example, generated by querying event control for application-generated events, displays a partial list of event numbers and names.
router# show log event-control
=======================================================================
Log Events
=======================================================================
Application
ID# Event Name P g/s Logged Dropped
-----------------------------------------------------------------------
ATM:
2011 tAtmPlcpSubLayerClear MI gen 0 0
2012 tAtmEpOutOfPeerVpiOrVciRange WA gen 0 0
2013 tAtmMaxPeerVccsExceeded WA gen 0 0
...
CHASSIS:
2001 cardFailure MA gen 0 0
2002 cardInserted MI gen 7 0
2003 cardRemoved MI gen 0 0
...
DEBUG:
L 2001 traceEvent MI gen 0 0
EFM_OAM:
2001 tmnxDot3OamPeerChanged MI gen 0 0
2002 tmnxDot3OamLoopDetected MI gen 0 0
FILTER:
2001 tIPFilterPBRPacketsDrop WA gen 0 0
2002 tFilterEntryActivationFailed WA gen 0 0
2003 tFilterEntryActivationRestored WA gen 0 0
GSMP:
2001 tmnxAncpIngRateMonitorEvent WA gen 0 0
L 2002 tmnxAncpIngRateMonitorEventL WA gen 0 0
2003 tmnxAncpEgrRateMonitorEvent WA gen 0 0
...
IP:
L 2001 clearRTMError MI gen 0 0
L 2002 ipEtherBroadcast MI gen 0 0
L 2003 ipDuplicateAddress MI gen 0 0
...
LDP:
2001 vRtrLdpStateChange MI gen 0 0
2002 vRtrLdpInstanceStateChange MI gen 0 0
2003 vRtrLdpIfStateChange MI gen 0 0
...
LOGGER:
L 2001 STARTED MI gen 5 0
2002 tmnxLogTraceError CR gen 0 0
2005 tmnxLogSpaceContention MA gen 0 0
...
MPLS:
2001 mplsXCUp WA gen 0 0
2002 mplsXCDown WA gen 0 0
2003 mplsTunnelUp WA gen 0 0
...
NTP:
2001 tmnxNtpAuthMismatch WA gen 0 0
2002 tmnxNtpNoServersAvail MA gen 0 0
2003 tmnxNtpServersAvail MI gen 0 0
...
SYSTEM:
2001 stiDateAndTimeChanged WA gen 0 0
2002 ssiSaveConfigSucceeded MA gen 0 0
2003 ssiSaveConfigFailed CR gen 0 0
...
USER:
L 2001 cli_user_login MI gen 4 0
L 2002 cli_user_logout MI gen 3 0
L 2003 cli_user_login_failed MI gen 0 0
...
VRTR:
2001 tmnxVRtrMidRouteTCA MI gen 0 0
2002 tmnxVRtrHighRouteTCA MI gen 0 0
2003 tmnxVRtrHighRouteCleared MI gen 0 0
...
=======================================================================
router# Log manager and event logs
Events that are forwarded by event control are sent to the log manager. The log manager manages the event logs in the system and the relationships between the log sources, event logs and log destinations, and log filter policies.
An event log has the following properties:
-
a unique log ID
The log ID is a short, numeric identifier for the event log. A maximum of 10 logs can be configured at a time.
-
one or more log sources
The source stream or streams to be sent to log destinations can be specified. The source must be identified before the destination can be specified. The events can be from the main event stream, events in the security event stream, or events in the user activity stream.
-
one event log destination
A log can only have a single destination. The destination for the log ID destination can be one of console, session, syslog, snmp-trap-group, memory, or a file on the local file system.
-
an optional event filter policy
An event filter policy defines whether to forward or drop an event or trap based on match criteria.
Event filter policies
The log manager uses event filter policies to control which events are forwarded or dropped based on various criteria. Like other policies with the 7705 SAR, filter policies have a default action. The default actions are either:
forward
drop
Filter policies also include a number of filter policy entries that are identified with an entry ID and define specific match criteria and a forward or drop action for the match criteria.
Each entry contains a combination of matching criteria that define the application, event number, router, severity, and subject conditions. The entry's action determines how the packets should be treated if they have met the match criteria.
Entries are evaluated in order from the lowest to the highest entry ID. The first matching event is subject to the forward or drop action for that entry.
Filter policy 1001 exists by default and collects events for the Serious Error Log (log ID 100). Filter policy 1001 is preconfigured with one entry that is configured to collect events of major severity or higher. Filter policy 1001 can be reconfigured by the user.
Valid operators are listed in the following table.
Operator |
Description |
|---|---|
eq |
Equal to |
neq |
Not equal to |
lt |
Less than |
lte |
Less than or equal to |
gt |
Greater than |
gte |
Greater than or equal to |
A match criteria entry can include combinations of:
equal to or not equal to a specified system application
equal to, not equal to, less than, less than or equal to, greater than, or greater than or equal to an event number within the application
equal to, not equal to, less than, less than or equal to, greater than, or greater than or equal to a severity level
equal to or not equal to a router name string or regular expression match
equal to or not equal to an event subject string or regular expression match
Event log entries
Log entries that are forwarded to a destination are formatted in a way that is appropriate for the specific destination; for example, whether it is to be recorded to a file or sent as an SNMP trap, but log event entries also have common elements or properties. All application-generated events have the following properties:
-
a timestamp in UTC or local time
-
the generating application
-
a unique event ID within the application
-
a router name identifying the VRF-ID that generated the event
-
a subject identifying the affected object
-
a short text description
The general format for an event in an event log with either a memory, console or file destination is as follows:
nnnn YYYY/MM/DD HH:MM:SS.SS <severity>:<application> # <event_id> <router-
name> <subject> descriptionThe following is an event log example:
475 2015/11/27 00:19:40.38 WARNING: SNMP #2008 Base 1/1/1
"interface 1/1/1 came up" The specific elements that make up the general format are described in the following table.
|
Label |
Description |
|---|---|
|
nnnn |
The log entry sequence number |
|
YYYY/MM/DD |
The UTC date stamp for the log entry YYYY – Year MM – Month DD – Day |
|
HH:MM:SS.SS |
The UTC timestamp for the event HH – Hours (24-hour format) MM – Minutes SS.SS – Seconds |
|
<severity> |
The severity level name of the event CLEARED – a cleared event (severity number 1) INFO – an indeterminate/informational severity event (severity level 2) CRITICAL – a critical severity event (severity level 3) MAJOR – a major severity event (severity level 4) MINOR – a minor severity event (severity level 5) WARNING – a warning severity event (severity 6) |
|
<application> |
The application generating the log message |
|
<event_id> |
The application's event ID number for the event |
|
<router> |
The router name representing the VRF-ID that generated the event |
|
<subject> |
The subject/affected object for the event |
|
<description> |
A text description of the event |
Simple logger event throttling
Simple event throttling provides a mechanism to protect event receivers from being overloaded when a scenario causes many events to be generated in a very short period of time. A throttling rate (events/seconds) can be configured. Specific application events can be configured to be throttled. When the throttling event limit is exceeded in a throttling interval, any further events of that type are dropped and the dropped events counter is incremented. Dropped events counts are displayed with the show>log>event-control command. Events are dropped before being sent to one of the logger event collector tasks. There is no record of the details of the dropped events and therefore no way to retrieve event history data lost by this throttling method.
A particular event type can be generated by multiple managed objects within the system. At the point that this throttling method is applied, the logger application has no information about the managed object that generated the event and cannot distinguish between events generated by object "A" from events generated by object "B". If the events have the same event-id, they are throttled regardless of the managed object that generated them. The logger application also cannot distinguish between events that will be logged to destination log-id <n> from events that will be logged to destination log-id <m>.
Throttle rate applies commonly to all event types. It is not configurable for a specific event type.
A timer task checks for events dropped by throttling when the throttle interval expires. If any events have been dropped, a TIMETRA-SYSTEM-MIB::tmnxTrapDropped notification is sent.
By default, event throttling is set to off for each specific event type. It must be explicitly enabled for each event type where throttling is needed. This makes backwards compatibility of configuration files easier to manage.
Default system logs
Log 99 is a preconfigured memory-based log that collects events from the main event source (that is, not the security, debug, or change source). Log 100 is preconfigured to be associated with filter policy 1001, which is preconfigured to collect events of major severity or higher. Log 100 can be reconfigured by the user.
Log 99 and log 100 exist by default.
The following example displays the log 99 and log 100 configurations.
ALU-1>config>log# info detail
#------------------------------------------
echo "Log Configuration "
#------------------------------------------
...
log-id 99
description "Default system log"
no filter
time-format utc
from main
to memory 500
no shutdown
exit
log-id 100
description "Default Serious Errors Log"
filter 1001
time-format utc
from main
to memory 500
no shutdown
exit
----------------------------------------------Event handling system
The event handling system (EHS) is a tool that enables operator-defined behavior to be configured on the 7705 SAR. The operator can define a CLI script that the router executes in response to a log event. The event is referred to as the trigger, where the trigger can be all or part of any event message. Regular expression (regexp) matching can be done on various fields in the log event to give flexibility in the trigger definition.
EHS gives operators the flexibility to configure the 7705 SAR to take actions based on specific events that cannot be done by protocols or services. For example, event-triggered actions can:
help with network convergence in response to a specific event
provide automatic exception handling upon detection of a specific problem
EHS objects are used to tie together trigger events (typically log events that match some configurable criteria) and a set of actions to perform (typically one or more CLI scripts).
EHS, along with CRON, makes use of the script-control functions for scripts. Any command available in the CLI can be executed in a script as the result of an event handler being triggered, except for commands that require interaction (for example, a y/n prompt for admin reboot without the now keyword, or commands that require a password). A script will error out if it encounters a command that requests input.
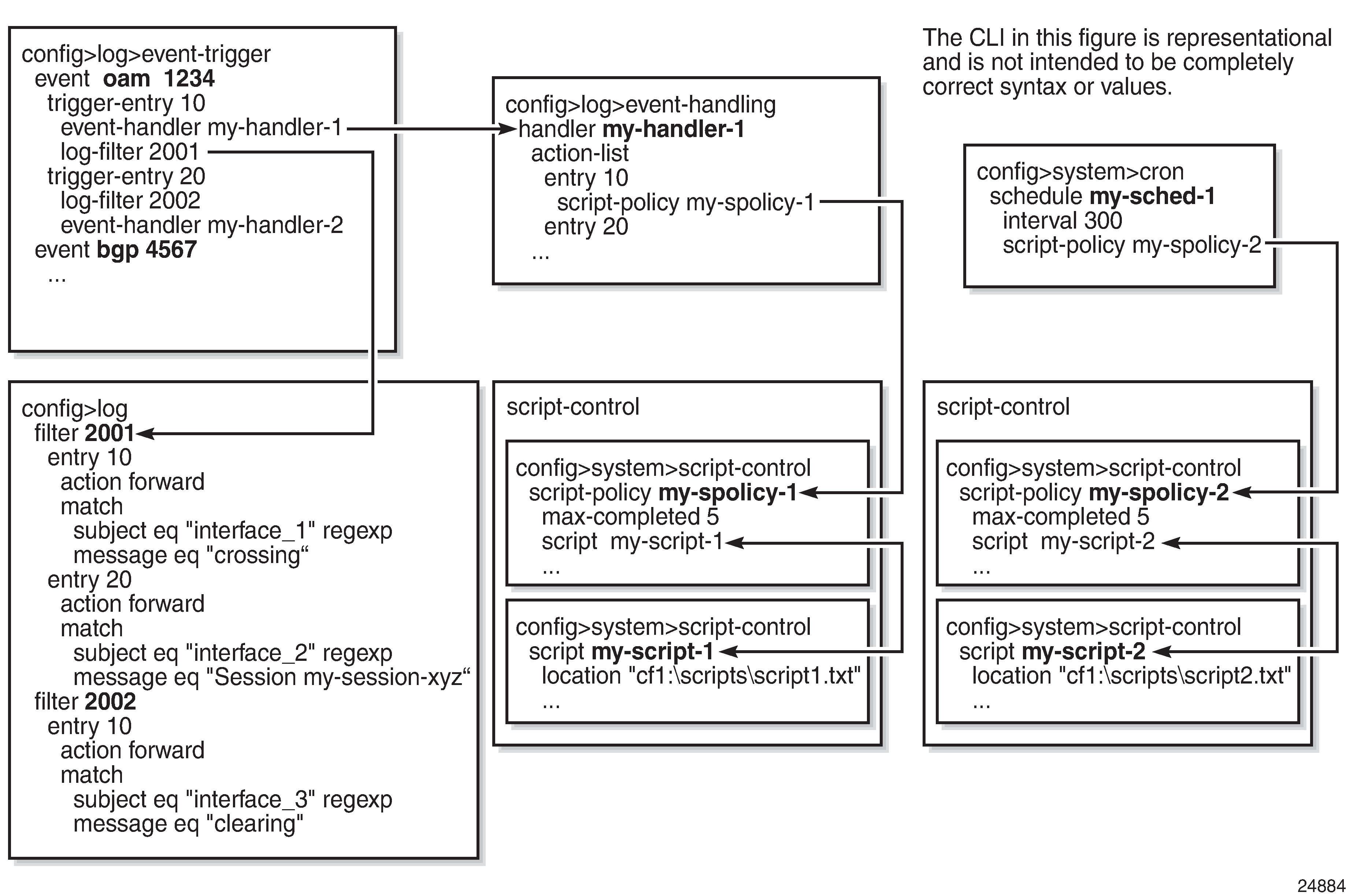
The following figure shows the relationships between the different configurable objects used by EHS (and CRON).
Configuring event handling
As shown in EHS object relationships, the steps involved in configuring EHS are:
configure a script and script policy under the config>system>script-control context; the script policy references the configured script
configure an event handler under the config>log>event-handling context and assign actions that reference the previously configured script policy
configure the event trigger under the config>log>event-trigger context that defines the event that triggers the running of the script
See the 7705 SAR Basic System Configuration Guide, "CLI Script Control" for information about configuring scripts and script policies.
Event handlers
Event handlers are created under the config>log>event-handling context. Each event handler is assigned an event handler name and an action list that consists of one or more entries. Each entry in the list references a configured script policy, which in turn references a configured script.
Event triggers
Event triggers are created under the config>log>event-trigger context. Each event trigger is associated with an application and event ID. One or more trigger entries can be configured for the event.
Each trigger entry references a previously configured event handler (which references a configured script policy, which in turn references the script that should be run). A trigger entry can be configured with a previously configured log filter. If a filter is configured, the event trigger calls the filter to determine whether the event should be dropped or forwarded. If the event is to be forwarded, the event trigger invokes the event handler.
All log filter matching options are supported. Regexp matching is supported. Complex rules can be configured to match on log events as a trigger for an EHS event handler.
The EHS triggers on log events that are dropped by user-configured log filters that are assigned to individual logs (with the config>log>log-id>filter command). The EHS event trigger occurs before the distribution of log event streams into individual logs.
If there is no filter configured for the trigger entry, the event trigger invokes the event handler as soon as the event occurs.
Log events can be configured to be suppressed or throttled (with the config>log>event-control command). EHS does not trigger on suppressed or throttled events.
Debounce
EHS debounce is the ability to trigger an action (for example, an EHS script), if an event happens (N) times within a specific time period (window) in seconds (S):
where:
N = 2 to 15 occurrences
S = 1 to 604800 seconds
For example, if linkDown occurs N times in S seconds, an EHS script is triggered to shut down the port.
Triggering happens with the Nth event, not at the end of the time window (S).
There is no sliding time window (for example, a trigger at the Nth event, N+1 event, and N+2 event) because N is reset after a trigger and the count is restarted.
When EHS debouncing is used, the varbinds passed in to an EHS script at script triggering time are from the Nth event occurrence (the Nth triggering event); see Variable passing.
If S is not specified, the 7705 SAR continues to trigger every Nth event.
Variable passing
The common parameters and variable bindings (varbinds) of a triggering log event are passed in to the triggered EHS script and can be used in the script as passed-in (dynamic) variables. These variables are:
the common event parameters: appid, name, eventid, severity, subject, and gentime
the predefined varbinds in a log event message; a varbind is a list of values or attributes included in a log event
Passed-in variables are read-only.
To view event parameters and varbinds, use the show log event-parameters command.
The passed-in event gentime is always UTC.
The event sequence number is not passed in to the script.
EHS scripting
An EHS script can contain local (static) variables and use some basic .if and .set commands. The use of variables with .if and .set commands in an EHS script adds more logic to EHS scripting and allows the reuse of a single EHS script for more than one trigger or action.
Both the passed-in and local variables can be used in the EHS script either as part of the CLI commands or as part of the .if or .set commands.
The following applies to both CLI commands and .if or .set commands:
Using $X (without using single or double quotes) replaces the variable X with its string or integer value.
-
Using ‟X” (with double quotes) means the literal string X.
-
Using ‟$X” (with double quotes) replaces the variable X with its string or integer value.
-
Using 'X' (with single quotes) means the literal string X.
-
Using ‛$X’ (with single quotes) does not replace the variable X with its value but means the literal string $X.
In summary:
All characters within single quotes are interpreted as string characters.
-
All characters within double quotes are interpreted as string characters except for $, which replaces the variable with its value (for example, shell expansion inside a string).
Some supported shell command scenarios are as follows (the commands are pseudo commands):
.if $string_variable==string_value_or_string_variable {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.if ($string_variable==string_value_or_string_variable) {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.if $integer_variable==integer_value_or_integer_variable {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.if ($integer_variable==integer_value_or_integer_variable) {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.if $string_variable!=string_value_or_string_variable {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.if ($string_variable!=string_value_or_string_variable) {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.if $integer_variable!=integer_value_or_integer_variable {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.if ($integer_variable!=integer_value_or_integer_variable) {
CLI_commands_set1
.} else {
CLI_commands_set2
.} endif
.set $string_variable = string_value_or_string_variable
.set ($string_variable = string_value_or_string_variable)
.set $integer_variable = integer_value_or_integer_variable
.set ($integer_variable = integer_value_or_integer_variable)
where:
CLI_commands_set1 is a set of one or more CLI commands
CLI_commands_set2 is a set of one or more CLI commands
string_variable is a local string variable
string_value_or_string_variable is a string value/variable
integer_variable is a local integer variable
integer_value_or_integer_variable is an integer value/variable
A maximum of 100 local variables per EHS script is imposed. Exceeding this limit may result in an error and only partial execution of the script.
When a set statement is used to set a string_variable to a string_value, the string_value can be any non-integer value with optional single or double quotes.
A "." preceding a directive (for example, if, and set) is always expected to start a new line.
An end of line is always expected after {.
A CLI command is always expected to start a new line.
Passed-in (dynamic) variables are always read-only inside an EHS script and cannot be overwritten using a set statement.
.if commands support == and != operators only.
.if and .set commands support addition, subtraction, multiplication, and division of integers.
.if and .set commands support concatenation of strings.
Valid examples:
configure service epipe $serviceID
where $serviceID is either a local integer variable or passed-in integer variable
echo srcAddr is $srcAddr
where $srcAddr is a passed-in string variable
.set $ipAddr = "10.0.0.1"
where $ipAddr is a local string variable
.set $ipAddr = $srcAddr
where $srcAddr is a passed-in string variable
$ipAddr is a local string variable
.set ($customerID = 50)
where $customerID is a local integer variable
.set ($totalPackets = $numIngrPackets + $numEgrPackets)
where $totalPackets, $numIngrPackets, $numEgrPackets are local integer variables
.set ($portDescription = $portName + $portLocation)
where $portDescription, $portName, $portLocation are local string variables
if ($srcAddr == "CONSOLE") {
CLI_commands_set1
.else {
CLI_commands_set2
.} endif
where $srcAddr is a passed-in string variable
CLI_commands_set1 is a set of one or more CLI commands
CLI_commands_set2 is a set of one or more CLI commands
.if ($customerId == 10) {
CLI_commands_set1
.else {
CLI_commands_set2
.} endif
where $customerID is a passed-in integer variable
CLI_commands_set1 is a set of one or more CLI commands
CLI_commands_set2 is a set of one or more CLI commands
.if ($numIngrPackets == $numEgrPackets) {
CLI_commands_set1
.else {
CLI_commands_set2
.} endif
where $numIngrPackets and $numEgrPackets are local integer variables
CLI_commands_set1 is a set of one or more CLI commands
CLI_commands_set2 is a set of one or more CLI commands
Invalid examples:
.set $srcAddr = "10.0.0.1"
where $srcAddr is a passed-in string variable
Reason: passed-in variables are read-only in an EHS script
.set ($ipAddr = ‛$numIngrPackets' + $numEgrPackets)
where $ipAddr is a local string variable
$numIngrPackets and $numEgrPackets are local integer variables
Reason: variable types do not match; cannot assign a string to an integer
.set ($numIngrPackets = $ipAddr + $numEgrPackets)
where $ipAddr is a local string variable
$numIngrPackets and $numEgrPackets are local integer variables
Reason: variable types do not match; cannot concatenate a string to an integer
.set $ipAddr = "10.0.0.1"100
where $ipAddr is a local string variable
Reason: when double quotes are used, they must enclose the entire string
.if ($totalPackets == "10.1.1.1") {
.} endif
where $totalPackets is a local integer variable
Reason: cannot compare an integer variable to a string value
.if ($ipAddr == 10) {
.} endif
where $ipAddr is a local string variable
Reason: cannot compare a string variable to an integer value
.if ($totalPackets == $ipAddr) {
where $totalPackets is a local integer variable
$ipAddr is a local string variable
Reason: cannot compare an integer variable to a string variable
Hardware support
EHS is supported on all 7705 SAR cards, modules, and fixed platforms.
Accounting logs
This section contains the following topics:
Before an accounting policy can be created, a target log file must be created to collect the accounting records. The files are stored in system memory on a compact flash (cf3: on all platforms; also cf1: or cf2: on the 7705 SAR-18) in a compressed (tar) XML format and can be retrieved using FTP or SCP.
Accounting records
An accounting policy must define a record name and collection interval. Only one record name can be configured per accounting policy. Also, a record name can only be used in one accounting policy.
The following table lists the record name, sub-record types, and default collection period for service and network accounting policies.
Record name |
Sub-record types |
Accounting object |
Default collection period (minutes) |
|---|---|---|---|
service-ingress-octets |
sio |
SAP |
5 |
service-egress-octets |
seo |
SAP |
5 |
service-ingress-packets |
sip |
SAP |
5 |
service-egress-packets |
sep |
SAP |
5 |
combined-service-ing-egr-octets |
cmSio and cmSeo |
SAP |
5 |
complete-service-ingress-egress |
cpSipo and cpSepo |
SAP |
5 |
saa |
saa (png) trc hop |
SAA or SAA test |
5 |
network-ingress-octets |
nio |
Network port |
15 |
network-egress-octets |
neo |
Network port |
15 |
network-ingress-packets |
nip |
Network port |
15 |
network-egress-packets |
nep |
Network port |
15 |
combined-network-ing-egr-octets |
cmNio and cmNeo |
Network port |
15 |
complete-network-ingr-egr |
cpNipo and cpNepo |
Network port |
15 |
combined-mpls-lsp-ingress combined-mpls-lsp-egress |
mplsLspIng mplsLspEg |
lsp |
5 |
combined-ldp-lsp-egress |
ldpEgr |
lsp |
5 |
The 7705 SAR supports simultaneous collection for some records. For example, ‟complete-network-ingr-egr” (cpNipo and cpNepo) simultaneously collects statistics on network-ingress octets, network-ingress packets, network-egress octets, and network-egress packets for the same network port.
Similarly, on the service side, ‟complete-service-ingr-egr” (cpSipo and cpSepo) simultaneously collects statistics on service-ingress octets, service-ingress packets, service-egress octets, and service-egress packets from a single SAP.
When creating accounting policies, one service accounting policy and one network accounting policy can be defined as the default. If statistics collection is enabled on a SAP or network port and no accounting policy is applied, the respective default policy is used. If no default policy is defined, no statistics are collected unless a specifically defined accounting policy is applied.
Each accounting record name is composed of one or more sub-records, which are in turn composed of multiple fields. The following table lists the accounting policy record names and the statistics that are collected with each.
Record name |
Sub-record |
Field |
Field description |
|---|---|---|---|
combined-mpls-lsp-ingress combined-mpls-lsp-egress combined-ldp-lsp-egress |
cmmplslspi cmmplslspe cmldplspe |
cmmplslspi |
combined mpls lsp ingress |
cmmplslspe |
combined mpls lsp egress |
||
cmldplspe |
combined ldp lsp egress |
||
iof |
InProfileOctetsForwarded |
||
oof |
OutOfProfileOctetsForwarded |
||
ipf |
In-profile packets forwarded |
||
opf |
Out-of-profile packets forwarded |
||
fc |
Packet forwarding class |
||
service-ingress-octets |
sio |
svc |
SvcId |
sap |
SapId |
||
qid |
QueueId |
||
hoo |
OfferedHiPrioOctets |
||
hod |
DroppedHiPrioOctets |
||
loo |
LowOctetsOffered |
||
lod |
LowOctetsDropped |
||
uco |
UncoloredOctetsOffered |
||
iof |
InProfileOctetsForwarded |
||
oof |
OutOfProfileOctetsForwarded |
||
service-egress-octets |
seo |
svc |
SvcId |
sap |
SapId |
||
qid |
QueueId |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
service-ingress-packets |
sip |
svc |
SvcId |
sap |
SapId |
||
qid |
QueueId |
||
hpo |
HighPktsOffered |
||
hpd |
HighPktsDropped |
||
lpo |
LowPktsOffered |
||
lpd |
LowPktsDropped |
||
ucp |
UncoloredPacketsOffered |
||
ipf |
InProfilePktsForwarded |
||
opf |
OutOfProfilePktsForwarded |
||
service-egress-packets |
sep |
svc |
SvcId |
sap |
SapId |
||
qid |
QueueId |
||
ipf |
InProfilePktsForwarded |
||
ipd |
InProfilePktsDropped |
||
opf |
OutOfProfilePktsForwarded |
||
opd |
OutOfProfilePktsDropped |
||
sap |
SapId |
||
slaProfile |
SlaProfile |
||
|
complete-service-ingress-egress (cpSipo and cpSepo) |
cpSipo |
svc |
SvcId |
sap |
SapId |
||
pid |
PolicerId |
||
hpo |
HighPktsOffered |
||
hpd |
HighPktsDropped |
||
lpo |
LowPktsOffered |
||
lpd |
LowPktsDropped |
||
ucp |
UncoloredPacketsOffered |
||
hoo |
OfferedHiPrioOctets |
||
hod |
DroppedHiPrioOctets |
||
loo |
LowOctetsOffered |
||
lod |
LowOctetsDropped |
||
uco |
UncoloredOctetsOffered |
||
apo |
AllPacketsOffered |
||
aoo |
AllOctetsOffered |
||
apd |
AllPacketsDropped |
||
aod |
AllOctetsDropped |
||
|
apf |
AllPacketsForwarded |
||
aof |
AllOctetsForwarded |
||
ipd |
InProfilePktsDropped |
||
iod |
InProfileOctetsDropped |
||
opd |
OutOfProfilePktsDropped |
||
ood |
OutOfProfileOctetsDropped |
||
hpf |
HighPriorityPacketsForwarded |
||
hof |
HighPriorityOctetsForwarded |
||
lpf |
LowPriorityPacketsForwarded |
||
lof |
LowPriorityOctetsForwarded |
||
ipf |
InProfilePktsForwarded |
||
opf |
OutOfProfilePktsForwarded |
||
iof |
InProfileOctetsForwarded |
||
oof |
OutOfProfileOctetsForwarded |
||
cpSepo |
svc |
SvcId |
|
sap |
SapId |
||
qid |
QueueId |
||
ipf |
InProfilePktsForwarded |
||
ipd |
InProfilePktsDropped |
||
opf |
OutOfProfilePktsForwarded |
||
opd |
OutOfProfilePktsDropped |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
combined-service-ingr-egr-octets (cmSio and CmSeo) |
cmSio |
svc |
SvcId |
sap |
SapId |
||
qid |
QueueId |
||
hoo |
OfferedHiPrioOctets |
||
hod |
DroppedHiPrioOctets |
||
loo |
LowOctetsOffered |
||
lod |
LowOctetsDropped |
||
uco |
UncoloredOctetsOffered |
||
iof |
InProfileOctetsForwarded |
||
oof |
OutOfProfileOctetsForwarded |
||
cmSeo |
svc |
SvcId |
|
sap |
SapId |
||
qid |
QueueId |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
network-ingress-octets |
nio |
port |
PortId |
qid |
QueueId |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
network-egress-octets |
neo |
port |
PortId |
qid |
QueueId |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
network-ingress-packets |
nip |
port |
PortId |
qid |
QueueId |
||
ipf |
InProfilePktsForwarded |
||
ipd |
InProfilePktsDropped |
||
opf |
OutOfProfilePktsForwarded |
||
opd |
OutOfProfilePktsDropped |
||
network-egress-packets |
nep |
port |
PortId |
qid |
QueueId |
||
ipf |
InProfilePktsForwarded |
||
ipd |
InProfilePktsDropped |
||
opf |
OutOfProfilePktsForwarded |
||
opd |
OutOfProfilePktsDropped |
||
|
combined-network-ing-egr-octets (cmNio and cmNeo) |
cmNio |
port |
PortId |
qid |
QueueId |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
|
cmNeo |
port |
PortId |
|
qid |
QueueId |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
complete-network-ingr-egr (cpNipo and cpNepo) |
cpNipo |
port |
PortId |
qid |
QueueId |
||
ipf |
InProfilePktsForwarded |
||
ipd |
InProfilePktsDropped |
||
opf |
OutOfProfilePktsForwarded |
||
opd |
OutOfProfilePktsDropped |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
cpNepo |
port |
PortId |
|
qid |
QueueId |
||
ipf |
InProfilePktsForwarded |
||
ipd |
InProfilePktsDropped |
||
opf |
OutOfProfilePktsForwarded |
||
opd |
OutOfProfilePktsDropped |
||
iof |
InProfileOctetsForwarded |
||
iod |
InProfileOctetsDropped |
||
oof |
OutOfProfileOctetsForwarded |
||
ood |
OutOfProfileOctetsDropped |
||
|
saa |
saa |
tmd |
TestMode |
own |
OwnerName |
||
tst |
TestName |
||
png |
PingRun subrecord |
||
rid |
RunIndex |
||
trr |
TestRunResult |
||
mnr |
MinRtt |
||
mxr |
MaxRtt |
||
avr |
AverageRtt |
||
rss |
RttSumOfSquares |
||
pbr |
ProbeResponses |
||
spb |
SentProbes |
||
mnt |
MinOutTt |
||
mxt |
MaxOutTt |
||
avt |
AverageOutTt |
||
tss |
OutTtSumOfSquares |
||
mni |
MinInTt |
||
mxi |
MaxInTt |
||
avi |
AverageInTt |
||
iss |
InTtSumOfSqrs |
||
ojt |
OutJitter |
||
ijt |
InJitter |
||
rjt |
RtJitter |
||
prt |
ProbeTimeouts |
||
prf |
ProbeFailures |
||
|
trc |
rid |
RunIndex |
|
trr |
TestRunResult |
||
lgp |
LastGoodProbe |
||
hop |
hop |
TraceHop |
|
hid |
HopIndex |
||
mnr |
MinRtt |
||
mxr |
MaxRtt |
||
avr |
AverageRtt |
||
rss |
RttSumOfSquares |
||
pbr |
ProbeResponses |
||
spb |
SentProbes |
||
mnt |
MinOutTt |
||
mxt |
MaxOutTt |
||
avt |
AverageOutTt |
||
tss |
OutTtSumOfSquares |
||
mni |
MinInTt |
||
mxi |
MaxInTt |
||
avi |
AverageInTt |
||
iss |
InTtSumOfSqrs |
||
ojt |
OutJitter |
||
ijt |
InJitter |
||
rjt |
RtJitter |
||
prt |
ProbeTimeouts |
||
prf |
ProbeFailures |
||
tat |
TraceAddressType |
||
tav |
TraceAddressValue |
Accounting files
When a policy has been created and applied to a service or network port, the accounting file is stored on the compact flash in a compressed XML file format. The 7705 SAR creates two directories on the compact flash to store the files. The following output displays a directory named act-collect that holds accounting files that are open and actively collecting statistics, and a directory named act that stores the files that have been closed and are awaiting retrieval.
ALU-1>file cf3:\# dir act*
12/19/2006 06:08a <DIR> act-collect
12/19/2006 06:08a <DIR> act
ALU-1>file cf3:\act-collect\ # dir
Directory of cf3:\act-collect#
12/23/2006 01:46a <DIR> .
12/23/2006 12:47a <DIR> ..
12/23/2006 01:46a 112 act1111-20031223-014658.xml.gz
12/23/2006 01:38a 197 act1212-20031223-013800.xml.gzAccounting files always have the prefix act followed by the accounting policy ID, log ID and timestamp. The accounting log file naming and log file destination properties (such as rollover and retention) are discussed in more detail in Log files.
A file ID can only be assigned to either one event log ID or one accounting log.
Design considerations
The 7705 SAR has ample resources to support large-scale accounting policy deployments. When preparing for an accounting policy deployment, verify that data collection, file rollover, and file retention intervals are properly tuned for the amount of statistics to be collected.
If the accounting policy collection interval is too brief, there may be insufficient time to store the data from all the services and network interfaces within the specified interval. If that is the case, some records may be lost or incomplete. Interval time, record types, and number of services using an accounting policy are all factors that should be considered when implementing accounting policies.
The rollover and retention intervals on the log files and the frequency of file retrieval must also be considered when designing accounting policy deployments. The amount of data stored depends on the type of record collected, the number of services that are collecting statistics, and the collection interval that is used.
Configuration notes
This following are logging configuration guidelines and restrictions:
-
A file or filter cannot be deleted if it has been applied to a log.
-
File IDs, syslog IDs, or SNMP trap groups must be configured in the config>log context before they can be applied to a log ID.
-
A file ID can only be assigned to either one log ID or one accounting policy.
-
Accounting policies must be configured in the config>log context before they can be applied to a service SAP or service interface, or applied to a network port.
-
A log ID associated with the snmp-trap-group command must be the same as a log ID associated with the log-id command.
Configuring logging with CLI
This section provides information to configure logging using the command line interface.
Topics in this section include:
Log configuration overview
Logging on the 7705 SAR is used to provide the operator with logging information for monitoring and troubleshooting. You can configure logging parameters to save information in a log file or direct the messages to other devices. Logging commands allow you to:
-
select the types of logging information to be recorded
-
assign a severity to the log messages
-
select the source and target of logging information
Log type
Logs can be configured in the following contexts:
-
log file – log files can contain log event message streams or accounting/billing information. Log file IDs are used to direct events, alarms/traps, and debug information to their respective targets.
-
SNMP trap groups – SNMP trap groups contain an IP address and community names that identify targets to send traps following specified events
-
syslog – information can be sent to a syslog host that is capable of receiving selected syslog messages from a network element
-
event control – configures a particular event, or all events associated with an application, to be generated or suppressed
-
event filters – an event filter defines whether to forward or drop an event or trap based on match criteria
-
accounting policies – an accounting policy defines the accounting records that will be created. Accounting policies can be applied to one or more service access points (SAPs) and to network ports.
-
event logs – an event log defines the types of events to be delivered to an associated destination
-
event throttling rate – defines the rate of throttling events
Basic event log configuration
The most basic log configuration must have the following:
-
a log ID or an accounting policy ID
-
a log source
-
a log destination
The following displays a log configuration example.
ALU-12>config>log# info
#------------------------------------------
echo "Log Configuration"
#------------------------------------------
file-id 1
description "This is a test file-id."
location cf3:
exit
file-id 2
description "This is a test log."
location cf3:
exit
snmp-trap-group 7
trap-target 10.10.10.10 "snmpv2c" notify-community "public"
exit
log-id 2
from main
to file 2
exit
----------------------------------------------
ALU-12>config>log#Common configuration tasks
The following sections describe basic system tasks that must be performed.
Configuring an event log
An event log file is identified by a log-id and contains information used to direct messages generated by system applications (such as events, alarms, traps, and debug information) to their respective destinations. One or more event sources can be specified using the from command. Event destinations (such as file IDs, SNMP trap groups, or syslog IDs) must be configured using the to command before they can be applied to an event log ID. Only one destination can be specified.
Use the file-id log-file-id command to specify the destination compact flash. See Configuring a file ID.
Use the following CLI syntax to configure a log file:
- CLI syntax:
config>log log-id log-id description description-string filter filter-id from {[main] [security] [change] [debug-trace]} to console to file log-file-id to memory [size] to session to snmp [size] to syslog syslog-id time-format {local | utc} no shutdown
The following displays an example of the event log file configuration command syntax:
- Example:
config# log config>log# log-id 2 config>log>log-id$ description "This is a test log file." config>log>log-id# filter 1 config>log>log-id# from main security config>log>log-id# to file 1 config>log>log-id# no shutdown config>log>log-id# exit
The following displays a log file configuration:
ALU-12>config>log>log-id# info
----------------------------------------------
...
log-id 2
description "This is a test log file."
filter 1
from main security
to file 1
exit
...
----------------------------------------------
ALU-12>config>log>log-id#Configuring a file ID
To create a log file, a file ID is defined that specifies the target compact flash drive and the rollover and retention interval period for the file. The rollover interval is defined in minutes and determines how long a file is used before it is closed and a new log file is created. The retention interval determines how long the file is stored on the compact flash drive before it is deleted.
The minimum amount of free space for log files on a compact flash drive is the lesser of 10% of the compact flash disk capacity or 5 Mb (5 242 880).
Use the following CLI syntax to configure a log file ID:
- CLI syntax:
config>log file-id log-file-id description description-string location cflash-id rollover minutes[retention hours]
The following displays an example of the log file ID configuration command syntax:
- Example:
config# log config>log# file-id 1 config>log>file-id# description "This is a log file." config>log>file-id# location cf3: config>log>file-id# rollover 600 retention 24
The following displays the file ID configuration:
ALU-12>config>log# info
------------------------------------------
file-id 1
description "This is a log file."
location cf3:
rollover 600 retention 24
exit
----------------------------------------------
ALU-12>config>log#Configuring an accounting policy
Before an accounting policy can be created, a target log file must be created to collect the accounting records. The files are stored in system memory on the compact flash drive in a compressed (tar) XML format and can be retrieved using FTP or SCP. See Configuring an event log and Configuring a file ID.
Accounting policies must be configured in the config>log context before they can be applied to a SAP or service interface, or applied to a network port. For information about associating an accounting policy with a SAP or a network port, see the 7705 SAR Services Guide or the 7705 SAR Interface Configuration Guide (respectively).
An accounting policy must define a record type and collection interval. Only one record type can be configured per accounting policy.
When creating accounting policies, one service accounting policy and one network accounting policy can be defined as default. If statistics collection is enabled on a SAP or network port and no accounting policy is applied, the respective default policy is used. If no default policy is defined, no statistics are collected unless a specifically defined accounting policy is applied.
Use the following CLI syntax to configure an accounting policy:
- CLI syntax:
config>log>accounting-policy acct-policy-id collection-interval minutes default description description-string record record-name to file log-file-id no shutdown
The following displays an example of the accounting policy configuration command syntax:
- Example:
config>log# accounting-policy 4 config>log>acct-policy# description "This is the default accounting policy." config>log>acct-policy# record service-ingress-packets config>log>acct-policy# default config>log>acct-policy# to file 1 config>log>acct-policy# exit config>log# accounting-policy 5 config>log>acct-policy# description "This is a test accounting policy." config>log>acct-policy# record service-ingress-packets config>log>acct-policy# to file 2 config>log>acct-policy#
The following displays the accounting policy configuration:
ALU-12>config>log# info
----------------------------------------------
accounting-policy 4
description "This is the default accounting policy."
record service-ingress-packets
default
to file 1
exit
accounting-policy 5
description "This is a test accounting policy."
record service-ingress-packets
to file 2
exit
----------------------------------------------
ALU-12>config>log#Configuring event control and throttle rate
Use the following CLI syntax to configure event control. The throttle parameter used in the event-control command syntax enables throttling for a specific event type. The config>log>throttle-rate command configures the number of events and interval length to be applied to all event types that have throttling enabled by this event-control command. The throttling rate can also be configured independently for each log event by using the specific-throttle-rate parameter; this rate overrides the globally configured throttle rate for the specified log event.
- CLI syntax:
config>log event-control application-id [event-name | event-number] generate [severity-level][throttle] [specific-throttle-rate events-limit interval seconds | disable-specific-throttle] event-control application-id [event-name |event-number] suppress throttle-rate events[interval seconds]
The following displays an example of throttle rate configuration for all events that have throttling enabled:
- Example:
config# log config>log# event-control aps 2003 generate major throttle config>log# event-control aps 2006 generate major throttle config>log# throttle-rate 500 interval 10
The following displays the throttle rate configuration:
ALU-12>config>log# info
#------------------------------------------
echo "Log Configuration"
#------------------------------------------
throttle-rate 500 interval 10
event-control "aps" 2003 generate major throttle
event-control "aps" 2006 generate major throttle
..
----------------------------------------------
ALU-12>config>log>#The following displays an example of throttle rate configuration for a specific event. The specific-throttle-rate configured for application aps, event 2003, overrides the globally configured throttle-rate.
- Example:
config# log config>log# event-control aps 2003 generate major throttle specific-throttle-rate 600 interval 15 config>log# event-control aps 2006 generate major throttle config>log# throttle-rate 500 interval 10
The following displays the specific throttle rate configuration:
ALU-12>config>log# info
#------------------------------------------
echo "Log Configuration"
#------------------------------------------
throttle-rate 500 interval 10
event-control "aps" 2003 generate major throttle specific-throttle-
rate 600 interval 15
event-control "aps" 2006 generate major throttle
..
----------------------------------------------
ALU-12>config>log>#Configuring a log filter
Use the following CLI syntax to configure a log filter:
- CLI syntax:
config>log filter filter-id default-action {drop | forward} description description-string entry entry-id action {drop | forward} description description-string match application {eq | neq} application-id message {eq | neq} pattern pattern [regexp] number {eq | neq | lt | lte | gt | gte} event-id router {eq | neq} router-instance [regexp] severity {eq | neq | lt | lte | gt | gte} severity-level subject {eq | neq} subject [regexp]
The following displays an example of the log filter configuration command syntax:
- Example:
config# log config>log# filter 1 config>log>filter# description "This is a test filter." config>log>filter# default-action drop config>log>filter# entry 1 config>log>filter>entry$ action forward config>log>filter>entry# match application eq atm config>log>filter>entry# match severity eq critical config>log>filter>entry# exit
The following displays the log filter configuration:
ALU-12>config>log# info
#------------------------------------------
echo "Log Configuration"
#------------------------------------------
file-id 1
description "This is our log file."
location cf3:
rollover 600 retention 24
exit
filter 1
default-action drop
description "This is a test filter."
entry 1
action forward
match
application eq "atm"
severity eq critical
exit
exit
exit
...
log-id 2
shutdown
description "This is a test log file."
filter 1
from main security
to file 1
exit
...
------------------------------------------
ALU-12>config>log#Configuring an SNMP trap group
The associated log-id does not have to be configured before a snmp-trap-group can be created; however, the snmp-trap-group must exist before the log-id can be configured to use it.
Use the following CLI syntax to configure an SNMP trap group:
- CLI syntax:
-
config>log snmp-trap-group log-id trap-target name address ip-address [port port] [snmpv1 | snmpv2c | snmpv3] notify-community communityName|snmpv3SecurityName[security-level {no-auth-no-privacy | auth-no-privacy | privacy}]
The following displays an example of the SNMP trap group configuration command syntax:
- Example:
-
config# log config>log# snmp-trap-group 2 config>log>snmp-trap-group# trap-target "target name" address 10.10.10.104 notify-community "communitystring" security-level no-auth-no-privacy config>log>snmp-trap-group# exit
The following displays the SNMP trap group configuration:
ALU-12>config>log# info
----------------------------------------------
...
snmp-trap-group 2
trap-target ‟target name” address 10.10.10.104:5 "snmpv3" notify-community
"communitystring"
exit
...
log-id 2
description "This is a test log file."
filter 1
from main security
to file 1
exit
...
----------------------------------------------
ALU-12>config>log#Configuring a syslog target
Log events cannot be sent to a syslog target host until a valid syslog ID exists.
Use the following CLI syntax to configure a syslog file:
- CLI syntax:
config>log syslog syslog-id address ip-address description description-string facility syslog-facility level {emergency | alert | critical | error | warning | notice | info | debug} log-prefix log-prefix-string port port
The following displays an example of the syslog file configuration command syntax:
- Example:
config# log config>log# syslog 1 config>log>syslog$ description "This is a syslog file." config>log>syslog# address 10.10.10.104 config>log>syslog# facility user config>log>syslog# level warning
The following displays the syslog configuration:
ALU-12>config>log# info
----------------------------------------------
...
syslog 1
description "This is a syslog file."
address 10.10.10.104
facility user
level warning
exit
...
----------------------------------------------
ALU-12>config>log#Log management tasks
This section discusses the following logging tasks:
Modifying a log file
If the log destination needs to be changed or if the size of an SNMP log or memory log needs to be modified, the log ID must be removed and then recreated.
Use the following CLI syntax to modify a log file:
- CLI syntax:
config>log log-id log-id description description-string filter filter-id from {[main] [security] [change] [debug-trace]} to console to file file-id to memory [size] to session to snmp [size] to syslog syslog-id
The following displays the current log configuration:
ALU-12>config>log>log-id# info
----------------------------------------------
...
log-id 2
description "This is a test log file."
filter 1
from main security
to file 1
exit
...
----------------------------------------------
ALU-12>config>log>log-id#The following displays an example of modifying log file parameters:
- Example:
config# log config>log# log-id 2 config>log>log-id# description "Chassis log file." config>log>log-id# filter 2 config>log>log-id# from security config>log>log-id# exit
The following displays the modified log file configuration:
ALU-12>config>log# info
----------------------------------------------
...
log-id 2
description "Chassis log file."
filter 2
from security
to file 1
exit
...
----------------------------------------------
ALU-12>config>log#Deleting a log file
The log ID must be shut down first before it can be deleted. In a previous example, file 1 is associated with log-id 2.
ALU-12>config>log# info
----------------------------------------------
file-id 1
description "LocationTest."
location cf3:
rollover 600 retention 24
exit
...
log-id 2
description "Chassis log file."
filter 2
from security
to file 1
exit
...
----------------------------------------------
ALU-12>config>log#Use the following CLI syntax to delete a log file:
- CLI syntax:
-
config>log no log-id log-id shutdown
The following displays an example of deleting a log file:
- Example:
-
config# log config>log# log-id 2 config>log>log-id# shutdown config>log>log-id# exit config>log# no log-id 2
Modifying a file ID
Use the following CLI syntax to modify a file ID:
- CLI syntax:
-
config>log file-id log-file-id description description-string location [cflash-id] rollover minutes[retention hours]
The following displays the current file ID configuration:
ALU-12>config>log# info
------------------------------------------
file-id 1
description "This is a log file."
location cf3:
rollover 600 retention 24
exit
----------------------------------------------
ALU-12>config>log#The following displays an example of modifying file ID parameters:
- Example:
-
config# log config>log# file-id 1 config>log>file-id# description "LocationTest." config>log>file-id# location cf3: config>log>file-id# rollover 2880 retention 500 config>log>file-id# exit
The following displays the file ID modifications:
ALU-12>config>log# info
----------------------------------------------
...
file-id 1
description "LocationTest."
location cf3:
rollover 2880 retention 500
exit
...
----------------------------------------------Deleting a file ID
Use the following CLI syntax to delete a file ID:
- CLI syntax:
config>log no file-id log-file-id
The following displays an example of deleting a file ID:
- Example:
config>log# no file-id 1
Modifying a syslog ID
Use the following CLI syntax to modify syslog ID parameters:
- CLI syntax:
config>log syslog syslog-id address ip-address description description-string facility syslog-facility level {emergency | alert | critical | error | warning | notice | info | debug} log-prefix log-prefix-string port port
The following displays an example of the syslog ID modifications:
- Example:
config# log config>log# syslog 1 config>log>syslog$ description "Test syslog." config>log>syslog# address 10.10.0.91 config>log>syslog# facility mail config>log>syslog# level info
The following displays the syslog configuration:
ALU-12>config>log# info
----------------------------------------------
...
syslog 1
description "Test syslog."
address 10.10.10.91
facility mail
level info
exit
...
----------------------------------------------
ALU-12>config>log#Deleting a syslog ID
Use the following CLI syntax to delete a syslog ID:
- CLI syntax:
config>log no syslog syslog-id
The following displays an example of deleting a syslog ID:
- Example:
config# log config>log# no syslog 1
Modifying an SNMP trap group
Use the following CLI syntax to modify an SNMP trap group:
- CLI syntax:
config>log snmp-trap-group log-id trap-target name [address ip-address] [port port] [snmpv1 | snmpv2c | snmpv3] notify-community communityName|snmpv3SecurityName[security-level {no-auth-no-privacy | auth-no-privacy | privacy}]
The following displays the current SNMP trap group configuration:
ALU-12>config>log# info
----------------------------------------------
...
snmp-trap-group 10
trap-target 10.10.10.104:5 "snmpv3" notify-community "communitystring"
exit
...
----------------------------------------------
ALU-12>config>log#The following displays an example of the command usage to modify an SNMP trap group:
- Example:
config# log config>log# snmp-trap-group 10 config>log>snmp-trap-group# no trap-target 10.10.10.104:5 config>log>snmp-trap-group# snmp-trap-group# trap- target 10.10.0.91:1 snmpv2c notify-community "com1"
The following displays the SNMP trap group configuration:
ALU-12>config>log# info
----------------------------------------------
...
snmp-trap-group 10
trap-target 10.10.0.91:1 "snmpv2c" notify-community "com1"
exit
...
----------------------------------------------
ALU-12>config>log#Deleting an SNMP trap group
Use the following CLI syntax to delete a trap target and SNMP trap group:
- CLI syntax:
config>log no snmp-trap-group log-id no trap-target name
The following displays the SNMP trap group configuration:
ALU-12>config>log# info
----------------------------------------------
...
snmp-trap-group 10
trap-target 10.10.0.91:1 "snmpv2c" notify-community "com1"
exit
...
----------------------------------------------
ALU-12>config>log#The following displays an example of deleting a trap target and an SNMP trap group.
- Example:
config>log# snmp-trap-group 10 config>log>snmp-trap-group# no trap-target 10.10.0.91:1 config>log>snmp-trap-group# exit config>log# no snmp-trap-group 10
Modifying a log filter
Use the following CLI syntax to modify a log filter:
- CLI syntax:
config>log filter filter-id default-action {drop | forward} description description-string entry entry-id action {drop | forward} description description-string match application {eq | neq} application-id message {eq | neq} pattern pattern [regexp] number{eq | neq | lt | lte | gt | gte}event-id router {eq | neq} router-instance [regexp] severity {eq | neq | lt | lte | gt | gte} severity-level subject {eq | neq} subject [regexp]
The following output displays the current log filter configuration:
ALU-12>config>log# info
#------------------------------------------
echo "Log Configuration"
#------------------------------------------
...
filter 1
default-action drop
description "This is a test filter."
entry 1
action forward
match
application eq "atm"
severity eq critical
exit
exit
exit
...
------------------------------------------
ALU-12>config>log#The following displays an example of the log filter modifications:
- Example:
config# log config>log# filter 1 config>log>filter# description "This allows <n>." config>log>filter# default-action forward config>log>filter# entry 1 config>log>filter>entry$ action drop config>log>filter>entry# match config>log>filter>entry>match# application eq user config>log>filter>entry>match# number eq 2001 config>log>filter>entry>match# no severity config>log>filter>entry>match# exit
The following displays the log filter configuration:
ALU-12>config>log>filter# info
----------------------------------------
...
description "This allows <n>."
entry 1
action drop
match
application eq "user"
number eq 2001
exit
exit
exit
...
----------------------------------------
ALU-12>config>log>filter#Deleting a log filter
Use the following CLI syntax to delete a log filter:
- CLI syntax:
config>log no filter filter-id
The following displays an example of the command to delete a log filter:
- Example:
config>log# no filter 1
Modifying event control parameters
Use the following CLI syntax to modify event control parameters:
- CLI syntax:
config>log event-control application-id [event-name | event-number] generate [severity-level][throttle] [specific-throttle-rate events-limit interval seconds | disable-specific-throttle] event-control application-id [event-name |event-number] suppress
The following displays the current event control configuration:
ALU-12>config>log# info
----------------------------------------------
...
event-control "atm" 2014 generate critical
...
----------------------------------------------
ALU-12>config>log#The following displays an example of event control modifications:
- Example:
config# log config>log# event-control atm 2014 suppress
The following displays the log filter configuration:
ALU-12>config>log# info
----------------------------------------------
...
event-control "atm" 2014 suppress
...
----------------------------------------------
ALU-12>config>log#Returning to the default event control configuration
The no form of the event-control command returns modified values back to the default values.
Use the following CLI syntax to return to the default event control configuration:
- CLI syntax:
config>log no event-control application [event-name |event-number]
The following displays an example of the command usage to return to the default values:
- Example:
config# log config>log# no event-control "atm" 2014 config>log# no event-control "filter" 2001 config>log# no event-control "mpls" 2001
ALU-12>config>log# info detail
----------------------------------------------
#------------------------------------------
echo "Log Configuration"
#------------------------------------------
...
event-control "atm" 2004 generate minor
event-control "atm" 2005 generate warning
event-control "atm" 2006 generate warning
event-control "atm" 2007 generate critical
event-control "atm" 2008 generate warning
event-control "atm" 2009 generate warning
event-control "atm" 2010 generate warning
event-control "atm" 2011 generate warning
event-control "atm" 2012 generate warning
event-control "atm" 2013 generate warning
event-control "atm" 2014 generate warning
event-control "atm" 2015 generate warning
event-control "atm" 2016 generate warning
event-control "atm" 2017 generate warning
...
----------------------------------------------
ALU-12>config>log#Log command reference
Command hierarchies
Configuration commands
Accounting policy commands
config
- log
- accounting-policy acct-policy-id
- no accounting-policy acct-policy-id
- collection-interval minutes
- no collection-interval
- [no] default
- description description-string
- no description
- record record-name
- no record
- [no] shutdown
- to file log-file-id
- to no-file
Event control commands
config
- log
- event-control application-id [event-name | event-number] generate [severity-level] [throttle] [specific-throttle-rate events-limit interval seconds | disable-specific-throttle]
- event-control application-id [event-name | event-number] suppress
- throttle-rate events [interval seconds]
- no throttle-rate
Event handling commands
config
- log
- event-handling
- [no] handler event-handler-name
- action-list
- [no] entry entry-id
- description description-string
- no description
- min-delay [delay]
- no min-delay
- script-policy policy-name [owner policy-owner]
- no script-policy
- [no] shutdown
- description description-string
- no description
- [no] shutdown
Event trigger commands
config
- log
- event-trigger
- [no] event application-id event-name-id
- description description-string
- no description
- [no] shutdown
- [no] trigger-entry entry-id
- debounce occurrences [within seconds]
- no debounce
- description description-string
- no description
- event-handler event-handler
- no event-handler
- log-filter filter-id
- no log-filter
- [no] shutdown
Log file commands
config
- log
- encryption-key key [hash | hash2]
- no encryption-key
- [no] file-id log-file-id
- description description-string
- no description
- location cflash-id
- rollover minutes [retention hours]
- no rollover
Log filter commands
config
- log
- [no] filter filter-id
- default-action {drop | forward}
- no default-action
- description description-string
- no description
- [no] entry entry-id
- action {drop | forward}
- no action
- description description-string
- no description
- [no] match
- application {eq | neq} application-id
- no application
- message {eq | neq} pattern pattern [regexp]
- no message
- number {eq | neq | lt | lte | gt | gte} event-id
- no number
- router {eq | neq} router-instance [regexp]
- no router
- severity {eq | neq | lt | lte | gt | gte} severity-level
- no severity
- subject {eq | neq} subject [regexp]
- no subject
Syslog commands
config
- log
- [no] syslog syslog-id
- address ip-address
- no address
- description description-string
- no description
- facility syslog-facility
- no facility
- level syslog-level
- no level
- log-prefix log-prefix-string
- no log-prefix
- port port
- no port
Logging destination commands
config
- log
- [no] log-id log-id
- description description-string
- no description
- filter filter-id
- no filter
- from {[main] [security] [change] [debug-trace]}
- no from
- [no] shutdown
- time-format {local | utc}
- to console
- to file log-file-id
- to memory [size]
- to session
- to snmp [size]
- to syslog syslog-id
SNMP trap group commands
config
- log
- [no] snmp-trap-group log-id
- description description-string
- no description
- trap-target name address ip-address [port port] [snmpv1 | snmpv2c | snmpv3] notify-community {communityName | snmpv3SecurityName}[security-level {no-auth-no-privacy | auth-no-privacy | privacy}]
- no trap-target name
Show commands
show
- log
- accounting-policy [acct-policy-id] [access | network] [associations]
- accounting-records
- applications
- event-control [application-id [event-name | event-number]]
- event-control application-id event-name detail
- event-handling
- handler [handler-name]
- handler detail
- information
- scripts
- event-parameters [application-id [event-name | event-number]]
- file-id [log-file-id]
- filter-id [filter-id]
- log-collector
- log-id [log-id] [severity severity-level] [application application] [sequence from-seq [to-seq]] [count count] [router router-instance [expression]] [subject subject [regexp]] [ascending | descending]
- snmp-trap-group [log-id]
- syslog [syslog-id]
Clear commands
clear
- log
- log-id log-id
- event-handling
- handler event-handler-name
- information
Command descriptions
Configuration commands
Generic commands
description
Syntax
description description-string
no description
Context
config>log>accounting-policy
config>log>event-handling>handler
config>log>event-handling>handler>action-list>entry
config>log>event-trigger>event
config>log>event-trigger>event>trigger-entry
config>log>file-id
config>log>snmp-trap-group
config>log>filter
config>log>filter>entry
config>log>log-id
config>log>syslog
Description
This command creates a text description stored in the configuration file for a configuration context.
The command associates a text string with a configuration context to help identify the content in the configuration file.
The no form of the command removes the string from the configuration.
Default
No text description is associated with this configuration.
Parameters
- string
The description can contain a string of up to 80 characters composed of printable, 7-bit ASCII characters. If the string contains special characters (such as #, $, or spaces), the entire string must be enclosed within double quotes.
shutdown
Syntax
[no] shutdown
Context
config>log>accounting-policy
config>log>event-handling>handler
config>log>event-handling>handler>action-list>entry
config>log>event-trigger>event
config>log>event-trigger>event>trigger-entry
config>log>log-id
Description
This command administratively disables an entity. When disabled, an entity does not change, reset, or remove any configuration settings or statistics.
The operational state of the entity is disabled as well as the operational state of any entities contained within. Many objects must be shut down before they can be deleted.
The no form of this command administratively enables an entity.
Default
no shutdown
Special cases
- log-id
when a log-id is shut down, no events are collected for the entity. This leads to the loss of event data.
- accounting-policy
when an accounting policy is shut down, no accounting data is written to the destination log ID. Counters in the billing data reflect totals, not increments, so when the policy is re-enabled (no shutdown), the counters include the data collected during the period the policy was shut down.
Accounting policy commands
accounting-policy
Syntax
accounting-policy acct-policy-id
no accounting-policy acct-policy-id
Context
config>log
Description
This command creates an access or network accounting policy. An accounting policy defines the accounting records that are created.
Access accounting policies are policies that can be applied to one or more service access points (SAPs). Changes made to an existing policy, using any of the sub-commands, are applied immediately to all SAPs where this policy is applied.
Network accounting policies are policies that can be applied to one or more network ports. Changes made to an existing policy, using any of the sub-commands, are applied immediately to all network ports where this policy is applied.
If an accounting policy is not specified on a SAP or network port, accounting records are produced in accordance with the access or network policy designated as the default. For more information, see the default command.
The no form of the command deletes the policy from the configuration. The accounting policy cannot be deleted unless it is removed from all the SAPs or network ports where the policy is applied. Use the show>log>accounting-policy command to see where an accounting policy is used and which accounting policy is the default policy.
Default
n/a
Parameters
- acct-policy-id
the policy ID that uniquely identifies the accounting policy, expressed as a decimal integer
collection-interval
Syntax
collection-interval minutes
no collection-interval
Context
config>log>accounting-policy
Description
This command configures the interval between collection of accounting records.
Parameters
- minutes
the interval, in minutes, at which accounting records are collected
default
Syntax
[no] default
Context
config>log>accounting-policy
Description
This command configures the accounting policy specified by acct-policy-id to be the default accounting policy that is used by all SAPs or network ports that do not have a specified accounting policy.
For a SAP or network port, if no accounting policy is explicitly specified and a default policy is defined, records are produced as per the default accounting policy. If no default policy is defined, no records are collected. However, if an accounting policy is explicitly defined for a SAP or network port, records are collected for that SAP or network port.
Only one access accounting policy ID can be designated as the default access policy. Similarly, only one network accounting policy ID can be designated as the default network accounting policy.
The record-name must be specified before configuring an accounting policy as default.
If a policy is configured as the default policy, a no default command must be issued before a new default policy can be configured.
Default accounting policies cannot be explicitly applied. For example, if default is set for accounting-policy 10, policy 10 cannot be assigned.
The no form of the command removes the default pol icy designation from the policy ID. The accounting policy is removed from all SAPs or network ports that do not have a policy explicitly defined. If there is no policy defined as the default policy, no accounting policy is applied to those entities.
record
Syntax
record record-name
no record
Context
config>log>accounting-policy
Description
This command adds the record name to the accounting policy, specifying which records to forward to the configured accounting file (identified by log-file-id). Each accounting policy can only contain one record name. To obtain a list of all record types that can be configured, use the show>log>accounting-records command.
ALU-12>config>log# show log accounting-records
==========================================================
Accounting Policy Records
==========================================================
Record # Record Name Def. Interval
----------------------------------------------------------
1 service-ingress-octets 5
2 service-egress-octets 5
3 service-ingress-packets 5
4 service-egress-packets 5
5 network-ingress-octets 15
6 network-egress-octets 15
7 network-ingress-packets 15
8 network-egress-packets 15
11 combined-network-ing-egr-octets 15
12 combined-service-ing-egr-octets 5
13 complete-service-ingress-egress 5
32 saa 5
54 complete-network-ing-egr 15
==========================================================
ALU-12>config>log#
The record-name must be specified before configuring an accounting policy as default.
To configure an accounting policy for access ports, select a service record (for example, service-ingress-octets). To change the service record to another service record, re-enter the record command with the new record-name to replace the old record-name.
When configuring an accounting policy for network ports, select a network record. To change the network record to another network record, re-enter the record command with the new record-name to replace the old record-name.
Only one record may be configured in a single accounting policy. If changing the record switches it from network to service, or from service to network, the old record-name must be removed using the no form of this command. For example, to change an accounting policy configuration from a network-egress-octets record to a service-ingress-octets record, use the no record command and then enter the service-ingress-octets record.
The no form of the command removes the record from the policy.
Default
n/a
Parameters
- record-name
the accounting record name
to
Syntax
to file log-file-id
to no-file
Context
config>log>accounting-policy
Description
This command specifies the destination for the accounting records selected for the accounting policy.
Default
No destination is specified
Parameters
- log-file-id
the log file ID specifies the destination for the accounting records associated with this accounting policy. The characteristics of the log file ID, such as rollover and retention intervals, must have already been defined in the config>log>file-id context. A log file ID can only be used once.
The file is generated when the log file ID is first referenced. This command identifies the type of accounting file to be created. If the to command is executed while the accounting policy is in operation, it becomes active during the next collection interval.
Event control commands
event-control
Syntax
event-control application-id [event-name | event-number] generate [severity-level] [throttle] [specific-throttle-rate events-limit interval seconds |disable-specific-throttle]
event-control application-id [event-name | event-number] suppress
no event-control application-id [event-name | event-number]
Context
config>log
Description
This command is used to specify that a particular event, or all events associated with an application, are either generated or suppressed.
Events are generated by an application and contain an event number and a description of the cause of the event. Each event has a default designation that directs it to be generated or suppressed.
Events are generated with a default severity level that can be modified by using the severity-level option. For example, to change event reporting for an external alarm output on the chassis, do the following:
- Specify the application by using the config>log>event-control>chassis command.
- Specify the event name or number by using the config>log>event-control>chassis> extAlarmInput1Detectedcommand.
- Specify whether the event is generated or suppressed by using the config>log>event-control>chassis> extAlarmInput1Detected>generate command.
- Change the severity level (for example, major severity) by using the config>log>event-control>chassis> extAlarmInput1Detected>generate>major command.
Events that are suppressed by default are typically used for debugging purposes. Events are suppressed at the time the application requests the event's generation. No event log entry is generated regardless of the destination. While this feature can save processor resources, there may be a negative effect on the ability to troubleshoot problems if the logging entries are not generated. However, the generation of too many events may cause excessive overhead.
The throttle parameter enables event throttling for these events. The throttling rate is set globally for all events with the throttle-rate command. The throttling rate can also be configured independently for each log event by using the specific-throttle-rate parameter; this rate overrides the globally configured throttle rate for the specified log event.
The no form of the command resets the parameters to the default setting for events for the application or a specific event within the application. The severity-level, generate, and suppress options will also be reset to the initial values.
Default
Each event has a default suppress or generate state. To display a list of all events and the current configuration use the event-control command.
Parameters
- application-id
the application whose events are affected by this event control filter
- event-name | event-number
to generate, suppress, or revert to default for a single event, enter the specific number or event short name. If no event number or name is specified, the command applies to all events in the application. To display a list of all event short names use the show>log>event-control command.
- generate
specifies that a log event is created when this event occurs. The generate keyword can be used with two optional parameters: severity-level and throttle.
- severity-level
An ASCII string representing the severity level to associate with the specified generated events
- throttle
specifies whether events of this type will be throttled
- suppress
indicates that the specified events will not be logged. If the suppress keyword is not specified, then the events are generated by default.
- specific-throttle-rate events-limit
configures an independent log event throttling rate for each log event, which overrides the globally configured throttle rate for the specified log event
- seconds
the number of seconds that the specific throttling interval lasts
- disable-specific-throttle
specifies to disable the specific-throttle-rate
throttle-rate
Syntax
throttle-rate events [intervalseconds]
no throttle-rate
Context
config>log
Description
This command configures an event throttling rate.
Parameters
- events
specifies the number of log events that can be logged within the specified interval for a specific event. When the limit has been reached, any additional events of that type will be dropped, and the event drop count will be incremented. At the end of the throttle interval, if any events have been dropped, a trap notification will be sent.
- seconds
specifies the number of seconds that an event throttling interval lasts
Event handling commands
event-handling
Syntax
event-handling
Context
config>log
Description
This command enables the context to configure event handling in the Event Handler System (EHS).
handler
Syntax
[no] handler event-handler-name
Context
config>log>event-handling
Description
This command configures an event handler.
The no form of the command removes the specified event handler.
Parameters
- event-handler-name
the name of the event handler, up to 32 characters in length
action-list
Syntax
action-list
Context
config>log>event-handling>handler
Description
This command enables the context to configure the event handler action list.
entry
Syntax
[no] entry entry-id
Context
config>log>event-handling>handler>action-list
Description
This command configures an event handler action-list entry. An action list consists of one or more entries. Each entry in the list references a configured script policy, which in turn references a configured script.
Multiple entries can be configured in the action list if multiple actions are required when an event triggers the event handler; for example, an event trigger results in the execution of different scripts. When the handler is triggered, it runs through the entries in sequence.
The no form of the command removes the specified action-list entry.
Parameters
- entry-id
the identifier of the event handler action-list entry
min-delay
Syntax
min-delay [delay]
no min-delay
Context
config>log>event-handling>handler>action-list>entry
Description
This command specifies the minimum delay between subsequent executions of the action specified in this entry. This is useful, for example, to ensure that a script does not get triggered to execute too often.
Default
no min-delay
Parameters
- delay
the delay time, in seconds
script-policy
Syntax
script-policy policy-name [owner policy-owner]
no script-policy
Context
config>log>event-handling>handler>action-list>entry
Description
This command specifies the script policy to use for this event handler action-list entry. The associated script is launched when the handler is triggered.
The script policy must already have been configured under the config>system>script-control context.
Default
no script-policy
Parameters
- policy-name
the script policy name
- policy-owner
the script policy owner associated with the script policy name
Event trigger commands
event-trigger
Syntax
event-trigger
Context
config>log
Description
This command enables the context to configure log events as triggers for event handlers in the EHS.
event
Syntax
[no] event application-id event-name-id
Context
config>log>event-trigger
Description
This command defines a specific log event that triggers the associated event handler. Further matching criteria can be applied (with the log-filter command) to only trigger certain handlers with certain instances of the log event.
The log event consists of an application ID and event ID.
The no form of the command removes the specified log event.
Parameters
- application-id
the type of application that triggers the event
- event-name-id
the numerical identifier or name of the event
trigger-entry
Syntax
[no] trigger-entry entry-id
Context
config>log>event-trigger>event
Description
This command configures a trigger entry for the specified log event. A trigger entry references a previously configured event handler. One or more trigger entries can be configured for the event.
Trigger entries can also be configured with a previously configured log filter.
The no form of the command removes the specified trigger entry.
Parameters
- entry-id
the identifier of the event trigger entry
debounce
Syntax
debounce occurrences [within seconds]
no debounce
Context
config>log>event-trigger>event>trigger-entry
Description
This command configures how many times the specified log event occurs before an action is triggered (for example, an EHS script). The number of occurrences of the event can be optionally bounded by a time window. If no time window is specified, the action is triggered every specified Nth event.
Triggering occurs at the specified Nth event, not at the end of the time window.
Default
no debounce
Parameters
- occurrences
the number of times the event must occur in order for EHS to trigger an action
- seconds
the time window, in seconds, in which the specified number of occurrences must happen in order for EHS to trigger an action
event-handler
Syntax
event-handler event-handler
no event-handler
Context
config>log>event-trigger>event>trigger-entry
Description
This command specifies the event handler to be used for this trigger entry. The event handler must have already been configured under the config>log>event-handling>handler context.
If the log event occurs and matches the criteria configured in the log filter (see log-filter), the event handler is triggered. When the event handler is triggered, the script that is referenced by the script policy that is in turn referenced by the event handler, is executed.
Parameters
- event-handler
the name of the event handler
log-filter
Syntax
log-filter filter-id
no log-filter
Context
config>log>event-trigger>event>trigger-entry
Description
This command specifies the log filter to be used for this trigger entry. The log filter must have already been configured under the config>log>filter context.
The log filter defines the matching criteria that must be met in order for the log event to trigger the event handler. The log filter is applied to the log event, and if the filtering decision results in a forward action, the event handler is triggered.
Parameters
- filter-id
the log filter identifier
Log file commands
encryption-key
Syntax
encryption-key key [hash | hash2]
no encryption-key
Context
config>log
Description
This command specifies the encryption key used by AES-265-CTR for log file encryption. The encryption key is used for all local log files on the system.
The no form of this command deletes the encryption key.
Parameters
- key
-
specifies the encryption key
If the hash or hash2 parameter is not configured, the key is entered in plaintext and the key length must be between 8 and 32 characters. A plaintext key cannot contain embedded nulls or end with "hash" or "hash2".
If the hash or hash2 parameter is configured, the key is hashed and the key length must be between 1 and 64 characters.
- hash
-
specifies that the key is entered and stored on the node in encrypted form
- hash2
-
specifies that the key is entered and stored on the node in a more complex encrypted form. The hash2 encryption scheme is node-specific and the key cannot be transferred between nodes.
file-id
Syntax
[no] file-id log-file-id
Context
config>log
Description
This command enables the context to configure a file ID template that is used as a destination for an event log or an accounting (billing) file.
The template defines the file location and characteristics of the destination for a log event message stream or for accounting and billing information. The log-file-id variable defined in this context is subsequently specified in the to command under config>log>log-id or config>log>accounting-policy contexts, to direct specific logging or accounting source streams to the file destination.
A file ID can only be assigned to either one log-id or one accounting-policy. It cannot be reused for multiple instances. A file ID and associated file definition must exist for each log and accounting file that will be stored in the file system.
A file is created when the file ID defined by this command is selected as the destination type for a specific log or accounting record. Log files are collected in a "log" directory. Accounting files are collected in an "act" directory.
The filenames for a log or accounting file are created by the system (see the following table).
File type |
Filename |
|---|---|
Log file |
logllff-timestamp |
Accounting file |
actaaff-timestamp |
where:
ll is the log-id
aa is the accounting policy-id
ff is the file-id
timestamp is the actual timestamp when the file is created. The format for the timestamp is yyyymmdd-hhmmss, where:
yyyy is the year (for example, 2016)
mm is the month number (for example, 12 for December)
dd is the day of the month (for example, 03 for the 3rd of the month)
hh is the hour of the day in 24-hour format (for example, 04 for 4 a.m.)
mm is the minutes (for example, 30 for 30 minutes past the hour)
ss is the number of seconds (for example, 14 for 14 seconds)
The accounting file is compressed and has a .gz extension.
When initialized, each file contains:
the log-id description
the time the file was opened
the reason the file was created
the sequence number of the last event stored on the log (if the event log file was closed properly)
If the process of writing to a log file fails (for example, the compact flash card is full), the log file will not become operational even if the compact flash card is replaced. Enter a clear log command or a shutdown/no shutdown command sequence to reinitialize the file.
If the location fails (for example, the compact flash card fills up during the write process), a trap is sent.
The no form of the command removes the file ID from the configuration. A file ID can only be removed from the configuration if the file is not the designated output for a log destination. The actual file remains on the file system.
Default
n/a
Parameters
- log-file-id
the file identification number for the file, expressed as a decimal integer
location
Syntax
location cflash-id
no location
Context
config>log>file-id
Description
This command specifies the location where the log or accounting billing file will be created.
The location command is optional. If the location command is not explicitly configured, log and accounting files will be created on cf3: for the following:
7705 SAR-8 Shelf V2
7705 SAR-A
7705 SAR-Ax
7705 SAR-H
7705 SAR-Hc
7705 SAR-M
7705 SAR-Wx
7705 SAR-X
For the 7705 SAR-18, log files are created by default on cf1: and accounting files are created by default on cf2:. There are no overflows onto other devices.
When multiple location commands are entered in a single file ID context, the last command overwrites the previous command.
When the location of a file ID that is associated with an active log ID is changed, the log events are not immediately written to the new location. The new location does not take effect until the log rolls over, either because the rollover period has expired or a clear>log log-id command is entered to manually roll over the log file.
When creating log or accounting files, the designated location is used as long as there is available space. If no space is available, an attempt is made to delete unnecessary files that are past their retention date.
If sufficient space is not available, an attempt is made to remove the oldest to newest closed log or accounting files. After each file is deleted, the system attempts to create the new file.
A medium severity trap is issued to indicate that the compact flash is either not available or that no space is available on the specified flash.
A high-priority alarm condition is raised if the compact flash device for this file ID is not present or if there is insufficient space available. If space does becomes available, the alarm condition will be cleared.
Use the no form of this command to revert to default settings.
Default
For the 7705 SAR-8 Shelf V2, 7705 SAR-A, 7705 SAR-Ax, 7705 SAR-H, 7705 SAR-Hc, 7705 SAR-M, 7705 SAR-Wx, and 7705 SAR-X, log and accounting files are created on cf3:
For the 7705 SAR-18, log files are created on cf1: and accounting files are created on cf2:
Parameters
- cflash-id
specifies the location of the flash
rollover
Syntax
rollover minutes [retention hours]
no rollover
Context
config>log>file-id
Description
This command configures how often an event or accounting log is rolled over or partitioned into a new file.
An event or accounting log is actually composed of multiple individual files. The system creates a new file for the log based on the rollover time, expressed in minutes.
The retention option, expressed in hours, allows you to modify the default time that the file is kept in the system. The retention time is based on the rollover time of the file. The retention time is used as a factor to determine which files should be deleted first as the file space becomes full.
When multiple rollover commands for a file ID are entered, the last command overwrites the previous command.
Default
rollover 1440
retention 12
Parameters
- minutes
the rollover time, in minutes
- hours
the retention period, in hours, expressed as a decimal integer. The retention period is based on the creation time of the file. The file becomes a candidate for removal when the creation timestamp + rollover time + retention time is less than the current timestamp.
Log filter commands
filter
Syntax
[no] filter filter-id
Context
config>log
Description
This command creates a context for an event filter. An event filter specifies whether to forward or drop an event or trap based on the match criteria.
Filters are configured in the filter filter-id context and then applied to a log in the log-id log-id context. Only events for the configured log source streams destined for the log ID where the filter is applied are filtered.
Any changes made to an existing filter, using any of the sub-commands, are immediately applied to the destinations where the filter is applied.
The no form of the command removes the filter association from log IDs, which causes those logs to forward all events.
Default
No event filters are defined.
Parameters
- filter-id
uniquely identifies the filter
default-action
Syntax
default-action {drop | forward}
no default-action
Context
config>log>filter
Description
The default action specifies the action that is applied to events when no action is specified in the event filter entries or when an event does not match the specified criteria.
When multiple default-action commands are entered, the last command overwrites the previous command.
The no form of the command reverts to the default value.
Default
default-action forward
Parameters
- drop
the events that are not explicitly forwarded by an event filter match are dropped
- forward
the events that are not explicitly dropped by an event filter match are forwarded
entry
Syntax
[no] entry entry-id
Context
config>log>filter
Description
This command is used to create or edit an event filter entry. Multiple entries may be created using unique entry-id numbers. The -TiMOS implementation exits the filter on the first match found and executes the action in accordance with the action command.
Comparisons are performed in an ascending entry ID order. When entries are created, they should be arranged sequentially from the most explicit entry to the least explicit. Matching ceases when a packet matches an entry. The entry action is performed on the packet, either drop or forward. To be considered a match, the packet must meet all the conditions defined in the entry.
An entry may have no match criteria defined (in which case, everything matches) but must have at least the action keyword for it to be considered complete. Entries without the action keyword will be considered incomplete and rendered inactive.
The no form of the command removes the specified entry from the event filter. Entries removed from the event filter are immediately removed from all log IDs where the filter is applied.
Default
No event filter entries are defined. An entry must be explicitly configured.
Parameters
- entry-id
uniquely identifies a set of match criteria corresponding action within a filter. Entry ID values should be configured in staggered increments so you can insert a new entry in an existing policy without renumbering the existing entries.
action
Syntax
action {drop | forward}
no action
Context
config>log>filter>entry
Description
This command specifies a drop or forward action associated with the filter entry.
If neither drop nor forward is specified, the default-action will be used for traffic that conforms to the match criteria. This could be considered a No-Op filter entry used to explicitly exit a set of filter entries without modifying previous actions.
When multiple action commands are entered, the last command will overwrite the previous command.
The no form of the command removes the specified action statement.
Default
no action
Parameters
- drop
specifies that packets matching the entry criteria will be dropped
- forward
specifies that packets matching the entry criteria will be forwarded
match
Syntax
[no] match
Context
config>log>filter>entry
Description
This command enables the context to enter or edit match criteria for a filter entry. When the match criteria is satisfied, the action associated with the entry is executed.
If more than one match parameter (within one match statement) is specified, then all the criteria must be satisfied and functional before the action associated with the match is executed.
Use the applications command to display a list of the valid applications.
Match context can consist of multiple match parameters (application, event-number, severity, subject), but multiple match statements cannot be entered per entry.
The no form of the command removes the match criteria for the entry-id.
Default
No match context is defined.
application
Syntax
application {eq | neq} application-id
no application
Context
config>log>filter>entry>match
Description
This command adds a TiMOS application as an event filter match criterion.
A TiMOS application is the software entity that reports the event. Examples of applications include: IP, MPLS, CLI, and SERVICES. Only one application can be specified per entry.
When multiple application commands are entered, the last command will overwrite the previous command.
The no form of the command removes the application as a match criterion.
Default
no application
Parameters
- eq
specifies that the matching criteria should be equal to the specified value
- neq
specifies that the matching criteria should not be equal to the specified value
- application-id
the application name string
message
Syntax
message {eq | neq}pattern pattern [regexp]
no message
Context
config>log>filter>entry>match
Description
This command adds system messages as a match criterion.
The no form of the command removes system messages as a match criterion.
Parameters
- eq
specifies that the matching criteria should be equal to the specified value
- neq
specifies that the matching criteria should not be equal to the specified value
- pattern
specifies a message up to 400 characters in length to be used in the match criteria
- regexp
specifies the type of string comparison to use to determine if the log event matches the value of message command parameters. When the regexp keyword is specified, the string in the message command is a regular expression string that will be matched against the message string in the log event being filtered. When the regexp keyword is not specified, the default matching algorithm used is a basic substring match.
number
Syntax
number {eq | neq | lt | lte | gt | gte} event-id
no number
Context
config>log>filter>entry>match
Description
This command adds a TiMOS application event number as a match criterion.
TiMOS event numbers uniquely identify a specific logging event within an application.
Only one number command can be entered per event filter entry. If multiple number commands are entered, the last command overwrites the previous command.
The no form of the command removes the event number as a match criterion.
Default
no event-number
Parameters
- eq | neq | lt | lte | gt | gte
this operator specifies the type of match. Valid operators are listed in the following table.
Table 8. Valid match operators for event numbers Operator
Notes
eq
Equal to
neq
Not equal to
lt
Less than
lte
Less than or equal to
gt
Greater than
gte
Greater than or equal to
- event-id
the event ID, expressed as a decimal integer
router
Syntax
router {eq | neq} router-instance [regexp]
no router
Context
config>log>filter>entry>match
Description
This command specifies the log event matches for the router.
Parameters
- eq
specifies that the matching criteria should be equal to the specified value
- neq
specifies that the matching criteria should not be equal to the specified value
- router-instance
specifies a router name up to 32 characters to be used in the match criteria
- regexp
specifies the type of string comparison to use to determine if the log event matches the value of router command parameters. When the regexp keyword is specified, the string in the router command is a regular expression string that will be matched against the router string in the log event being filtered. When the regexp keyword is not specified, the router command string is matched exactly by the event filter.
severity
Syntax
severity {eq | neq | lt | lte | gt | gte} severity-level
no severity
Context
config>log>filter>entry>match
Description
This command adds an event severity level as a match criterion. Only one severity command can be entered per event filter entry. When multiple severity commands are entered, the last command overwrites the previous command.
The no form of the command removes the severity match criterion.
Default
no severity
Parameters
- eq | neq | lt | lte | gt | gte
this operator specifies the type of match. Valid operators are listed in the following table.
Table 9. Valid operators for event severity Operator
Notes
eq
Equal to
neq
Not equal to
lt
Less than
lte
Less than or equal to
gt
Greater than
gte
Greater than or equal to
- severity-level
the ITU severity level number. The following table lists severity levels and corresponding numbers per ITU standards M.3100 X.733 & X.21 severity levels.
Table 10. Severity levels Severity number
Severity level
1
Cleared
2
Indeterminate (info)
3
Critical
4
Major
5
Minor
6
Warning
subject
Syntax
subject {eq | neq} subject [regexp]
no subject
Context
config>log>filter>entry>match
Description
This command adds an event subject as a match criterion.
The subject is the entity for which the event is reported, such as a port. In this case, the port-id string would be the subject.
Only one subject command can be entered per event filter entry. If multiple subject commands are entered, the last command overwrites the previous command.
The no form of the command removes the subject match criterion.
Default
no subject
Parameters
- eq
specifies that the matching criteria should be equal to the specified value
- neq
specifies that the matching criteria should not be equal to the specified value
- subject
a string used as the subject match criterion
- regexp
specifies the type of string comparison to use to determine if the log event matches the value of subject command parameters. When the regexp keyword is specified, the string in the subject command is a regular expression string that will be matched against the subject string in the log event being filtered.
When the regexp keyword is not specified, the subject command string is matched exactly by the event filter.
Syslog commands
syslog
Syntax
[no] syslog syslog-id
Context
config>log
Description
This command enables the context to configure a syslog target host that is capable of receiving selected syslog messages from the 7705 SAR.
A valid syslog-id must have the target syslog host address configured.
A maximum of 10 syslog IDs can be configured.
No log events are sent to a syslog target address until the syslog-id has been configured as the log destination (to) in the log-id node.
Default
No syslog IDs are defined.
Parameters
- syslog-id
the syslog ID number for the syslog destination, expressed as a decimal integer
address
Syntax
address ip-address
no address
Context
config>log>syslog
Description
This command associates the syslog target host IP address with the syslog ID.
This parameter is mandatory. If no address is configured, syslog data cannot be forwarded to the syslog target host.
Only one address can be associated with a syslog-id. If multiple addresses are entered, the last address entered overwrites the previous address.
The same syslog target host can be used by multiple log IDs.
The no form of the command removes the syslog target host IP address.
Default
no address
Parameters
- ip-address
the IP address of the syslog target host
facility
Syntax
facility syslog-facility
no facility
Context
config>log>syslog
Description
This command configures the facility code for messages sent to the syslog target host.
Multiple syslog IDs can be created with the same target host but each syslog ID can only have one facility code. If multiple facility codes are entered, the last facility code entered overwrites the previous facility code.
If multiple facilities need to be generated for a single syslog target host, then multiple log-id entries must be created, each with its own filter criteria to select the events to be sent to the syslog target host with a given facility code.
The no form of the command reverts to the default value.
Default
local7
Parameters
- syslog-facility
the syslog facility name for the event type being sent to the syslog target host. Valid codes are as per RFC 3164, The BSD syslog Protocol.
level
Syntax
level syslog-level
no level
Context
config>log>syslog
Description
This command configures the syslog message severity level threshold. All messages with a severity level equal to or higher than the threshold are sent to the syslog target host.
Only a single threshold level can be specified. If multiple level commands are entered, the last command will overwrite the previous command.
The no form of the command reverts to the default value.
Default
info
Parameters
- syslog-level
the threshold severity level value, as described in the following table. See Event severity levels for the numeric values associated with the severity levels.
log-prefix
Syntax
log-prefix log-prefix-string
no log-prefix
Context
config>log>syslog
Description
This command adds the string prepended to every syslog message sent to the syslog host.
RFC 3164, The BSD syslog Protocol, allows an alphanumeric string (tag) to be prepended to the content of every log message sent to the syslog host. This alphanumeric string can, for example, be used to identify the node that generates the log entry. The software appends a colon (:) and a space to the string and it is inserted in the syslog message after the date stamp and before the syslog message content.
Only one string can be entered. If multiple strings are entered, the last string overwrites the previous string. The alphanumeric string can contain lowercase (a-z), uppercase (A-Z) and numeric (0-9) characters.
The no form of the command removes the log prefix string.
Default
no log-prefix
Parameters
- log-prefix-string
an alphanumeric string of up to 32 characters. Spaces and colons (:) cannot be used in the string.
port
Syntax
port value
no port
Context
config>log>syslog
Description
This command configures the UDP port that will be used to send syslog messages to the syslog target host.
The port configuration is needed if the syslog target host uses a port other than the standard UDP syslog port 514.
Only one port can be configured. If multiple port commands are entered, the last entered port overwrites the previously entered ports.
The no form of the command reverts to the default value.
Default
no port
Parameters
- value
the configured UDP port number used when sending syslog messages
Logging destination commands
log-id
Syntax
[no] log-id log-id
Context
config>log
Description
This command creates a context to configure destinations for event streams.
The log-id context is used to direct events, alarms, traps, and debug information to respective destinations.
A maximum of 100 logs can be configured.
Before an event can be associated with this log-id, the log-id>from command identifying the source of the event must be configured.
Only one destination can be specified for a log-id. The destination of an event stream can be an in-memory buffer, console, session, snmp-trap-group, syslog, or file.
Use the event-control command to suppress the generation of events, alarms, and traps for all log destinations.
An event filter policy can be applied in the log-id context to limit which events, alarms, and traps are sent to the specified log-id.
Log-IDs 99 and 100 are created by the agent. Log-ID 99 captures all log messages. Log-ID 100 captures log messages with a severity level of major and above.
The no form of the command deletes the log destination ID from the configuration.
Default
No log destinations are defined
Parameters
- log-id
the log ID number, expressed as a decimal integer
filter
Syntax
filter filter-id
no filter
Context
config>log>log-id
Description
This command associates an event filter policy with the log destination.
The filter command is optional. If no event filter is configured, all events, alarms and traps generated by the source stream will be forwarded to the destination.
An event filter policy defines (limits) the events that are forwarded to the destination configured in the log-id. The event filter policy can also be used to select the alarms and traps to be forwarded to a destination snmp-trap-group.
The application of filters for debug messages is limited to application and subject only.
Accounting records cannot be filtered using the filter command.
Only one filter-id can be configured per log destination.
The no form of the command removes the specified event filter from the log-id.
Default
no filter
Parameters
- filter-id
the event filter policy ID that is used to associate the filter with the log-id configuration. The event filter policy ID must already be defined in the config>log>filter filter-id context. Log ID 100 is preconfigured by the system as a Severe Event Log that is associated with filter policy 1001 by default.
from
Syntax
from {[main] [security] [change] [debug-trace]}
no from
Context
config>log>log-id
Description
This command selects the source stream to be sent to a log destination.
One or more source streams must be specified. The source of the data stream must be identified using the from command before you can configure the destination using the to command. The from command can identify multiple source streams in a single statement (for example: from main change debug-trace).
Only one from command may be entered for a single log-id. If multiple from commands are entered, then the last command entered overwrites the previous command.
The no form of the command removes all previously configured source streams.
Default
no from
Parameters
- main
instructs all events in the main event stream to be sent to the destination defined in the to command for this destination log-id. The main event stream contains the events that are not explicitly directed to any other event stream. To limit the events forwarded to the destination, configure filters using the filter (log destination) command.
- security
instructs all events in the security event stream to be sent to the destination defined in the to command for this destination log-id. The security stream contains all events that affect attempts to breach system security such as failed login attempts, attempts to access MIB tables to which the user is not granted access, or attempts to enter a branch of the CLI to which access has not been granted. To limit the events forwarded to the destination, configure filters using the filter (log destination) command.
- change
instructs all events in the user activity stream to be sent to the destination configured in the to command for this destination log-id. The change event stream contains all events that directly affect the configuration or operation of this node. To limit the events forwarded to the change stream destination, configure filters using the filter (log destination) command.
- debug-trace
instructs all debug-trace messages in the debug stream to be sent to the destination configured in the to command for this destination log-id. Filters applied to debug messages are limited to application and subject.
to console
Syntax
to console
Context
config>log>log-id
Description
This command instructs the events selected for the log ID to be directed to the console. If the console is not connected, all entries are dropped.
The command is one of the to commands used to specify the log ID destination. A to command is mandatory when configuring a log destination.
The source of the data stream must be specified in the from command before configuring the destination with the to command.
The to command can only be set once. It cannot be modified or re-entered. If the log destination needs to be changed or if the maximum size of an SNMP log or memory log needs to be modified, the log ID must be removed and then recreated.
Default
No destination is specified
to file
Syntax
to file log-file-id
Context
config>log>log-id
Description
This command instructs the events selected for the log ID to be directed to a specified file.
The command is one of the to commands used to specify the log ID destination. A to command is mandatory when configuring a log destination.
The source of the data stream must be specified in the from command before configuring the destination with the to command.
The to command can only be set once. It cannot be modified or re-entered. If the log destination needs to be changed or if the maximum size of an SNMP log or memory log needs to be modified, the log ID must be removed and then recreated.
Default
No destination is specified
Parameters
- log-file-id
instructs the events selected for the log ID to be directed to the log-file-id. The characteristics of the log-file-id referenced here must have already been defined in the config>log>file-id log-file-id context.
to memory
Syntax
to memory [size]
Context
config>log>log-id
Description
This command instructs the events selected for the log ID to be directed to a memory file. A memory file is a circular buffer. When the file is full, each new entry replaces the oldest entry in the log.
The command is one of the to commands used to specify the log ID destination. A to command is mandatory when configuring a log destination.
The source of the data stream must be specified in the from command before configuring the destination with the to command.
The to command can only be set once. It cannot be modified or re-entered. If the log destination needs to be changed or if the maximum size of an SNMP log or memory log needs to be modified, the log ID must be removed and then recreated.
Default
No destination is specified
Parameters
- size
indicates the number of events that can be stored in the memory log
to session
Syntax
to session
Context
config>log>log-id
Description
This command instructs the events selected for the log ID to be directed to the current console or Telnet session. This command is only valid for the duration of the session. When the session is terminated, the to session configuration is removed. A log ID with a session destination is saved in the configuration file but the to session part of the configuration is not stored.
The command is one of the to commands used to specify the log ID destination. A to command is mandatory when configuring a log destination.
The source of the data stream must be specified in the from command before configuring the destination with the to command.
The to command can only be set once. It cannot be modified or re-entered. If the log destination needs to be changed or if the maximum size of an SNMP log or memory log needs to be modified, the log ID must be removed and then recreated.
Default
No destination is specified
to snmp
Syntax
to snmp [size]
Context
config>log>log-id
Description
This command instructs the alarms and traps to be directed to the snmp-trap-group associated with the log-id.
A local circular memory log is always maintained for SNMP notifications sent to the specified snmp-trap-group for the log-id.
The command is one of the to commands used to specify the log ID destination. A to command is mandatory when configuring a log destination.
The source of the data stream must be specified in the from command before configuring the destination with the to command.
The to command can only be set once. It cannot be modified or re-entered. If the log destination needs to be changed or if the maximum size of an SNMP log or memory log needs to be modified, the log ID must be removed and then recreated.
Default
No destination is specified
Parameters
- size
defines the number of events stored in this memory log
to syslog
Syntax
to syslog syslog-id
Context
config>log>log-id
Description
This command instructs the alarms and traps to be directed to a specified syslog. To remain consistent with the standards governing syslog, messages to syslog are truncated to 1 kbyte.
The command is one of the to commands used to specify the log ID destination. A to command is mandatory when configuring a log destination.
The source of the data stream must be specified in the from command before configuring the destination with the to command.
The to command can only be set once. It cannot be modified or re-entered. If the log destination needs to be changed or if the maximum size of an SNMP log or memory log needs to be modified, the log ID must be removed and then recreated.
Default
No destination is specified
Parameters
- syslog-id
instructs the events selected for the log ID to be directed to the syslog-id. The characteristics of the syslog-id referenced here must have been defined in the config>log>syslog syslog-id context.
time-format
Syntax
time-format {local | utc}
Context
config>log>log-id
Description
This command specifies whether the time should be displayed in local or Coordinated Universal Time (UTC) format.
Default
utc
Parameters
- local
specifies that timestamps are written in the system's local time
- utc
specifies that timestamps are written using the UTC value. This was formerly called Greenwich Mean Time (GMT) and Zulu time.
SNMP trap group commands
snmp-trap-group
Syntax
[no] snmp-trap-group log-id
Context
config>log
Description
This command enables the context to configure a group of SNMP trap receivers and their operational parameters for a specified log-id.
A trap group specifies the types of SNMP traps and specifies the log ID that will receive the group of SNMP traps. A trap group must be configured in order for SNMP traps to be sent.
To suppress the generation of all alarms and traps, see the event-control command. To suppress alarms and traps that are sent to this log-id, see the filter (log destination) command. When alarms and traps are generated, they can be directed to one or more SNMP trap groups. Logger events that can be forwarded as SNMP traps are always defined on the main event source.
The no form of the command deletes the SNMP trap group.
Default
There are no default SNMP trap groups.
Parameters
- log-id
the log ID value of a log configured in the to snmp context. Alarms and traps cannot be sent to the trap receivers until a valid log-id exists.
trap-target
Syntax
trap-target name address ip-address [port port] [snmpv1 | snmpv2c | snmpv3] notify-community {communityName | snmpv3SecurityName} [security-level {no-auth-no-privacy | auth-no-privacy | privacy}]
no trap-targetname
Context
config>log>snmp-trap-group
Description
This command adds or modifies a trap receiver and configures the operational parameters for the trap receiver. A trap reports significant events that occur on a 7705 SAR, such as errors or failures.
Before an SNMP trap can be issued to a trap receiver, the to console, snmp-trap-group, and at least one trap-target must be configured.
The trap-target command is used to add or remove a trap receiver from an snmp-trap-group. The operational parameters specified in the command include:
the IP address of the trap receiver
the UDP port used to send the SNMP trap
SNMP version
SNMP community name for SNMPv1 and SNMPv2c receivers
security name and level for SNMPv3 trap receivers
A single snmp-trap-group log-id can have multiple trap receivers. Each trap receiver can have different operational parameters.
An address can be configured as a trap receiver more than once as long as a different port is used for each instance.
To prevent resource limitations, only configure a maximum of 10 trap receivers.
The no form of the command removes the SNMP trap receiver from the SNMP trap group.
Default
No SNMP trap targets are defined.
Parameters
- name
specifies the name of the trap target, up to 28 characters in length
- ip-address
the IP address of the trap receiver. Only one IP address destination can be specified per trap destination group.
- port
the destination UDP port used for sending traps to the destination, expressed as a decimal integer. Only one port can be specified per trap-target statement. If multiple traps need to be issued to the same address, multiple ports must be configured.
- snmpv1 | snmpv2c | snmpv3
specifies the SNMP version format to use for traps sent to the trap receiver
- notify-community communityName | snmpv3SecurityName
specifies the community string for snmpv1 or snmpv2c, or the snmpv3 security-name. If no notify-community parameter is configured, then no alarms or traps are issued for the trap destination. If the SNMP version is modified, the notify-community parameter must be changed to the correct form for the SNMP version.
- security-level {no-auth-no-privacy | auth-no-privacy | privacy}
specifies the required authentication and privacy levels required to access the views configured on this node when configuring an snmpv3 trap receiver.
Show commands
accounting-policy
Syntax
accounting-policy [acct-policy-id] [access | network] [associations]
Context
show>log
Description
This command displays accounting policy information.
Parameters
- acct-policy-id
-
the policy ID that uniquely identifies the accounting policy, expressed as a decimal integer
- access
-
only displays access accounting policies
- network
-
only displays network accounting policies
- associations
-
only displays accounting policy associations
Output
The following output is an example of accounting policy information, and Accounting policy field descriptions describes the fields.
Output exampleA:ALU-1# show log accounting-policy
==============================================================================
Accounting Policies
==============================================================================
Policy Type Def Admin Oper Intvl File Record Name
Id State State Id
------------------------------------------------------------------------------
1 access No Up Up 15 1 service-ingress-packets
2 access Yes Up Up 15 2 service-ingress-octets
==============================================================================
A:ALU-1#
A:ALU-1# show log accounting-policy 10
==============================================================================
Accounting Policies
==============================================================================
Policy Type Def Admin Oper Intvl File Record Name
Id State State Id
------------------------------------------------------------------------------
10 access Yes Up Up 5 3 service-ingress-packets
Description : (Not Specified)
Data Loss Count : 0 Data Loss TimeStamp: N/A
This policy is applied to:
Svc Id: 100 SAP : 1/1/8:0 Collect-Stats
Svc Id: 101 SAP : 1/1/8:1 Collect-Stats
Svc Id: 102 SAP : 1/1/8:2 Collect-Stats
Svc Id: 106 SAP : 1/1/8:6 Collect-Stats
Svc Id: 107 SAP : 1/1/8:7 Collect-Stats
Svc Id: 108 SAP : 1/1/8:8 Collect-Stats
Svc Id: 109 SAP : 1/1/8:9 Collect-Stats
...
==============================================================================
A:ALU-1#
A:ALU-1# show log accounting-policy access
==============================================================================
Accounting Policies
==============================================================================
Policy Type Def Admin Oper Intvl File Record Name
Id State State Id
------------------------------------------------------------------------------
10 access Yes Up Up 5 3 service-ingress-packets
==============================================================================
A:ALU-1#
|
Label |
Description |
|---|---|
|
Policy ID |
The identifying value assigned to a specific policy |
|
Type |
Identifies the accounting policy type forwarded to the configured accounting file |
|
access: indicates that the policy is an access accounting policy |
|
|
network: indicates that the policy is a network accounting policy |
|
|
none: indicates no accounting policy types assigned |
|
|
Def |
Yes: indicates that the policy is a default policy |
|
No: indicates that the policy is not a default policy |
|
|
Admin State |
Displays the administrative state of the policy |
|
Up: indicates that the policy is administratively enabled |
|
|
Down: indicates that the policy is administratively disabled |
|
|
Oper State |
Displays the operational state of the policy |
|
Up: indicates that the policy is operationally up |
|
|
Down: indicates that the policy is operationally down |
|
|
Intvl |
Displays the interval, in minutes, in which statistics are collected and written to their destination. The default depends on the record name type. |
|
File ID |
The log destination |
|
Record Name |
The accounting record name that represents the configured record type |
|
Description |
The description of the accounting policy |
|
Data Loss Count |
The number of times a statistics data loss has occurred |
|
Data Loss Timestamp |
The timestamp of the last data loss occurrence. If there are no losses, the timestamp is N/A. |
|
This policy is applied to |
Specifies the entities that the accounting policy is applied to |
accounting-records
Syntax
accounting-records
Context
show>log
Description
This command displays accounting policy record names.
Output
The following output is an example of accounting policy record information, and Accounting records field descriptions describes the fields.
Output exampleA: ALU-1# show log accounting-records
==========================================================
Accounting Policy Records
==========================================================
Record # Record Name Def. Interval
----------------------------------------------------------
1 service-ingress-octets 5
2 service-egress-octets 5
3 service-ingress-packets 5
4 service-egress-packets 5
5 network-ingress-octets 15
6 network-egress-octets 15
7 network-ingress-packets 15
8 network-egress-packets 15
11 combined-network-ing-egr-octets 15
12 combined-service-ing-egr-octets 5
13 complete-service-ingress-egress 5
32 saa 5
54 complete-network-ing-egr 15
==========================================================
A:ALU-1#
|
Label |
Description |
|---|---|
|
Record # |
The record ID that uniquely identifies the accounting policy, expressed as a decimal integer |
|
Record Name |
The accounting record name |
|
Def. Interval |
The default interval, in minutes, in which statistics are collected and written to their destination |
applications
Syntax
applications
Context
show>log
Description
This command displays a list of all application names that can be used in event-control and filter commands.
Output
The following output is an example of an application list (not all applications apply to the 7705 SAR).
Output exampleA:ALU-1# show log applications
==================================
Log Event Application Names
==================================
Application Name
----------------------------------
APS
ATM
BFD
BGP
CHASSIS
CPMHWFILTER
DEBUG
DHCP
DHCPS
DOT1X
EFM_OAM
ERING
ETH_CFM
FILTER
FIREWALL
FR
IGMP
IGMP_SNOOPING
IP
IPSEC
IPSEC_CPM
ISIS
LAG
LDP
LLDP
LOGGER
MCPATH
MC_REDUNDANCY
MIRROR
MLD
MLD_SNOOPING
MPLS
MWMGR
NGE
NTP
OAM
OSPF
PIM
PIM_SNOOPING
PORT
PPP
PTP
QOS
RADIUS
RIP
RIP_NG
ROUTE_NEXT_HOP
ROUTE_POLICY
RSVP
SCADA
SECURITY
SNMP
STP
SUB_HOST_TRK
SVCMGR
SYSTEM
TIP
TSS
USER
VRRP
VRTR
==================================
A:ALU-1#
event-control
Syntax
event-control [application-id [event-name | event-number]]
event-control application-id event-namedetail
Context
show>log
Description
This command displays event control settings for events, including whether the event is suppressed or generated, and the severity level for the event.
If no options are specified, all events, alarms, and traps are listed.
Parameters
- application-id
-
displays event control for the specified application
- event-name
-
displays event control for the named application event
- event-number
-
displays event control for the specified application event number
- detail
-
displays detailed event-control information
Output
The following output is an example of event control information, and Event control field descriptions describes the fields. Because the output is very large, only a sample of the events are shown here.
Output exampleA:gal171# show log event-control
=======================================================================
Log Events
=======================================================================
Application
ID# Event Name P g/s Logged Dropped
-----------------------------------------------------------------------
ATM:
2004 tAtmTcSubLayerDown MI gen 0 0
2005 tAtmTcSubLayerClear MI gen 0 0
L 2006 atmVclStatusChange WA gen 0 0
...
CHASSIS:
2001 cardFailure MA gen 4 0
2002 cardInserted MI gen 3 0
2003 cardRemoved MI gen 8 0
2004 cardWrong MI gen 0 0
2005 EnvTemperatureTooHigh MA gen 0 0
2007 powerSupplyOverTemp CR gen 0 0
2008 powerSupplyAcFailure CR gen 0 0
2009 powerSupplyDcFailure CR gen 0 0
2010 powerSupplyInserted MA gen 0 0
2011 powerSupplyRemoved MA gen 0 0
2012 redPrimaryCPMFail CR gen 0 0
2016 clearNotification MA gen 0 0
2017 syncIfTimingHoldover CR gen 0 0
2018 syncIfTimingHoldoverClear CR gen 0 0
2019 syncIfTimingRef1Alarm MI gen 0 0
2020 syncIfTimingRef1AlarmClear MI gen 0 0
2021 syncIfTimingRef2Alarm MI gen 0 0
2022 syncIfTimingRef2AlarmClear MI gen 0 0
2023 flashDataLoss MA gen 0 0
2024 flashDiskFull MA gen 0 0
2025 softwareMismatch MA gen 0 0
2026 softwareLoadFailed MA gen 0 0
2027 bootloaderMismatch MA gen 0 0
2028 bootromMismatch MA gen 0 0
2029 fpgaMismatch MA gen 0 0
2030 syncIfTimingBITSAlarm MI gen 0 0
2031 syncIfTimingBITSAlarmClear MI gen 0 0
2032 cardUpgraded MA gen 0 0
2033 cardUpgradeInProgress MA gen 0 0
2034 cardUpgradeComplete MA gen 0 0
2050 powerSupplyInputFailure CR gen 0 0
2051 powerSupplyOutputFailure CR gen 0 0
2052 mdaHiBwMulticastAlarm MI gen 0 0
2056 mdaCfgNotCompatible MA gen 0 0
2057 extAlarmInput1Detected CR gen 0 0
2058 extAlarmInput2Detected MA gen 0 0
2059 extAlarmInput3Detected MA gen 0 0
2060 extAlarmInput4Detected MI gen 0 0
2061 extAlarmCleared MA gen 0 0
2062 syncIfTimingExternAlarm MI gen 0 0
2063 syncIfTimingExternAlarmClear MI gen 0 0
2064 cardBgDiagsFault MI gen 0 0
2065 fanCriticalFailure CR gen 0 0
2066 fanMinorFailure MI gen 0 0
2067 cardSyncFileNotPresent MI gen 0 0
2058 tmnxEqMdaXplError MI sup 0 0
...
DEBUG:
L 2001 traceEvent MI gen 0 0
DOT1AG:
2001 dot1agCfmFaultAlarm MI gen 0 0
EFM_OAM:
2001 tmnxDot3OamPeerChanged MI gen 0 0
2002 tmnxDot3OamLoopDetected MI gen 0 0
2003 tmnxDot3OamLoopCleared MI gen 0 0
FILTER:
2001 tIPFilterPBRPacketsDrop WA gen 0 0
2002 tFilterEntryActivationFailed WA gen 0 0
2003 tFilterEntryActivationRestored WA gen 0 0
IP:
L 2001 clearRTMError MI gen 0 0
L 2002 ipEtherBroadcast MI gen 0 0
L 2003 ipDuplicateAddress MI gen 0 0
L 2004 ipArpInfoOverwritten MI gen 0 0
L 2005 fibAddFailed MA gen 0 0
L 2006 qosNetworkPolicyMallocFailed MA gen 0 0
L 2007 ipArpBadInterface MI gen 0 0
L 2008 ipArpDuplicateIpAddress MI gen 0 0
L 2009 ipArpDuplicateMacAddress MI gen 0 0
....
....
USER:
L 2001 cli_user_login MI gen 2 0
L 2002 cli_user_logout MI gen 1 0
L 2003 cli_user_login_failed MI gen 0 0
L 2004 cli_user_login_max_attempts MI gen 0 0
L 2005 ftp_user_login MI gen 0 0
L 2006 ftp_user_logout MI gen 0 0
L 2007 ftp_user_login_failed MI gen 0 0
L 2008 ftp_user_login_max_attempts MI gen 0 0
L 2009 cli_user_io MI sup 0 48
L 2010 snmp_user_set MI sup 0 0
L 2011 cli_config_io MI gen 4357 0
=======================================================================
A:ALU-1#
|
Label |
Description |
|---|---|
|
Application |
The application name |
|
ID# |
The event ID number within the application L ID#: an "L" in front of an ID represents event types that do not generate an associated SNMP notification. Most events generate a notification; only the exceptions are marked with a preceding "L". |
|
Event Name |
The event name |
|
P |
CL: the event has a cleared severity/priority |
|
CR: the event has critical severity/priority |
|
|
IN: the event has indeterminate severity/priority |
|
|
MA: the event has major severity/priority |
|
|
MI: the event has minor severity/priority |
|
|
WA: the event has warning severity/priority |
|
|
g/s |
gen: the event is generated/logged by event control |
|
sup: the event is suppressed/dropped by event control |
|
|
thr: specifies that throttling is enabled |
|
|
Logged |
The number of events logged/generated |
|
Dropped |
The number of events dropped/suppressed |
event-handling
Syntax
event-handling
Context
show>log
Description
This command enables the context to display Event Handling System (EHS) information.
handler
Syntax
handler [handler-name]
handler detail
Context
show>log>event-handling
Description
This command displays event handler information.
Parameters
- handler-name
-
specifies an event handler name
- detail
-
displays detailed information for all event handlers
Output
The following is an example of event handler information, and Event handler field descriptions describes the fields.
Output exampleA:7705:Dut-C# show log event-handling handler "handler_1"
===============================================================================
Event Handling System - Handlers
===============================================================================
===============================================================================
Handler : handler_1
===============================================================================
Description : test_handler
Admin State : up Oper State : up
-------------------------------------------------------------------------------
Handler Execution Statistics
Success : 1
Err No Entry : 0
Err Adm Status : 0
Total : 1
-------------------------------------------------------------------------------
Handler Action-List Entry
-------------------------------------------------------------------------------
-------------------------------------------------------------------------------
Entry-id : 1
Description : test_entry
Admin State : up Oper State : up
Script
Policy Name : script_policy_1
Policy Owner : TiMOS CLI
Min Delay : 0
Last Exec : 05/24/2018 19:03:31
-------------------------------------------------------------------------------
Handler Action-List Entry Execution Statistics
Success : 1
Err Mn Delay : 0
Err Launch : 0
Err Adm Status : 0
Total : 1
===============================================================================
|
Label |
Description |
|---|---|
|
Handler |
The name of the event handler |
|
Description |
The event handler description string |
|
Admin State |
The administrative state of the event handler |
|
Oper State |
The operational state of the event handler |
|
Handler Execution Statistics |
|
|
Success |
The number of times that the event handler was successfully triggered |
|
Err No Entry |
The number of times that the event handler failed to trigger due to no action-list entry |
|
Err Adm Status |
The number of times that the event handler was not executed because the entry was administratively disabled |
|
Total |
The total number of times that the event handler attempted execution |
|
Handler Action-List Entry |
|
|
Entry-id |
The action-list entry identifier |
|
Description |
The action-list entry description string |
|
Admin State |
The administrative state of the action-list entry |
|
Oper State |
The operational state of the action-list entry |
|
Script |
|
|
Policy Name |
The name of the related script policy |
|
Policy Owner |
The owner of the related script policy |
|
Min Delay |
The configured minimum delay time between subsequent executions of the action specified in the entry |
|
Last Exec |
The timestamp of the last successful execution of the action-list entry |
|
Handler Action-List Entry Execution Statistics |
|
|
Success |
The number of times that the action-list entry was successfully queued to run. For a script-policy entry, this indicates that the script request has been enqueued but does not necessarily indicate that the script has successfully launched or completed. |
|
Err Mn Delay |
The number of times that the action-list entry attempted to execute before the minimum delay time expired |
|
Err Launch |
The number of times that the action-list entry was not successfully queued to run. This could be caused by a number of conditions, including a full script request input queue. |
|
Err Adm Status |
The number of times that the action-list entry was not executed because the entry was administratively disabled |
|
Total |
The total number of times that the action-list entry attempted execution |
information
Syntax
information
Context
show>log>event-handling
Description
This command displays general information about EHS, as well as handler and trigger statistics.
Output
The following is an example of EHS information.
Output exampleA:7705:Dut-C# show log event-handling information
===============================================================================
Event Handling System - Event Trigger Statistics
===============================================================================
_______________________________________________________________________________
Application Name
Event Id Total Success ErrNoEntry AdmStatus
-------------------------------------------------------------------------------
OAM
2001 0 0 0 0
-----------------------------------------------------------------------------
Entry FilMatch Trigger Debounce FilFail ErrAdmSta ErrFilter ErrHandler
-----------------------------------------------------------------------------
1 0 0 0 0 0 0 0
10 0 0 0 0 0 0 0
-----------------------------------------------------------------------------
SUM 0 0 0 0 0 0 0
_______________________________________________________________________________
Application Name
Event Id Total Success ErrNoEntry AdmStatus
-------------------------------------------------------------------------------
OAM
2004 0 0 0 0
-----------------------------------------------------------------------------
Entry FilMatch Trigger Debounce FilFail ErrAdmSta ErrFilter ErrHandler
-----------------------------------------------------------------------------
1 0 0 0 0 0 0 0
-----------------------------------------------------------------------------
SUM 0 0 0 0 0 0 0
===============================================================================
EVENTS PROCESSED Total Success ErrNoEntry AdmStatus
-------------------------------------------------------------------------------
0 0 0 0
===============================================================================
===============================================================================
Event Handling System - Event Handler Statistics
===============================================================================
_______________________________________________________________________________
Handler Total Success ErrNoEntry AdmStatus
handler_1 0 0 0 0
-----------------------------------------------------------------------------
Entry Id Launch MinDelay ErrLaunch ErrAdmSta
-----------------------------------------------------------------------------
1 0 0 0 0
-----------------------------------------------------------------------------
SUMMARY 0 0 0 0
===============================================================================
HANDLERS SUMMARY Total Success ErrNoEntry AdmStatus
-------------------------------------------------------------------------------
0 0 0 0
===============================================================================
scripts
Syntax
scripts
Context
show>log>event-handling
Description
This command displays handler configuration and script run queue information.
Output
The following is an example of script information.
Output exampleA:7705:Dut-C# show log event-handling scripts
===============================================================================
Event Handling System - Script Policy Association
===============================================================================
-------------------------------------------------------------------------------
No Matching Entries Found
===============================================================================
===============================================================================
Event Handling System - Script Association
===============================================================================
-------------------------------------------------------------------------------
No Matching Entries Found
===============================================================================
===============================================================================
Event Handling System - Script Launched List
===============================================================================
Run # Script owner Script name Script state
-------------------------------------------------------------------------------
No Matching Entries
===============================================================================
event-parameters
Syntax
event-parameters [application-id [event-name | event-number]]
Context
show>log
Description
This command displays the common parameters and specific parameters of log event or of all log events. This display lets a user know what parameters can be passed from a triggering event to the triggered EHS script.
Parameters
- application-id
-
displays event parameters for the specified application
- event-name
-
displays event parameters for the named application event
- event-number
-
displays event parameters for the specified application event number
Output
The following is an example of log event parameter information.
Output example# show log event-parameters "oam" 2001
=======================================================================
Common Event Parameters
appid
name
eventid
severity
subject
gentime
Event Specific Parameters
tmnxOamPingCtlOwnerIndex
tmnxOamPingCtlTestIndex
tmnxOamPingCtlTgtAddrType
tmnxOamPingCtlTgtAddress
tmnxOamPingResultsTestRunIndex
tmnxOamPingResultsOperStatus
tmnxOamPingResultsMinRtt
tmnxOamPingResultsMaxRtt
tmnxOamPingResultsAverageRtt
tmnxOamPingResultsRttSumOfSquares
tmnxOamPingResultsRttOFSumSquares
tmnxOamPingResultsMtuResponseSize
tmnxOamPingResultsSvcPing
tmnxOamPingResultsProbeResponses
tmnxOamPingResultsSentProbes
tmnxOamPingResultsLastGoodProbe
tmnxOamPingCtlTestMode
tmnxOamPingHistoryIndex
=======================================================================
file-id
Syntax
file-id [log-file-id]
Context
show>log
Description
This command displays event log file information.
If no command line parameters are specified, a summary output of all event log files is displayed.
Specifying a file ID displays detailed information for the event log file.
Parameters
- log-file-id
-
displays detailed information for the specified event log file
Output
The following output is an example of event log file information, and Log file summary field descriptions describes the fields.
Output exampleA:ALU-1# show log file-id
=============================================================
File Id List
=============================================================
file-id rollover retention admin backup oper
location location location
-------------------------------------------------------------
1 60 4 cf3: none none
2 60 3 cf3: none none
3 1440 12 cf3: none none
10 1440 12 cf3: none none
11 1440 12 cf3: none none
15 1440 12 cf3: none none
20 1440 12 cf3: none none
=============================================================
A:ALU-1#
A:ALU-1# show log file-id 10
=============================================================
File Id List
=============================================================
file-id rollover retention admin backup oper
location location location
-------------------------------------------------------------
10 1440 12 cf3: none none
Description : Main
=============================================================
===============================================================
File Id 10 Location cf3:
===============================================================
file name expired state
---------------------------------------------------------------
cf3:\log\log0302-20060501-012205 yes complete
cf3:\log\log0302-20060501-014049 yes complete
cf3:\log\log0302-20060501-015344 yes complete
cf3:\log\log0302-20060501-015547 yes in progress
=============================================================
|
Label |
Description |
|---|---|
|
file-id |
The log file ID |
|
rollover |
The rollover time for the log file, which is the amount of time before the file is partitioned into a new file. |
|
retention |
The retention time for the file in the system, which is how long the file should be retained in the file system |
|
admin location |
The flash device specified for the file location |
|
none: indicates no specific flash device was specified |
|
|
backup location |
The backup compact flash device specified for the file location |
|
oper location |
The actual flash device on which the log file exists |
|
file name |
The complete pathname of the file associated with the log ID |
|
expired |
Indicates whether the retention period for this file has passed |
|
state |
in progress: indicates the current open log file |
|
complete: indicates the old log file |
filter-id
Syntax
filter-id [filter-id]
Context
show>log
Description
This command displays event log filter policy information. If you specify a filter ID, the command also displays the filter match criteria.
Parameters
- filter-id
-
displays detailed information for the specified event filter policy ID
Output
The following outputs are examples of event log filter policy information:
-
filter ID summary information (Output example, Filter ID summary field descriptions)
-
filter ID information with match criteria specified (Output example, Filter ID match criteria field descriptions )
*A:ALU-48>config>log# show log filter-id
=============================================================================
Log Filters
=============================================================================
Filter Applied Default Description
Id Action
-----------------------------------------------------------------------------
1 no forward
5 no forward
10 no forward
1001 yes drop Collect events for Serious Errors Log
=============================================================================
*A:ALU-48>config>log#
|
Label |
Description |
|---|---|
|
Filter Id |
The event log filter ID |
|
Applied |
no: the event log filter is not currently in use by a log ID |
|
yes: the event log filter is currently in use by a log ID |
|
|
Default Action |
drop: the default action for the event log filter is to drop events not matching filter entries |
|
forward: the default action for the event log filter is to forward events not matching filter entries |
|
|
Description |
The description string for the filter ID |
*A:ALU-48>config>log# show log filter-id 1001
==========================================================================
Log Filter
==========================================================================
Filter-id : 1001 Applied : yes Default Action: drop
Description : Collect events for Serious Errors Log
--------------------------------------------------------------------------
Log Filter Match Criteria
--------------------------------------------------------------------------
Entry-id : 10 Action : forward
Application : Operator : off
Event Number : 0 Operator : off
Severity : major Operator : greaterThanOrEqual
Subject : Operator : off
Match Type : exact string :
Router : Operator : off
Match Type : exact string :
Description : Collect only events of major severity or higher
--------------------------------------------------------------------------
==========================================================================
|
Label |
Description |
|---|---|
|
Entry-id |
The event log filter entry ID |
|
Action |
default: there is no explicit action for the event log filter entry and the filter's default action is used on matching events |
|
drop: the action for the event log filter entry is to drop matching events |
|
|
forward: the action for the event log filter entry is to forward matching events |
|
|
Description: (Entry-id) |
The description string for the event log filter entry |
|
Application |
The event log filter entry application match criterion |
|
Event Number |
The event log filter event ID match criterion |
|
Severity |
cleared: the event log filter severity match is cleared |
|
indeterminate: the event log filter entry application event severity indeterminate match criterion |
|
|
critical: the event log filter entry application event severity critical match criterion |
|
|
major: the event log filter entry application event severity cleared match criterion |
|
|
minor: the event log filter entry application event severity minor match criterion |
|
|
warning: the event log filter entry application event severity warning match criterion |
|
|
Subject |
Displays the event log filter entry subject string match criterion |
|
Router |
Displays the event log filter entry router router-instance string match criterion |
|
Operator: |
There is an operator field for each match criteria: application, event number, severity, and subject |
|
equal: matches when equal to the match criterion |
|
|
greaterThan: matches when greater than the match criterion |
|
|
greaterThanOrEqual: matches when greater than or equal to the match criterion |
|
|
lessThan: matches when less than the match criterion |
|
|
lessThanOrEqual: matches when less than or equal to the match criterion |
|
|
notEqual: matches when not equal to the match criterion |
|
|
off: no operator specified for the match criterion |
log-collector
Syntax
log-collector
Context
show>log
Description
This command displays log collector statistics for the main, security, change and debug log collectors.
Output
The following output is an example of log collector statistics, and Log collector field descriptions describes the fields.
Output exampleA:ALU-1# show log log-collector
===============================================================================
Log Collectors
===============================================================================
Main Logged : 1224 Dropped : 0
Dest Log Id: 99 Filter Id: 0 Status: enabled Dest Type: memory
Dest Log Id: 100 Filter Id: 1001 Status: enabled Dest Type: memory
Security Logged : 3 Dropped : 0
Change Logged : 3896 Dropped : 0
Debug Logged : 0 Dropped : 0
===============================================================================
A:ALU-1#
|
Label |
Description |
|---|---|
|
<Collector Name> |
Main: the main event stream contains the events that are not explicitly directed to any other event stream |
|
Security: the security stream contains all events that affect attempts to breach system security, such as failed login attempts, attempts to access MIB tables to which the user is not granted access or attempts to enter a branch of the CLI to which access has not been granted |
|
|
Change: the change event stream contains all events that directly affect the configuration or operation of this node |
|
|
Debug: the debug-trace stream contains all messages in the debug stream |
|
|
Dest. Log ID |
Specifies the event log stream destination |
|
Filter ID |
The value is the index to the entry that defines the filter to be applied to this log's source event stream to limit the events output to this log's destination. If the value is 0, then all events in the source log are forwarded to the destination. |
|
Status |
Enabled: logging is enabled |
|
Disabled: logging is disabled |
|
|
Dest. Type: |
Console: a log created with the console type destination displays events to the physical console device Events are displayed to the console screen whether a user is logged in to the console or not. A user logged in to the console device or connected to the CLI via a remote Telnet or SSH session can also create a log with a destination type of 'session'. Events are displayed to the session device until the user logs off. When the user logs off, the 'session' type log is deleted. |
|
Syslog: all selected log events are sent to the syslog address |
|
|
SNMP traps: events defined as SNMP traps are sent to the configured SNMP trap destinations and are logged in NOTIFICATION-LOG-MIB tables |
|
|
File: all selected log events are directed to a file on the CSM's compact flash disk |
|
|
Memory: all selected log events are directed to an in-memory storage area |
log-id
Syntax
log-id [log-id][severity severity-level] [application application] [sequence from-seq [to-seq]] [count count] [router router-instance [expression]] [subject subject [regexp]] [ascending | descending]
Context
show>log
Description
This command displays an event log summary with settings and statistics or the contents of a specific log file, SNMP log, or memory log.
If the command is specified with no command line options, a summary of the defined system logs is displayed. The summary includes log settings and statistics.
If the log ID of a memory, SNMP, or file event log is specified, the command displays the contents of the log. Additional command line options control what and how the contents are displayed.
Contents of logs with console, session or syslog destinations cannot be displayed. The actual events can only be viewed on the receiving syslog or console device.
Parameters
- log-id
-
displays the contents of the specified log file or memory log ID. The log ID must have a destination of an SNMP or log file or a memory log for this parameter to be used.
- severity-level
-
displays only events with the specified and higher severity
- application
-
displays only events generated by the specified application
- from-seq [to-seq]
-
displays the log entry numbers from a particular entry sequence number (from-seq) to another sequence number (to-seq). The to-seq value must be larger than the from-seq value.
If the to-seq number is not provided, the log contents to the end of the log are displayed unless the count parameter is present, in which case the number of entries displayed is limited by the count.
- count
-
limits the number of log entries displayed to the number specified
- router-instance
-
specifies a router name up to 32 characters to be used in the display criteria
- expression
-
specifies to use a regular expression as match criteria for the router instance string
- subject
-
displays only log entries matching the specified text subject string. The subject is the object affected by the event; for example, the port-id would be the subject for a link-up or link-down event.
- regexp
-
specifies to use a regular expression as parameters with the specified subject string
- ascending | descending
-
specifies the log sort direction. Logs are normally shown from the newest entry to the oldest in descending sequence number order on the screen. When using the ascending parameter, the log will be shown from the oldest to the newest entry.
Output
The following output is an example of event log summary information, and Log ID field descriptions describes the fields.
Output exampleA:ALU-1# show log log-id
=====================================================================
Event Logs
=====================================================================
Log Source Filter Admin Oper Logged Dropped Dest Dest Size
Id Id State State Type Id
--------------------------------------------------------------------
1 none none up down 52 0 file 10 N/A
2 C none up up 41 0 syslog 1 N/A
99 M none up up 2135 0 memory 500
=====================================================================
A:ALU-1#
|
Label |
Description |
|---|---|
|
Log Id |
An event log destination |
|
Source |
no: the event log filter is not currently in use by a log ID |
|
yes: the event log filter is currently in use by a log ID |
|
|
M: the event source for the log ID is the Main event category |
|
|
C: the event source for the log ID is the Change event category |
|
|
none: the event log filter is currently in use by a log ID |
|
|
Filter ID |
The value is the index to the entry that defines the filter to be applied to this log's source event stream to limit the events output to this log's destination. If the value is 0, then all events in the source log are forwarded to the destination. |
|
Admin State |
Up: indicates that the administrative state is up |
|
Down: indicates that the administrative state is down |
|
|
Oper State |
Up: indicates that the operational state is up |
|
Down: indicates that the operational state is down |
|
|
Logged |
The number of events that have been sent to the log sources that were forwarded to the log destination |
|
Dropped |
The number of events that have been sent to the log sources that were not forwarded to the log destination because they were filtered out by the log filter |
|
Dest. Type |
Console: all selected log events are directed to the system console. If the console is not connected, then all entries are dropped. |
|
Syslog: all selected log events are sent to the syslog address |
|
|
SNMP traps: events defined as SNMP traps are sent to the configured SNMP trap destinations and are logged in NOTIFICATION-LOG-MIB tables |
|
|
File: all selected log events are directed to a file on the CSM's compact flash disk |
|
|
Memory: all selected log events are directed to an in-memory storage area |
|
|
Dest ID |
The event log stream destination |
|
Size |
The allocated memory size for the log |
A:gal171# show log log-id 99
===============================================================================
Event Log 99
===============================================================================
Description : Default System Log
Memory Log contents [size=500 next event=3722 (wrapped)]
3721 2008/02/07 09:14:06.69 UTC WARNING: SYSTEM #2006 Base LOGGER
"Log File Id 2 configuration modified"
3720 2008/02/07 09:13:18.86 UTC WARNING: SYSTEM #2006 Base LOGGER
"Log File Id 2 configuration modified"
3719 2008/02/01 11:54:15.67 UTC MINOR: IP #2004 management PIP MANAGEMENT
"ARP information overwritten for 10.120.52.253 by 00:e0:52:d4:a5:00"
3718 2008/02/01 11:54:15.40 UTC MINOR: IP #2004 management PIP MANAGEMENT
"ARP information overwritten for 10.120.52.253 by 00:e0:5e:00:a5:00"
...
===============================================================================
A:gal171
snmp-trap-group
Syntax
snmp-trap-group [log-id]
Context
show>log
Description
This command displays SNMP trap group configuration information.
Parameters
- log-id
-
displays only SNMP trap group information for the specified trap group log ID
Output
The following output is an example of SNMP trap group information, and SNMP trap group field descriptions describes the fields.
Output example*A:ALU-48>config>log# show log snmp-trap-group
===============================================================================
SNMP Trap Groups
===============================================================================
id name
port address
-------------------------------------------------------------------------------
29 name
162 10.20.30.10
===============================================================================
*A:ALU-48>config>log#
*A:ALU-48>config>log# show log snmp-trap-group 90
===============================================================================
SNMP Trap Group 90
===============================================================================
Description : none
-------------------------------------------------------------------------------
Name : 10.121.107.98:162
Address : 10.121.107.98
Port : 162
Version : v2c
Community : private
Sec. Level : none
Replay : disabled
First replay : n/a
Last replay : never
===============================================================================
*A:ALU-48>config>log#
|
Label |
Description |
|---|---|
|
Name |
The log destination ID for an event stream |
|
Address |
The IP address of the trap receiver |
|
Port |
The destination UDP port used for sending traps to the destination, expressed as a decimal integer |
|
Version |
Specifies the SNMP version format to use for traps sent to the trap receiver. Valid values are v1, v2c, and v3. |
|
Community |
The community string required by snmpv1 or snmpv2c trap receivers |
|
Sec. Level |
The required authentication and privacy security levels required to access the views on this node |
|
Replay |
Indicates whether the replay parameter has been configured for the trap-target address: enabled or disabled |
|
First replay |
Indicates the sequence ID of the first missed notification that will be replayed when a route by which the trap-target address can be reached is added to the routing table. If no notifications are waiting to be replayed, this field shows "n/a". |
|
Last replay |
Indicates the last time that missed events were replayed to the trap-target address. If no events have ever been replayed, this field shows "never". |
syslog
Syntax
syslog [syslog-id]
Context
show>log
Description
This command displays syslog event log destination summary information or detailed information for a specific syslog destination.
Parameters
- syslog-id
-
displays detailed information for the specified syslog event log destination
Output
The following output is an example of syslog event log destination summary information, and Syslog field descriptions describes the fields.
Output example*A:ALU-48>config>log# show log syslog
===============================================================================
Syslog Target Hosts
===============================================================================
Id Ip Address Port Sev Level
Below Level Drop Facility Pfx Level
-------------------------------------------------------------------------------
2 unknown 514 info
0 local7 yes
3 unknown 514 info
0 mail yes
===============================================================================
*A:ALU-48>config>log#
*A:ALU-48>config>log# show log syslog 1
===============================================================================
Syslog Target 1
===============================================================================
IP Address : 192.168.15.22
Port : 514
Log-ids : none
Prefix : Sr12
Facility : mail
Severity Level : info
Prefix Level : yes
Below Level Drop : 0
Description : Linux Station Springsteen
===============================================================================
*A:ALU-48>config>log#
|
Label |
Description |
|---|---|
|
Syslog ID |
The syslog ID number for the syslog destination |
|
IP Address |
The IP address of the syslog target host |
|
Port |
The configured UDP port number used when sending syslog messages |
|
Facility |
The facility code for messages sent to the syslog target host |
|
Severity Level |
The syslog message severity level threshold |
|
Below Level Dropped |
A count of messages not sent to the syslog collector target because the severity level of the message was above the configured severity. The higher the level, the lower the severity. |
|
Prefix Present |
Yes: a log prefix was prepended to the syslog message sent to the syslog host |
|
No: a log prefix was not prepended to the syslog message sent to the syslog host |
|
|
Description |
A text description stored in the configuration file for a configuration context |
|
LogPrefix |
The prefix string prepended to the syslog message |
|
Log-id |
Events are directed to this destination |
Clear commands
log-id
Syntax
log-id log-id
Context
clear>log
Description
This command reinitializes or rolls over the specified memory log or log file. Memory logs are reinitialized and cleared of contents. Log files are manually rolled over.
This command is only applicable to event logs that are directed to file destinations and memory destinations.
SNMP, syslog, and console/session logs are not affected by this command.
Parameters
- log-id
-
the event log ID to be reinitialized or rolled over
event-handling
Syntax
event-handling
Context
clear>log
Description
This command enables the context to clear Event Handling System (EHS) information.
handler
Syntax
handler event-handler-name
Context
clear>log>event-handling
Description
This command clears the event-handler statistics for the specified event handler. These statistics are displayed in the show log event-handling handler handler-name output. The command does not clear the global or aggregate event-handling statistics.
Parameters
- event-handler-name
-
the name of the event handler
information
Syntax
information
Context
clear>log>event-handling
Description
This command clears global and aggregate event-handling statistics. These statistics are displayed in the show log event-handling information output.